Trivy, a widely used open-source vulnerability scanner by Aqua Security, experienced a security breach for the second time in a month, leading to the hijacking of sensitive CI/CD secrets. This incident affected specific GitHub Actions, ‘aquasecurity/trivy-action’ and ‘aquasecurity/setup-trivy’, which are crucial for scanning Docker container images and configuring workflows.
Details of the Security Breach
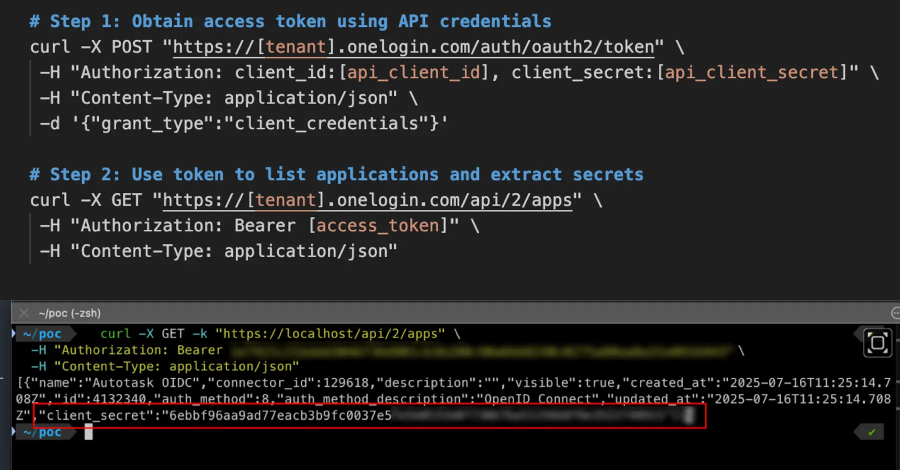
Security researcher Philipp Burckhardt revealed that an attacker forcefully modified 75 out of 76 version tags in the ‘aquasecurity/trivy-action’ repository. These alterations facilitated the distribution of a malicious payload, turning verified version tags into vectors for infostealer malware. The payload was designed to extract critical developer secrets from CI/CD environments, including SSH keys, cloud service credentials, and cryptocurrency wallets.
This breach marks the second supply chain compromise involving Trivy. Earlier, in late February and early March 2026, an autonomous bot named hackerbot-claw exploited a workflow to steal a Personal Access Token (PAT), leading to unauthorized control of the GitHub repository and the release of malicious Visual Studio Code extensions.
Impact and Response
The compromised version (0.69.4) of Trivy was flagged by security researcher Paul McCarty, and it has since been removed. According to reports, the malicious code in version 0.69.4 conducted data theft by scanning for environment variables and credentials, encrypting the data, and sending it to an attacker-controlled server. Persistence was achieved through a systemd service that executed a Python script to retrieve and run the payload.
Itay Shakury, Aqua Security’s vice president of open source, stated that attackers exploited a compromised credential to publish malicious releases. The attackers managed to force-push 75 version tags containing the infostealer payload without creating new releases or branches, leveraging a compromised credential from a previous incident.
Attribution and Mitigation
While the exact perpetrators of the attack remain unidentified, there are indications that the group known as TeamPCP is involved. The credential harvester’s self-identification as ‘TeamPCP Cloud stealer’ supports this theory, aligning with the group’s cloud-native cybercrime activities.
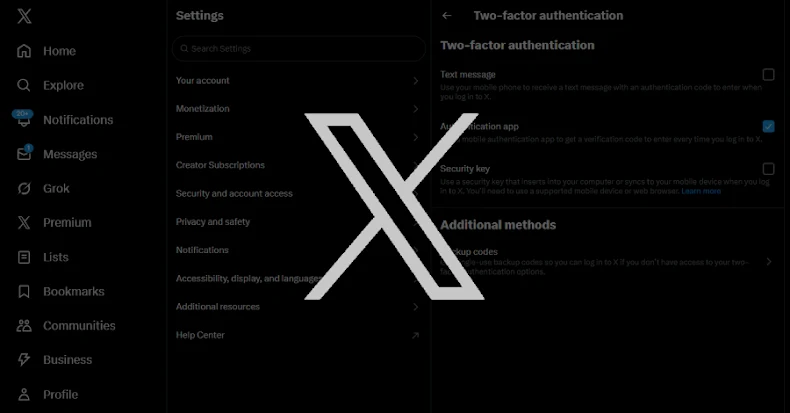
Users are advised to update to the latest secure releases and consider all pipeline secrets compromised if they suspect they were using a compromised version. Additional mitigation measures include blocking the exfiltration domain at the network level and inspecting GitHub accounts for repositories named ‘tpcp-docs’ to identify potential data theft.
Wiz researcher Rami McCarthy recommends pinning GitHub Actions to full SHA hashes instead of version tags, as tags can be redirected to malicious commits. This is an evolving situation, and further updates are forthcoming.