The rapid integration of artificial intelligence into cyber attack strategies is reshaping the landscape of digital threats. Cloudflare’s threat intelligence division, Cloudforce One, unveiled its first annual 2026 Threat Report on March 3, 2026, highlighting AI as a key component of contemporary cyber threats. This report, which draws on trillions of network signals collected over the past year, underscores a significant change in how adversaries operate, urging organizations to rethink their defense mechanisms.
AI’s Role in Modern Cyber Attacks
A pivotal element of this evolution is the Measure of Effectiveness (MOE), a metric that attackers use to maximize the impact of their actions while minimizing effort. Cyber adversaries are increasingly focused on efficiency, opting for methods like stealing session tokens over developing complex exploits, as AI accelerates the timeline from target identification to compromise.
Cloudflare’s analysis reveals eight major trends driven by MOE considerations in 2026. These include the use of generative AI for network mapping, exploit development, and deepfake creation, enabling less skilled threat actors to perform operations previously reserved for state-backed groups.
State-Sponsored Cyber Intrusions
State-affiliated hacking groups, such as China’s Salt Typhoon and Linen Typhoon, are embedding themselves in North American telecommunications and IT sectors, securing long-term positions to further geopolitical goals. Hyper-volumetric DDoS attacks, supported by botnets like Aisuru, have reached unprecedented levels, with data transfer rates peaking at 31.4 Tbps.
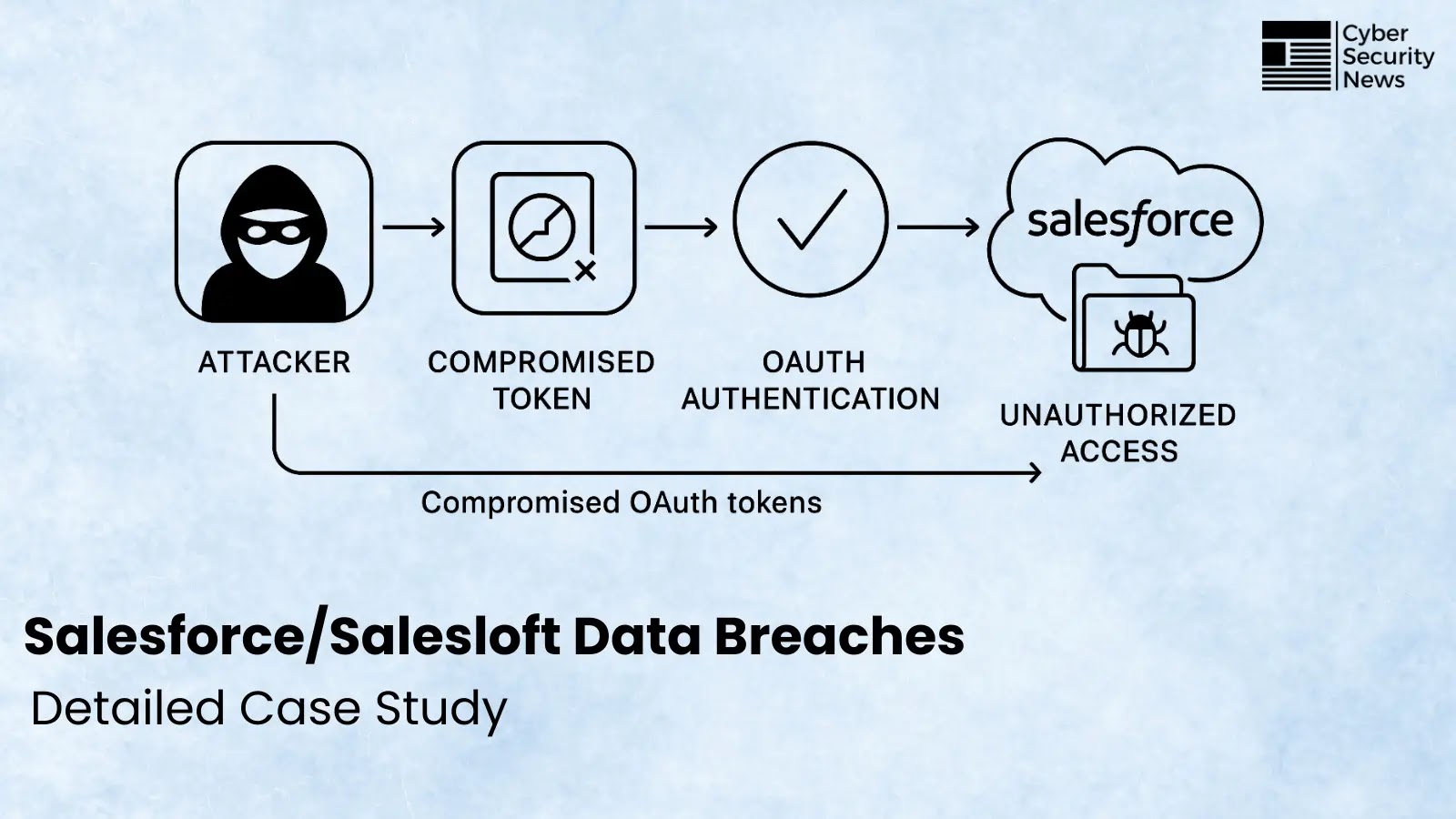
The report also highlights the rise of token theft as a particularly damaging method, with tools like LummaC2 capturing session tokens to bypass authentication entirely. Additionally, phishing-as-a-service exploits weaknesses in email verification, with nearly half of examined emails failing DMARC checks.
Emerging Threats and Defensive Measures
Beyond digital assaults, North Korea is advancing the use of deepfakes, employing AI-generated videos to infiltrate Western companies under false identities. These operations enable espionage from within, posing a significant challenge that firewalls alone cannot counter.
Threat actors are increasingly disguising their activities within trusted tools, a tactic known as Living off the Land (LotX). By exploiting platforms like Google Drive and Microsoft Teams, attackers blend malicious traffic with legitimate business operations, remaining undetected for extended periods.
Cloudforce One’s research highlights various nation-state groups employing these tactics, including China’s FrumpyToad and PunyToad, Russia’s NastyShrew, North Korea’s PatheticSlug, and Iran’s CrustyKrill, each utilizing different methods to evade detection and maintain persistence.
Adapting to AI-Driven Threats
To counter these advanced threats, Cloudforce One recommends adopting autonomous defense systems over traditional manual detection methods. With AI accelerating attack speeds, slow response times pose significant risks. Organizations should implement DMARC, DKIM, and SPF protocols for email security, enforce Zero Trust access across SaaS platforms, and regularly audit third-party integrations to prevent over-privilege exposures. Real-time automated responses are now essential to keep pace with relentless AI-driven adversaries.