Cybersecurity experts have reported the emergence of a new variant of the SparkCat malware, found in mobile applications available on both the Apple App Store and Google Play Store. This discovery comes over a year after the initial identification of SparkCat, which targeted mobile operating systems. The malware is designed to surreptitiously scan users’ photo galleries for images containing cryptocurrency wallet recovery phrases, posing a significant threat to mobile security.
Hidden Threat in Common Apps
SparkCat conceals itself within seemingly harmless applications such as enterprise communication tools and food delivery services. This tactic allows it to operate unnoticed while targeting cryptocurrency users, particularly in Asia. According to Russian cybersecurity firm Kaspersky, two infected apps were identified on the App Store and one on the Google Play Store, all primarily focused on Asian markets.
The iOS version of SparkCat differs in its approach by scanning for mnemonic phrases in English, potentially expanding its reach to affect users globally. This broadens the scope of the threat beyond regional boundaries, making international users vulnerable.
Advanced Features in the Android Variant
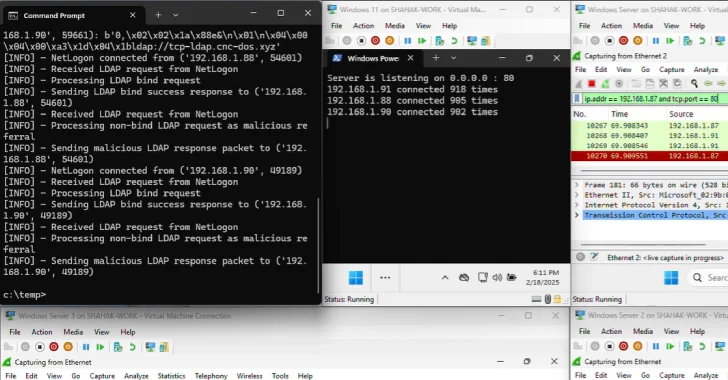
The latest iteration of SparkCat for Android introduces multiple layers of obfuscation, improving its stealth capabilities. This includes techniques such as code virtualization and the use of cross-platform programming languages, complicating efforts to analyze and counter the threat. Additionally, the Android version is tailored to search for keywords in Japanese, Korean, and Chinese, reinforcing its focus on Asian cryptocurrency users.
Initially documented by Kaspersky in February 2025, SparkCat was notable for its use of an optical character recognition (OCR) model to extract images containing recovery phrases from users’ photo libraries and send them to a remote server under the attackers’ control.
Ongoing Threat and Developer Insights
The continual evolution of SparkCat highlights the sophistication and ongoing efforts of its developers. Kaspersky researchers, including Sergey Puzan, emphasize that the updated variant retains the capability to request access to smartphone photo galleries. Utilizing an OCR module, it analyzes text within stored images, sending any with relevant keywords to the attackers. The similarities between current and previous versions suggest the same developers are behind this malware campaign.
This development underscores the critical need for robust security measures on smartphones to protect against diverse cyber threats. Users are advised to employ comprehensive security solutions to safeguard their devices from such evolving threats.