A complicated Android banking trojan often known as ToxicPanda has efficiently infiltrated over 4500 cell gadgets throughout Europe, representing one of the vital cell banking malware campaigns noticed in recent times.
The malware particularly targets banking and digital pockets purposes, using superior overlay methods to steal login credentials, PIN codes, and sample locks whereas enabling cybercriminals to carry out unauthorized monetary transactions remotely.
ToxicPanda operates as a extremely advanced banking trojan that infiltrates Android gadgets to reap delicate monetary data from banking and monetary purposes.
The malware demonstrates exceptional sophistication via its capability to create pixel-perfect phishing overlays that mimic official banking interfaces, successfully deceiving customers into coming into their credentials straight into malicious kinds.
As soon as put in, the trojan grants attackers complete management over compromised gadgets, permitting them to intercept two-factor authentication codes, bypass safety measures, and provoke fraudulent cash transfers with out consumer data.
First recognized by Development Micro researchers in 2022, ToxicPanda initially centered its operations on Southeast Asian markets earlier than increasing its attain to European territories in 2024.
The malware marketing campaign has demonstrated vital development and geographic redistribution, with present operations primarily concentrated in Portugal and Spain.
BitSight analysts recognized a considerable shift within the malware’s focusing on technique throughout early 2025, noting that Portuguese gadgets now account for about 3000 infections whereas Spanish gadgets signify round 1000 compromised methods.
The present European marketing campaign reveals a deliberate focusing on technique centered on the Iberian Peninsula, with Portugal and Spain collectively representing over 85% of all noticed world infections.
Contaminated cellphone fashions (Supply – Bitsight)
The malware exhibits specific affinity for mid-range Android gadgets, with Samsung A sequence, Xiaomi Redmi, and Oppo A fashions comprising nearly all of contaminated gadgets, although premium fashions together with Samsung S sequence gadgets have additionally been compromised.
Superior Persistence and Evasion Mechanisms
ToxicPanda employs refined persistence methods that make conventional elimination strategies ineffective, demonstrating the malware authors’ deep understanding of Android safety structure.
The trojan abuses Android’s Accessibility Companies framework, initially designed to help customers with disabilities, to realize elevated privileges and keep persistent management over contaminated gadgets.
‘dropper.apk’ and ‘no_dropper.apk’ (Supply – Bitsight)
The malware implements a number of layers of persistence via dynamic broadcast receiver registration that screens system occasions together with package deal elimination, alternative, and information clearing operations.
When customers try to uninstall the applying via standard strategies, ToxicPanda mechanically closes settings home windows and prevents entry to accessibility service configurations via its hijacked UI management capabilities.
The trojan’s anti-analysis capabilities embody complete emulator detection mechanisms that look at CPU data, system properties, and {hardware} traits to keep away from execution in sandbox environments.
Current variations incorporate enhanced detection strategies together with Bluetooth adapter verification, ambient gentle sensor checks, and telephony service validation.
The malware employs a Area Era Algorithm (DGA) that creates month-to-month rotating domains mixed with sequential top-level area biking, making certain communication resilience even when particular person command and management servers are compromised.
ToxicPanda’s encryption implementation makes use of hardcoded AES keys (“0623U25KTT3YO8P9”) for main communications and DES encryption (“jp202411”) for fallback area storage, sustaining safe channels between contaminated gadgets and command infrastructure.
Faux ‘Google Chrome’ (Supply – Bitsight)
The malware package deal masquerades as “Google Chrome” whereas working below the inner identifier “com.instance.mysoul,” requesting 58 completely different Android permissions to attain complete system entry.
Full elimination requires Android Debug Bridge (ADB) instructions as a result of malware’s refined self-protection mechanisms that stop customary uninstallation procedures.
