Google has recently confirmed the exploitation of a significant security flaw in a Qualcomm component used in Android devices. Known as CVE-2026-21385, this vulnerability is categorized as high-severity, with a CVSS score of 7.8. It has been identified as a buffer over-read issue within the Graphics component, potentially leading to memory corruption through unchecked user data input.
Details of the Vulnerability
Qualcomm, the chipset manufacturer, described the flaw as an integer overflow, explaining that the issue arises when user-supplied data is added without verifying the available buffer space. This vulnerability was initially reported to Qualcomm by Google’s Android Security team on December 18, 2025, with affected customers being informed on February 2, 2026.
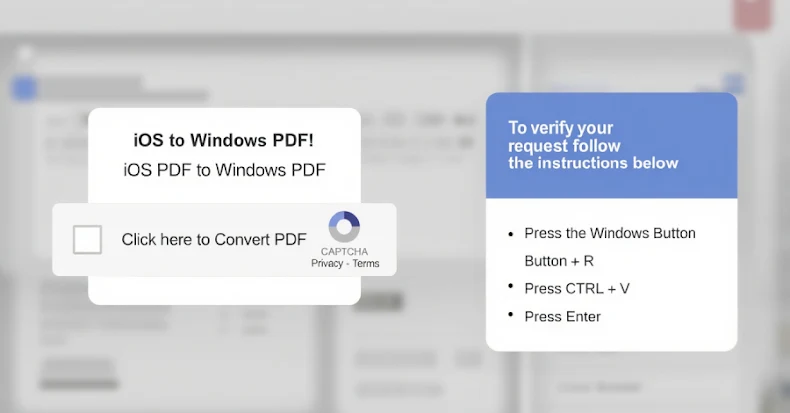
Although specific exploitation methods have not been disclosed, Google’s March security bulletin indicates that CVE-2026-21385 is being actively exploited in limited, targeted attacks. The lack of detailed exploitation information underscores the critical need for users to apply security updates promptly.
March Security Update and Its Implications
The latest Android security update from Google addresses a total of 129 vulnerabilities, including another critical issue in the System component identified as CVE-2026-0006. This particular flaw could enable remote code execution without additional privileges or user involvement.
In addition to the newly patched vulnerabilities, Google included fixes for several other critical security issues. These include a privilege escalation bug in the Framework component, a denial-of-service (DoS) vulnerability in the System component, and multiple privilege escalation flaws across various Kernel components.
Patch Levels and Partner Flexibility
The March 2026 Android security bulletin introduces two patch levels: 2026-03-01 and 2026-03-05. This dual patch level approach allows Android partners to address vulnerabilities more efficiently across different devices. The second patch level includes updates not only for Kernel components but also for components from Arm, Imagination Technologies, MediaTek, Qualcomm, and Unisoc.
These measures illustrate Google’s commitment to enhancing the security landscape for Android devices, urging users and partners to prioritize these updates to prevent potential exploits and ensure device safety.
As the cybersecurity landscape evolves, staying informed and promptly applying security patches remains crucial in safeguarding devices against emerging threats.