Rising Threat of OAuth Device Phishing
Security experts at ANY.RUN have reported a concerning rise in phishing attacks leveraging Microsoft’s OAuth Device Authorization Grant flow. Within just a single week, over 180 malicious URLs were uncovered, indicating a significant threat to users.
Unlike typical credential-stealing tactics, this method uses genuine Microsoft authentication pages, complicating detection for security operation centers (SOCs).
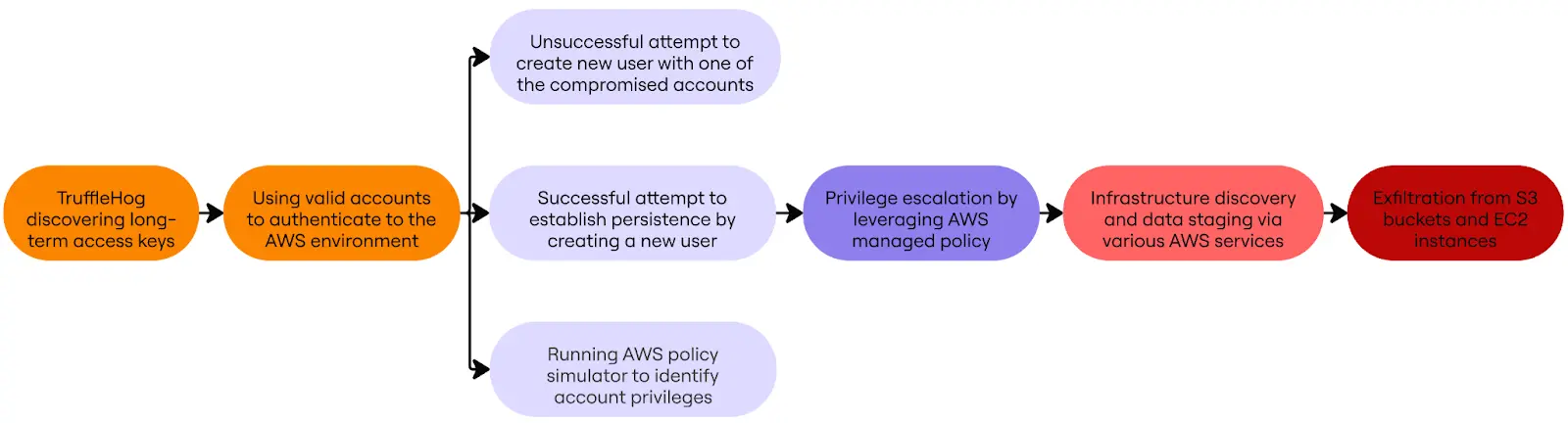
Understanding OAuth Device Code Exploitation
Originally, the OAuth Device Code flow was intended for devices with limited input capabilities, like smart TVs. However, attackers have adapted this process for unauthorized account access, effectively bypassing multi-factor authentication (MFA).
The attack initiates when cybercriminals request a Microsoft device authorization, generating a user_code for the victim and a device_code for the attacker. Victims are misled into entering their code on a legitimate Microsoft site, unknowingly granting attackers access tokens.
Impact on Security Operations
The implications for SOCs are profound. Compromises often remain undetected until suspicious activity is observed, extending the time required for investigation. SOCs must track token-based access rather than stolen credentials, which increases the complexity of incident response.
Malicious actors can access sensitive resources, such as Microsoft 365 data, immediately after acquiring tokens, facilitating potential internal movement and data theft.
Enhanced Detection and Mitigation Strategies
To tackle this sophisticated phishing model, traditional domain filtering and email security measures are insufficient. ANY.RUN offers solutions like Interactive Sandbox and Threat Intelligence Feeds, enabling earlier detection of phishing infrastructures.
Security teams benefit from features like SSL decryption and Suricata IDS rules, which identify malicious traffic previously concealed by encryption. Such advancements are crucial for timely detection and response to these complex attacks.
To address the evolving threat landscape, organizations must prioritize identity-layer visibility and encrypted traffic inspection, as outlined in Microsoft’s 2025 Digital Defense Report. This approach is essential for modern SOC operations aiming to safeguard against persistent identity attacks.