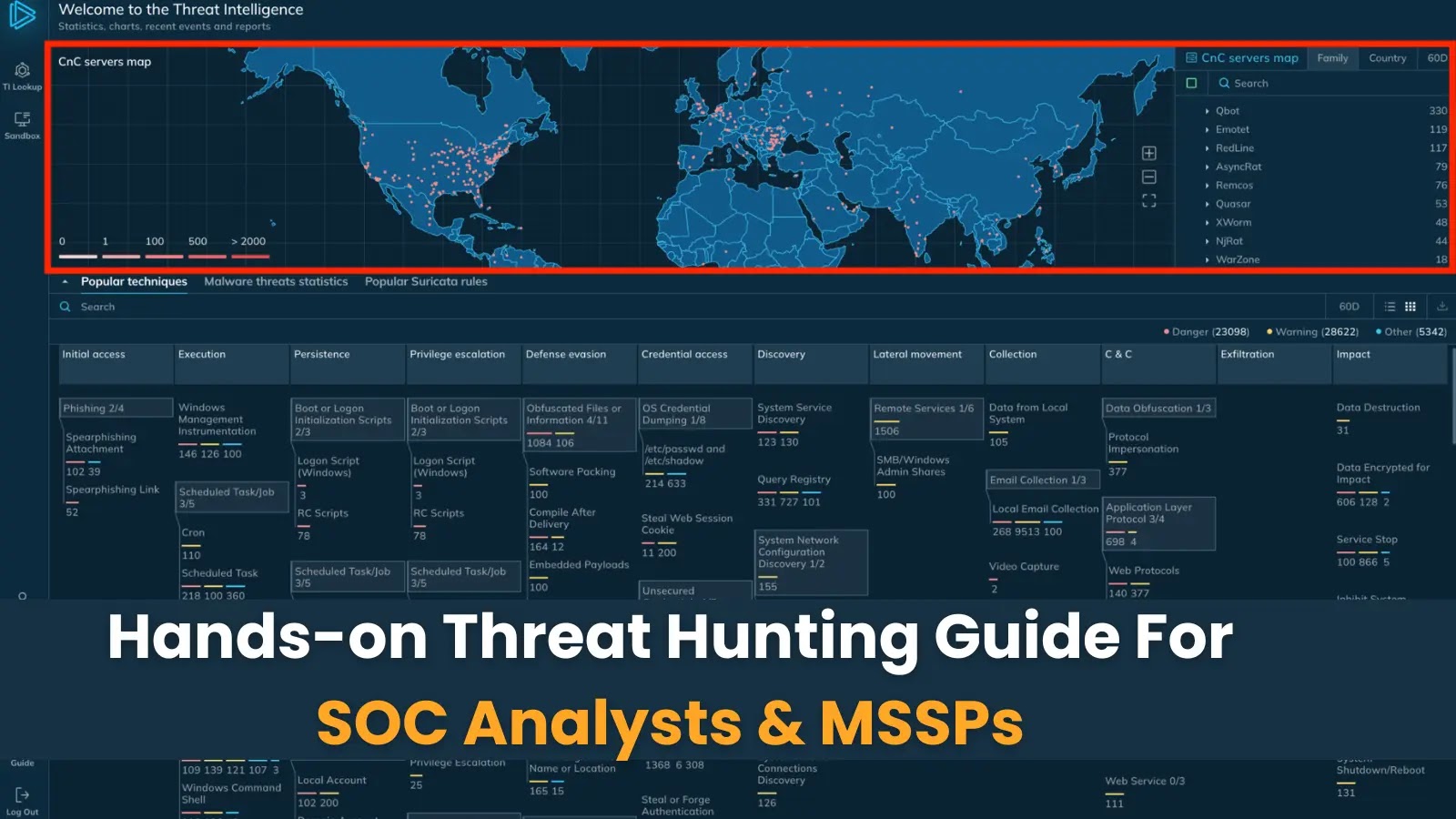
Combine ANY.RUN TI Lookup together with your SIEM or SOAR To Analyses Superior Threats -> Strive 50 Free Trial Searches