The past week in cybersecurity has been a whirlwind of activity, marked by both significant triumphs and daunting challenges. As attackers and defenders continue their digital cat-and-mouse game, several notable developments have emerged. This week’s highlights include the dismantling of major phishing operations, discovery of vulnerabilities in popular software, and evolving tactics by threat actors.
Phishing Operations Dismantled
In a significant victory for cybersecurity, Europol and a coalition of security firms successfully dismantled the infrastructure behind Tycoon 2FA, a major phishing-as-a-service operation. Described as one of the largest adversary-in-the-middle phishing platforms, its takedown is expected to impact multi-factor authentication credential phishing significantly. Similarly, the authorities brought down LeakBase, a notorious cybercrime forum, although experts warn that such disruptions often only cause short-term setbacks.
Phishing kits have made it easier for less skilled hackers to launch attacks by providing them with tools to create persuasive phishing emails and websites. The shutdown of Tycoon 2FA and LeakBase marks a crucial step in combating these threats, though the ecosystem is expected to adapt and find new avenues.
Vulnerabilities and Exploit Kits
Anthropic, in collaboration with Mozilla, discovered 22 vulnerabilities in the Firefox web browser, with most being classified as high severity. These issues have been addressed in Firefox 148. On the other hand, a critical flaw in Qualcomm chips used in Android devices has been actively exploited. CVE-2026-21385, a buffer over-read vulnerability, poses risks of memory corruption and arbitrary code execution.
Additionally, Google has revealed details about the Coruna iOS exploit kit, which targets older iOS versions with a total of 23 exploits. Initially developed by a commercial surveillance vendor, this kit has changed hands among various threat actors, including espionage groups and financially motivated attackers.
Emerging Threats and Nation-State Actors
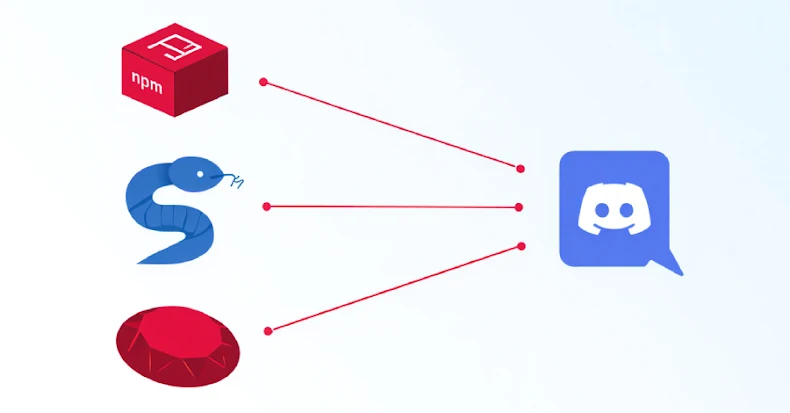
The Transparent Tribe, a threat actor group, has launched a campaign using AI-powered tools to target Indian government entities. By leveraging niche programming languages, they aim to evade detection and flood environments with malware. Meanwhile, the Iranian group MuddyWater has been targeting U.S. entities, escalating tensions amidst geopolitical conflicts.
In another development, a new attack called AirSnitch has been unveiled, exposing vulnerabilities in Wi-Fi client isolation. This highlights the need for robust security measures to protect against potential advanced cyber attacks.
As the cybersecurity landscape continues to evolve, staying informed and vigilant remains crucial. With new vulnerabilities and exploit methods emerging, organizations and individuals must prioritize updating their defenses and staying informed about the latest threats.
Overall, while some progress has been made in dismantling key phishing operations and addressing software vulnerabilities, the cybersecurity battle is far from over. It’s essential to remain proactive in safeguarding digital assets and adapting to the ever-changing threat landscape.