Dec 03, 2025Ravie LakshmananMalware / Web3 Safety
Cybersecurity researchers have found a malicious Rust bundle that is able to concentrating on Home windows, macOS, and Linux methods, and options malicious performance to stealthily execute on developer machines by masquerading as an Ethereum Digital Machine (EVM) unit helper software.
The Rust crate, named “evm-units,” was uploaded to crates.io in mid-April 2025 by a person named “ablerust,” attracting greater than 7,000 downloads over the previous eight months. One other bundle created by the identical writer, “uniswap-utils,” listed “evm-units” as a dependency. It was downloaded over 7,400 occasions. The packages have since been faraway from the bundle repository.
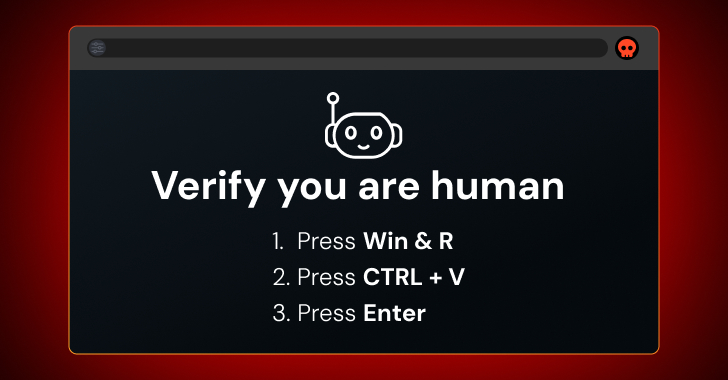
“Based mostly on the sufferer’s working system and whether or not Qihoo 360 antivirus is working, the bundle downloads a payload, writes it to the system temp listing, and silently executes it,” Socket safety researcher Olivia Brown stated in a report. “The bundle seems to return the Ethereum model quantity, so the sufferer is none the wiser.”
A notable facet of the bundle is that it’s explicitly designed to test for the presence of the “qhsafetray.exe” course of, an executable file related to 360 Complete Safety, an antivirus software program developed by Chinese language safety vendor Qihoo 360.
Particularly, the bundle is designed to invoke a seemingly innocent operate named “get_evm_version(),” which decodes and reaches out to an exterior URL (“obtain.videotalks[.]xyz”) to fetch a next-stage payload relying on the working system on which it is being run –
On Linux, it downloads a script, saves it in /tmp/init, and runs it within the background utilizing the nohup command, enabling the attacker to achieve full management
On macOS, it downloads a file known as init and runs it utilizing osascript within the background with the nohup command
On Home windows, it downloads and saves the payload as a PowerShell script file (“init.ps1”) within the temp listing and checks working processes for “qhsafetray.exe,” earlier than invoking the script
Within the occasion the method will not be current, it creates a Visible Fundamental Script wrapper that runs a hidden PowerShell script with no seen window. If the antivirus course of is detected, it barely alters its execution movement by straight invoking PowerShell.
“This give attention to Qihoo 360 is a uncommon, express, China-focused concentrating on indicator, as a result of it’s a main Chinese language web firm,” Brown stated. “It suits the crypto-theft profile, as Asia is likely one of the largest world markets for retail cryptocurrency exercise.”
The references to EVM and Uniswap, a decentralized cryptocurrency change protocol constructed on the Ethereum blockchain, point out that the provision chain incident is designed to focus on builders within the Web3 house by passing off the packages as Ethereum-related utilities.
“Ablerust, the menace actor accountable for the malicious code, embedded a cross-platform second-stage loader inside a seemingly innocent operate,” Brown stated. “Worse, the dependency was pulled into one other extensively used bundle (uniswap-utils), permitting the malicious code to execute mechanically throughout initialization.”