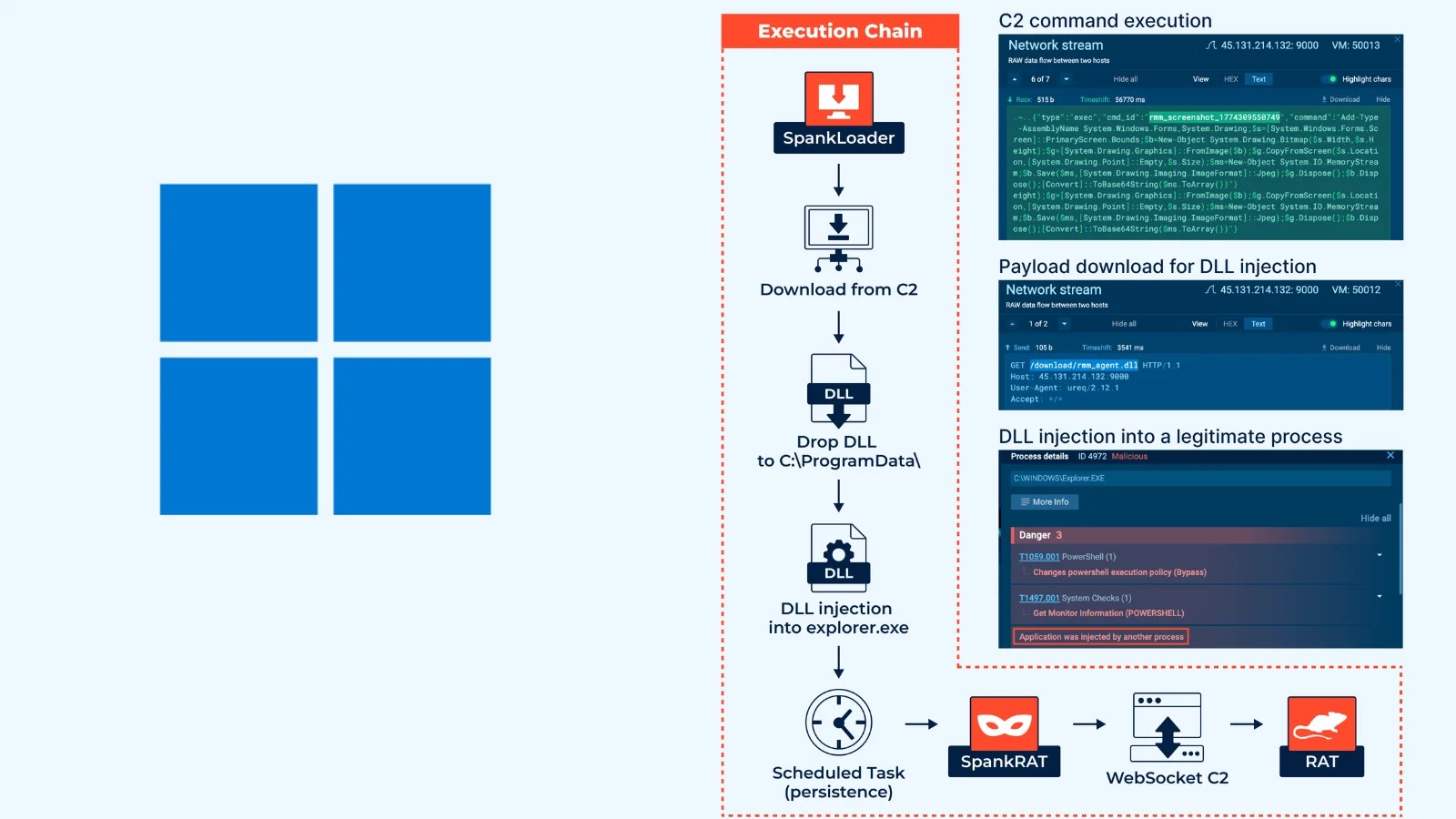
Cybercriminals are increasingly using stolen credentials to infiltrate corporate networks, posing a significant threat to security. Unlike traditional methods that exploit software vulnerabilities, attackers are now leveraging infostealer malware to conduct large-scale brute-force attacks on Single Sign-On (SSO) gateways.
Infostealers Target Corporate Gateways
Infostealer malware families have become central to a new wave of cyberattacks focusing on corporate SSO systems, particularly targeting F5 BIG-IP interfaces. This shift was brought into the spotlight on February 23, 2026, when Defused Cyber reported a significant credential stuffing campaign aimed at these gateways. The attack involved a single IP address, 219.75.254.166, linked to OPTAGE Inc. in Japan, which was utilized to bombard systems with legitimate-looking email and password combinations.
The precision of these attacks is noteworthy. The credentials used appeared to be authentic, linked to employees from multinational corporations and government bodies. These were not credentials obtained from an F5 data breach but rather collected from devices compromised by infostealer malware.
Identifying the Source of Compromised Credentials
Analysis by infostealers analysts revealed a strong correlation between the credentials used in the attacks and those found in Hudson Rock’s cybercrime database. Of the 70 observed email-password pairs, 54 matched known infostealer infection logs, indicating a 77% match rate. The malware had extracted these credentials from infected devices, which were then used to attack systems such as Active Directory Federation Services (ADFS) and Security Token Services (STS).
The attack affected numerous high-profile organizations, including Rolls-Royce, Johnson & Johnson, and the Belgian Police, among others. Turkish government ministries and retail conglomerates were also targeted, exploiting weak or absent multi-factor authentication measures to gain access.
Infrastructure and Defense Strategies
The attackers’ infrastructure added complexity to the threat, with the source IP traced back to a compromised Fortinet FortiGate-60E firewall at OPTAGE Inc. Open ports and a self-signed SSL certificate further facilitated the malicious traffic routing. This dual-threat strategy, combining stolen identities with compromised devices, poses a formidable challenge to detection and defense.
The concept of a “Log-to-Lead” pipeline exemplifies the industrial nature of these attacks, where infostealer data is quickly transformed into network access. Organizations can mitigate these threats by implementing phishing-resistant multi-factor authentication, monitoring exposed credentials, and preventing password reuse across systems. Educating employees about the risks of browser-saved passwords is also crucial to disrupt the infostealer supply chain.
Stay informed with our updates by following us on Google News, LinkedIn, and X, and ensure you set Site Name as a preferred source on Google for the latest cybersecurity news.