In a recent development, a newly identified cyber threat actor has been linked to attacks on Ukrainian organizations using a malware variant named CANFAIL. According to the Google Threat Intelligence Group (GTIG), the cybercriminal group is suspected of having connections with Russian intelligence services. Their primary targets include defense, military, government, and energy sectors within Ukraine.
Expanding Targets and Tactics
Beyond these sectors, the group has shown increasing interest in aerospace and manufacturing entities linked to military and drone technology, as well as nuclear and chemical research bodies. Additionally, international organizations focusing on conflict monitoring and humanitarian efforts in Ukraine have also been targeted by the hackers.
Despite being less organized and funded compared to other Russian hacking groups, the attackers are evolving by leveraging large language models (LLMs) to enhance their technical capabilities. These models assist them in conducting reconnaissance, designing social engineering baits, and resolving basic technical queries related to post-compromise activities and command-and-control (C2) infrastructure.
Phishing Strategies and Techniques
The group’s phishing campaigns often involve impersonating legitimate Ukrainian energy firms to gain unauthorized access to personal and corporate email accounts. They have also been observed masquerading as a Romanian energy company with Ukrainian connections and targeting Romanian and Moldovan entities.
Central to their operations is the creation of targeted email lists based on geographical and industrial research. Their attack vectors frequently employ LLM-generated lures and contain Google Drive links that lead to a RAR archive with the CANFAIL malware.
Technical Characteristics of CANFAIL Malware
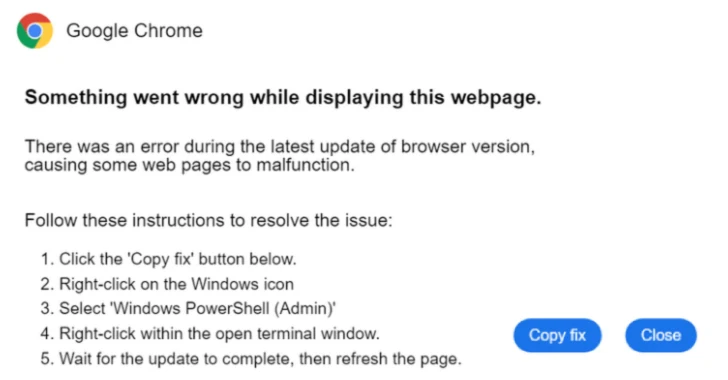
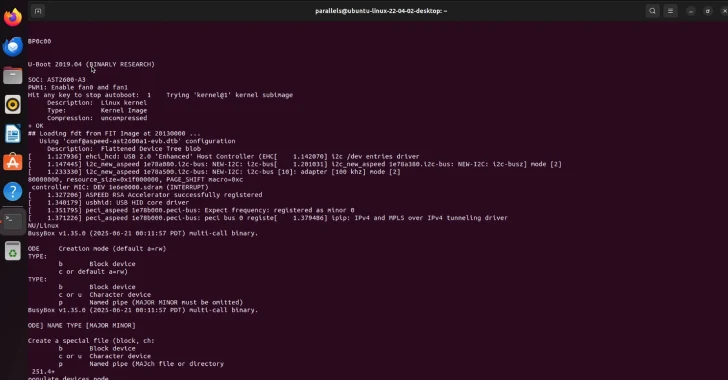
The CANFAIL malware, often disguised with a double extension to appear as a PDF document, is actually obfuscated JavaScript. Once executed, it runs a PowerShell script that downloads and executes an in-memory PowerShell dropper while showing a fake error message to the victim.
GTIG has also associated this threat actor with a campaign named PhantomCaptcha, identified by SentinelOne’s SentinelLABS in October 2025. This campaign targeted Ukrainian war relief organizations through phishing emails that redirected users to counterfeit pages designed to initiate the infection process using a WebSocket-based trojan.
As the situation develops, organizations are urged to enhance their cybersecurity measures to defend against such sophisticated cyber threats, particularly those originating from state-sponsored actors.