Cybersecurity experts have detected a sophisticated campaign in which attackers are posing as IT support to distribute the Havoc command-and-control (C2) framework. This strategy serves as a precursor to either data theft or ransomware attacks.
This campaign, identified by Huntress last month, affected five partner organizations. It involved spam emails and follow-up phone calls from fake IT help desks, initiating a complex malware delivery chain. According to researchers Michael Tigges, Anna Pham, and Bryan Masters, one incident saw attackers access nine additional endpoints within eleven hours, deploying custom Havoc Demon payloads and legitimate remote management tools to sustain their presence. This rapid lateral movement suggests a clear intent towards data theft or ransomware deployment.
Background and Tactics
The tactics used in these attacks resemble previous email bombing and phishing operations attributed to the Black Basta ransomware group. Despite this group’s apparent inactivity following a leak of its internal communications last year, the persistence of their methods indicates two possibilities. Either former Black Basta affiliates are engaging in other ransomware operations, or competing threat actors are mimicking their techniques to execute social engineering and gain initial entry.
The attack method begins with a spam campaign designed to inundate targets’ inboxes with junk mail. Subsequently, the attackers, pretending to be IT support, contact victims and deceive them into allowing remote access via Quick Assist or tools like AnyDesk to resolve supposed issues.
Execution and Evasion
Once access is obtained, attackers swiftly open a web browser to a counterfeit page hosted on Amazon Web Services (AWS), mimicking Microsoft. Here, victims are instructed to input their email to update Outlook’s anti-spam rules. Clicking “Update rules configuration” on this bogus page runs a script prompting users to enter their password, thus enabling the theft of credentials while enhancing the interaction’s credibility.
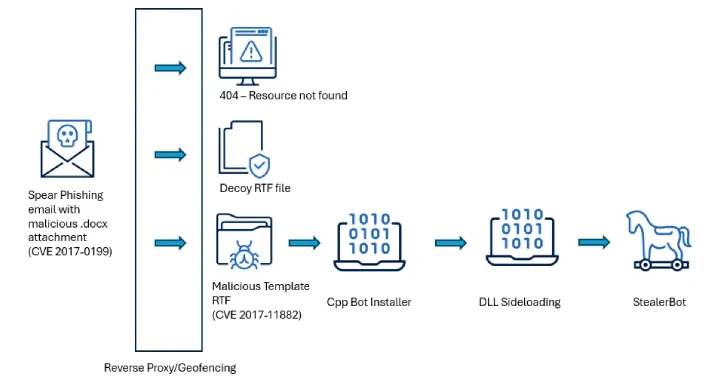
Further, the assault entails downloading a fake anti-spam patch, leading to the execution of legitimate binaries like “ADNotificationManager.exe” to sideload a malicious DLL. This DLL is designed to evade defenses and run the Havoc shellcode payload by spawning a thread with the Demon agent. Notably, one DLL, “vcruntime140_1.dll,” uses advanced evasion tactics to circumvent security software.
Persistence and Implications
After deploying the Havoc Demon on the initial host, attackers expanded their reach across the victim’s network. While initial social engineering and malware delivery showed innovative methods, the subsequent manual actions were relatively straightforward. Scheduled tasks were created to persistently launch the Havoc Demon payload upon each system reboot, granting attackers ongoing remote access.
Notably, attackers also employed legitimate remote monitoring and management (RMM) tools like Level RMM and XEOX on some compromised hosts, diversifying their persistence efforts. The campaign underscores how attackers are willing to impersonate IT staff and engage victims directly to increase their success rate. Techniques once reserved for major firms or state-backed activities are now commonplace, with customized malware bypassing standard security signatures.
As attacks rapidly progress from initial compromise to extensive network penetration, utilizing multiple persistence methods, organizations must remain vigilant. This deceptive IT support strategy exemplifies how modern adversaries integrate sophistication at every phase: using social engineering to gain entry, DLL sideloading for stealth, and varied persistence techniques to endure remediation.