SILENTCONNECT, a sophisticated multi-stage malware, has been quietly infiltrating Windows systems since March 2025. It employs a combination of VBScript, in-memory PowerShell, and PEB masquerading to deploy the ConnectWise ScreenConnect tool, posing significant security risks to organizations globally.
How SILENTCONNECT Operates
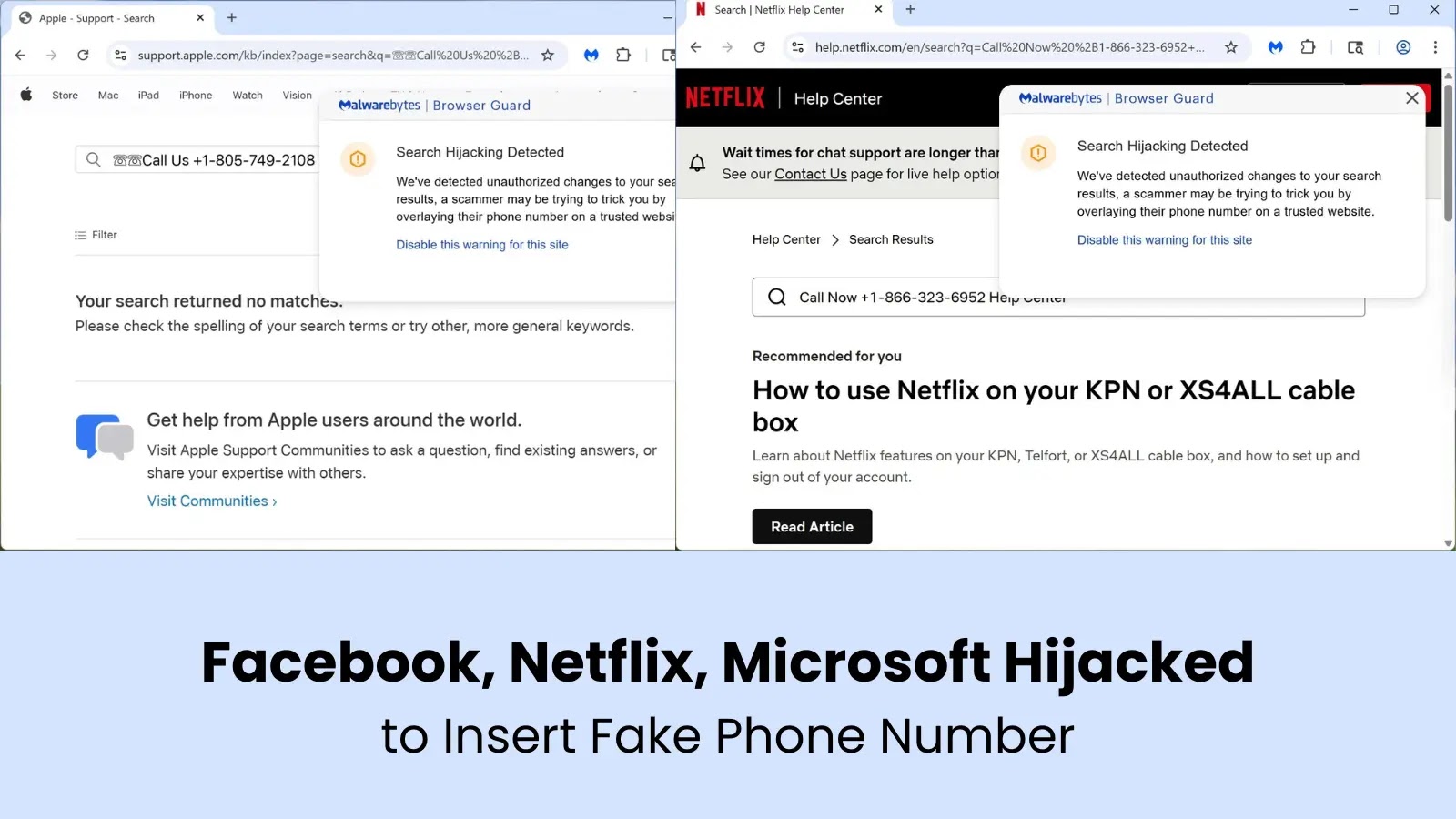
The malware’s initial entry point is a phishing email, which lures victims with links that appear legitimate. Once the link is clicked, users are redirected to a Cloudflare Turnstile CAPTCHA, which, upon completion, triggers the download of a VBScript file, often disguised with credible names like Proposal-03-2026.vbs.
Researchers from Elastic Security Labs identified this campaign in March 2026. The infection process, characterized by living-off-the-land tactics, prompted numerous behavioral alerts. By tracing the VBScript’s origin URL, analysts discovered the script was hosted on Cloudflare’s r2.dev storage, while the C# payload was sourced from Google Drive, both platforms typically regarded as trustworthy.
Technical Details and Defense Evasion
SILENTCONNECT blends into routine Windows operations to evade detection. The VBScript disguises its true function by embedding malicious instructions within Replace and Chr functions, which decode to execute a PowerShell command. This command then uses curl.exe to download, compile, and execute a C# file in memory, bypassing traditional endpoint security checks.
The malware’s infrastructure showed a consistent pattern, with phishing emails traced back to a fake proposal from dan@checkfirst[.]net[.]au. The URI path download_invitee.php was reused across multiple sites, aiding researchers in mapping the campaign’s full scope.
Advanced Evasion Techniques
Once the .NET loader is executed, SILENTCONNECT vanishes from view by allocating memory through NtAllocateVirtualMemory and inserting a shellcode stub. This shellcode manipulates the Process Environment Block (PEB) to operate stealthily, avoiding monitored API calls.
By altering its module list entry to mimic a legitimate Windows utility, SILENTCONNECT becomes nearly invisible to EDR systems. Preceding ScreenConnect installation, it employs a UAC bypass, obfuscates parameters, and adds a Microsoft Defender exclusion for executables.
Organizations are advised to regularly audit their systems for unauthorized RMM tools and monitor unusual network traffic. Security teams should be vigilant about PowerShell commands, VBScript downloads, and unexpected Defender exclusions, as well as trace NtAllocateVirtualMemory calls in .NET applications.
Stay informed by following us on Google News, LinkedIn, and X. Set CSN as a preferred source on Google for the latest updates.