Dec 23, 2025Ravie LakshmananFinancial Crime / Legislation Enforcement
The U.S. Justice Division (DoJ) on Monday introduced the seizure of an internet area and database that it stated was used to additional a legal scheme designed to focus on and defraud Individuals by the use of checking account takeover fraud.
The area in query, web3adspanels[.]org, was used as a backend internet panel to host and manipulate illegally harvested financial institution login credentials. Customers to the web site at the moment are greeted by a seizure banner that claims the area was taken down in a global legislation enforcement operation led by authorities from the U.S. and Estonia.
“The legal group perpetrating the checking account takeover fraud delivered fraudulent ads via serps, together with Google and Bing,” the DoJ stated. “These fraudulent ads imitate the sponsored search engine ads utilized by official banking entities.”
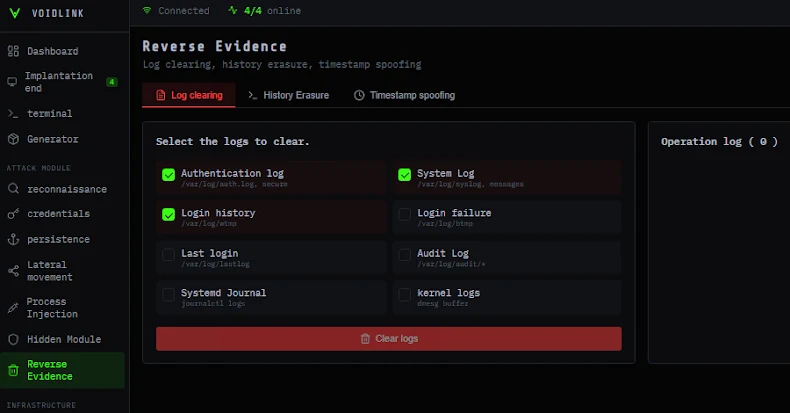
The advertisements served as a conduit to redirect unsuspecting customers to faux financial institution web sites operated by the risk actors, who harvested login credentials entered by victims via an unspecified malicious software program program constructed into the websites. The stolen credentials had been then utilized by the criminals to signal into official financial institution web sites to take over victims’ accounts and drain their funds.
The scheme is estimated to have claimed 19 victims throughout the U.S. so far, together with two firms within the Northern District of Georgia, resulting in tried losses of roughly $28 million and precise losses of roughly $14.6 million.
The DoJ stated the confiscated area saved the stolen login credentials of 1000’s of victims, along with internet hosting a backend server to facilitate takeover fraud as lately as final month.
In response to info shared by the U.S. Federal Bureau of Investigation (FBI), the Web Crime Criticism Heart (IC3) has acquired greater than 5,100 complaints associated to checking account takeover fraud since January 2025, with reported losses upwards of $262 million.
Customers are suggested to train warning when sharing about themselves on-line or on social media; frequently monitor accounts for any monetary irregularities; use distinctive, advanced passwords; make sure the correctness of banking web site URLs earlier than signing in; and keep vigilant towards phishing assaults or suspicious callers.