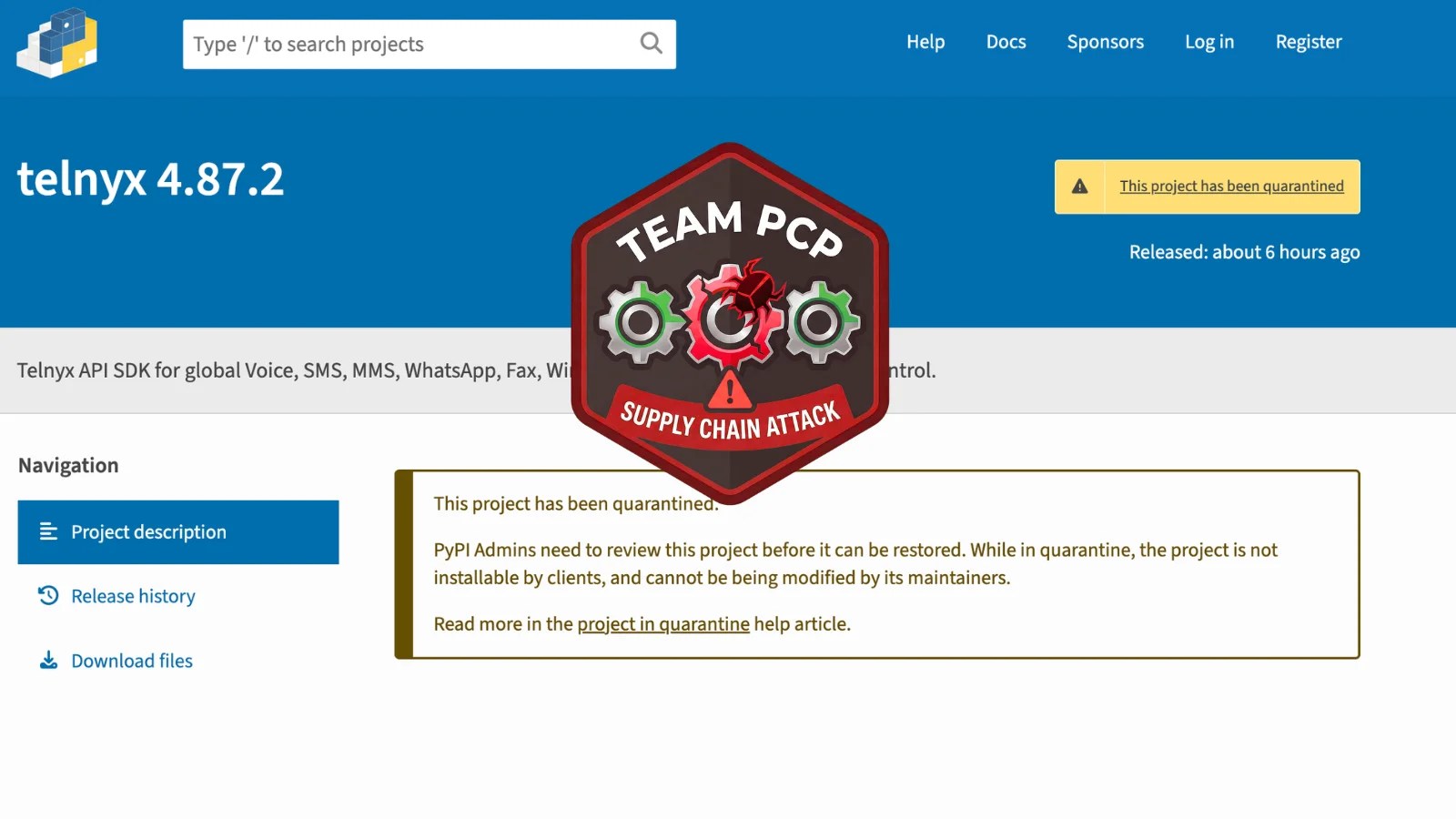
The Telnyx Python package, a widely used software with over 742,000 downloads in the past month, has become the latest target in a series of sophisticated supply chain attacks conducted by a notorious threat actor group known as TeamPCP. The breach was identified on March 27, 2026, when malicious versions of the package were uploaded to the Python Package Index (PyPI).
TeamPCP’s Escalating Campaign
This recent compromise is part of a broader campaign by TeamPCP, a group that has been targeting trusted development tools since March 19, 2026. The group’s method involves infiltrating software supply chains to steal credentials, which are then used to compromise additional targets. Their attacks have affected numerous platforms, including Aqua Security’s Trivy and Checkmarx’s GitHub Actions.
On March 19, TeamPCP backdoored Trivy, assigning it a critical vulnerability score and exploiting it to access sensitive credentials. This breach led to further compromises across npm packages and GitHub repositories, showcasing the group’s ability to move quickly and efficiently within software ecosystems.
Malicious Payload and Execution
The malicious code in the Telnyx package executes at import time, affecting both Windows and Linux/macOS systems. On Windows, it downloads an audio file containing an obfuscated executable, which is designed to persist on the system and execute at startup. On Linux and macOS, a secondary script is embedded within the package, downloading additional payloads in a similar manner.
TeamPCP employs a unique technique involving WAV steganography to evade detection. The payloads are hidden within audio files, which pass standard security checks, making them difficult to identify using traditional filtering methods.
Mitigation and Future Outlook
Organizations using the affected Telnyx versions are urged to treat their systems as compromised. Immediate actions include downgrading to a secure version of the package, rotating all exposed credentials, and monitoring network traffic for suspicious activity. Additionally, it is crucial to audit CI/CD pipelines to prevent further exploitation.
This incident underscores the importance of stringent security measures in software development environments, especially as the FBI warns of potential follow-on intrusions. Organizations are advised to review their dependency management practices and enforce version pinning to mitigate risks.
For more updates on cybersecurity threats and mitigation strategies, follow us on Google News, LinkedIn, and X. Contact us if you wish to feature your cybersecurity stories.