The emergence of SpankRAT, a sophisticated Remote Access Trojan (RAT) developed in Rust, highlights a growing threat to Windows security. This toolkit is being leveraged by cybercriminals to manipulate legitimate Windows processes. By doing so, it effectively bypasses reputation-based security controls and maintains persistent access to compromised systems, all while evading detection on platforms like VirusTotal.
Understanding SpankRAT’s Stealth Capabilities
Researchers from ANY.RUN have extensively analyzed SpankRAT, identifying it as a significant threat due to its capability to reroute Command and Control (C2) traffic through trusted system processes. This tactic allows the malware to evade detection based on reputation, reducing the visibility of Security Operations Centers (SOCs) and increasing the risk of undetected breaches.
SpankRAT’s stealth is primarily due to its use of legitimate Windows binaries for malicious network activities, which are often deprioritized during security triage. As a result, compromised environments remain vulnerable for longer periods.
The Role of SpankLoader in SpankRAT Attacks
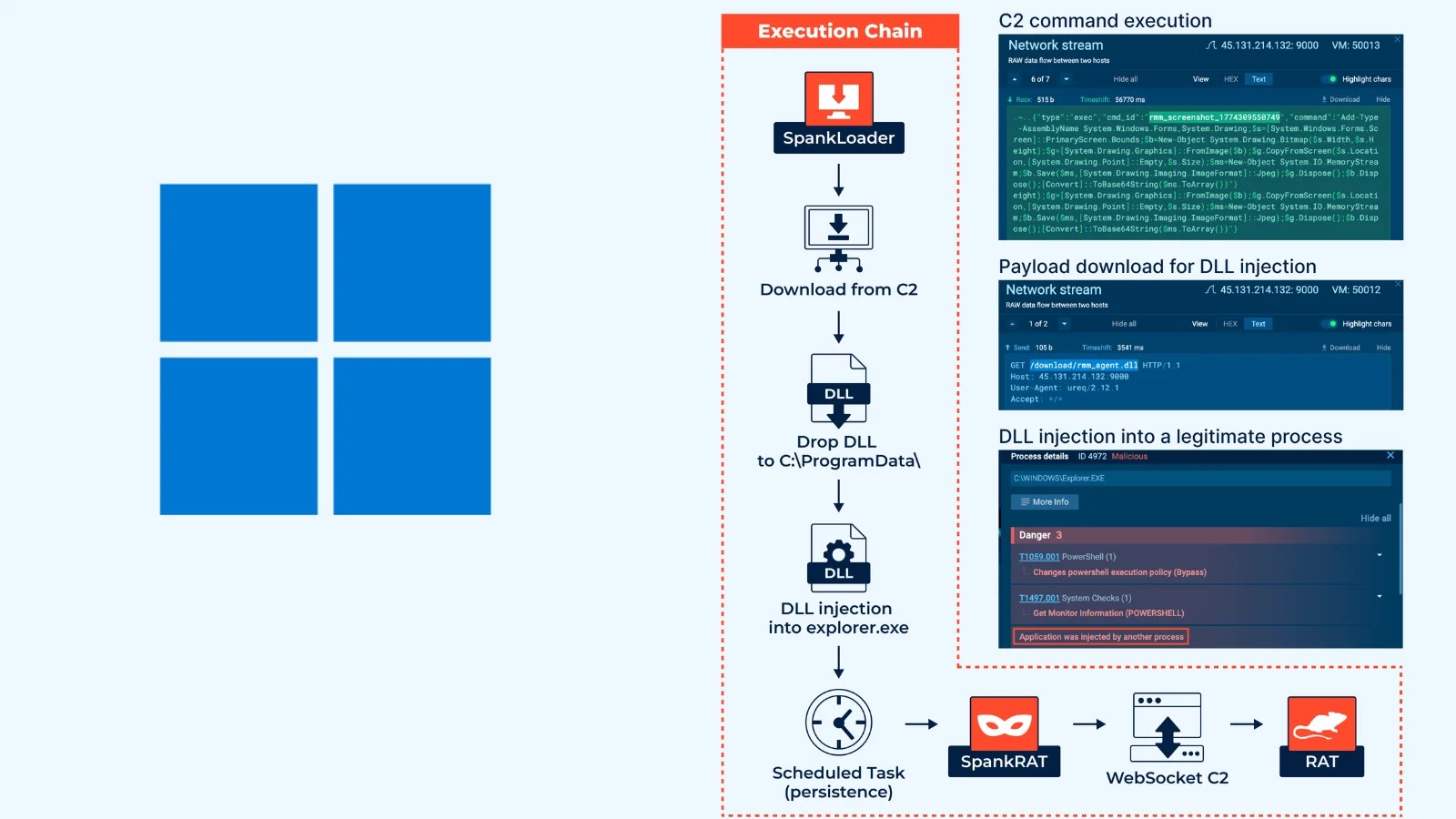
The initial stage of a SpankRAT attack begins with SpankLoader, a lightweight loader retrieving the primary payload from a C2 server using unencrypted HTTP. Upon execution, SpankLoader enhances privileges and drops a malicious DLL into the system, injecting it into the explorer.exe process through classic DLL injection techniques.
To ensure its persistence, SpankLoader sets up a Scheduled Task named RmmAgentCore, configured to trigger upon logon with the highest privileges. This method disguises malware-generated traffic as originating from a trusted process, complicating detection by traditional endpoint and network security solutions.
SpankRAT’s Comprehensive Control Features
Once embedded in explorer.exe, SpankRAT establishes a WebSocket-based connection to its C2 server, utilizing a JSON communication protocol. This variant supports 18 distinct server commands, providing attackers with extensive remote control over infected systems.
The command set includes capabilities such as session management, remote command execution, file operations, process control, and registry manipulation. All interactions are executed through PowerShell, bypassing typical security policies.
Despite the potency of SpankRAT, most of its samples remain undetected by VirusTotal, highlighting significant vulnerabilities in signature and reputation-based detection systems. The use of behavioral analysis platforms like ANY.RUN’s Sandbox is crucial for uncovering full execution chains and C2 communication patterns in real-time, even when traditional methods fail.
Indicators of Compromise and Mitigation Strategies
Security teams should be vigilant for specific indicators such as C2 server addresses, agent hashes, malicious files, and specific persistence mechanisms. Monitoring for unauthorized DLL injections into explorer.exe or unusual Scheduled Task creations with elevated privileges can aid in early threat detection.
Organizations relying solely on antivirus solutions are advised to incorporate dynamic sandbox analysis to minimize threat dwell time. This approach is particularly beneficial for threats like SpankRAT, which remain elusive to conventional detection tools. The exclusivity of the malware samples emphasizes the importance of proactive cybersecurity measures.