A Pervasive Threat to E-commerce Security
An intricate Magecart campaign has been covertly targeting e-commerce platforms in at least 12 nations for over two years. Utilizing more than 100 malicious domains, this operation aims to pilfer payment card details in real time. The financial burden primarily falls on banking institutions rather than the merchants themselves.
Security experts from ANY.RUN have revealed this large-scale operation, which has compromised at least 17 WooCommerce websites from February 2024 to April 2025. This organized cybercrime syndicate’s infrastructure spans a significant number of domains, indicating a high level of planning and investment.
Widespread Impact Across Multiple Countries
The campaign has affected victims mainly in the UK, Denmark, France, Spain, and the US, with Spain particularly impacted due to the exploitation of the Redsys payment system. While e-commerce platforms are directly targeted, banks and cardholders experience the brunt of the financial fallout, which includes fraud losses and diminished trust in digital payments.
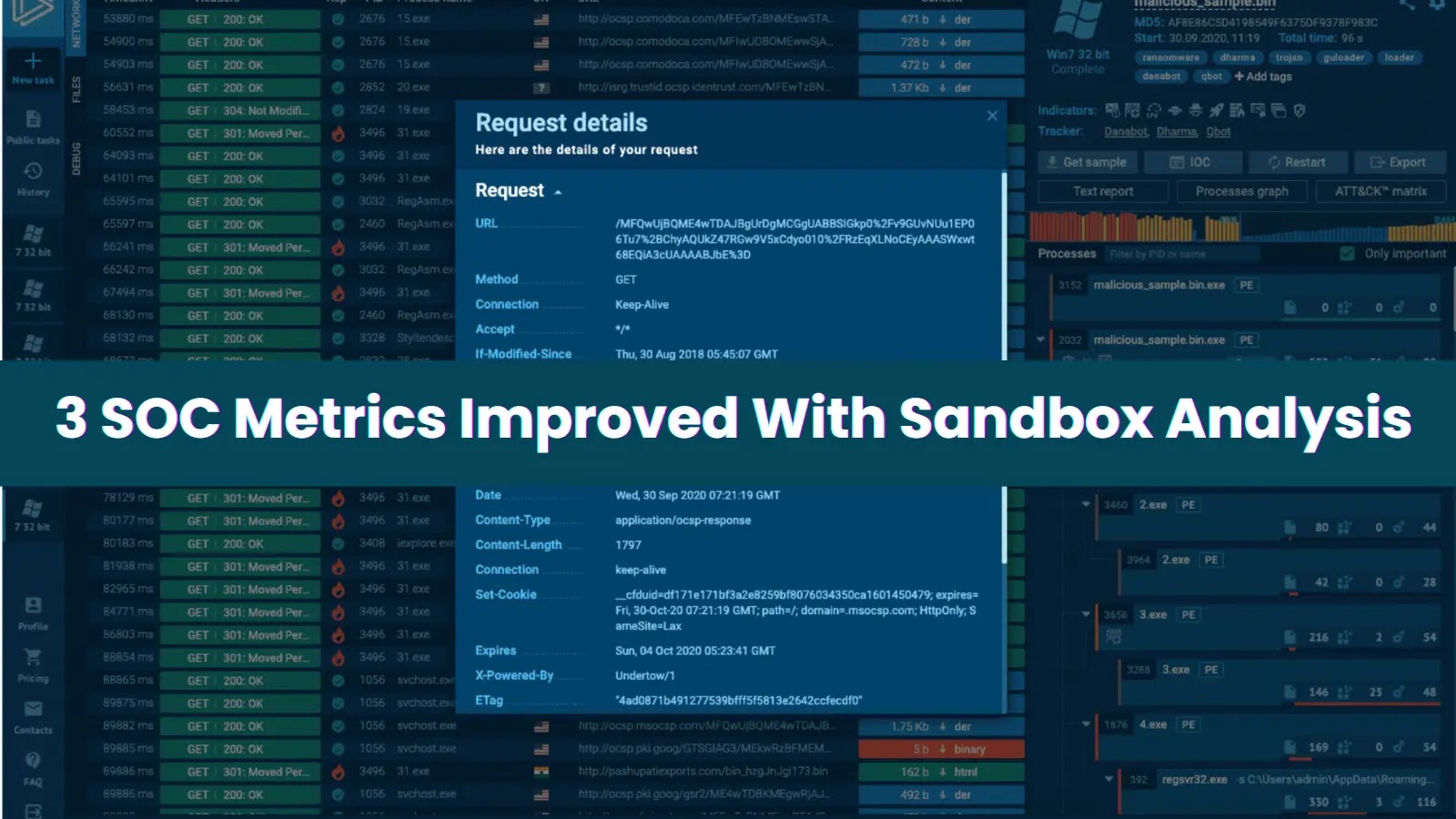
ANY.RUN advocates for businesses to gain early insight into such threats to minimize potential damage. Integrating their solutions into Security Operations Centers (SOC) is suggested to mitigate risks effectively.
Deceptive Tactics and Techniques
The attackers employ a complex, multi-layered infection process to evade detection and removal. Once a WooCommerce site is compromised, a small obfuscated JavaScript loader is injected into existing scripts, remaining inactive until the payment stage is reached by users.
This loader, devoid of direct card-stealing capabilities, connects to external servers to retrieve further malicious payloads. A fallback system ensures the operation’s continuity by cycling through backup domains if the primary ones are inaccessible.
By replacing genuine payment buttons with counterfeit ones, the operation remains undetected for extended periods. Scripts mimic trustworthy web services, such as jQuery and analytics platforms, to capture user data.
Advanced Impersonation and Mobile Expansion
The campaign’s hallmark is its ability to convincingly imitate legitimate payment service providers. The Redsys system is frequently impersonated, with attackers incorporating its domain into their workflow to enhance credibility.
Beyond desktop platforms, the operation extends to mobile devices, utilizing malicious payloads to distribute Android APK files. This vector prompts users to download apps under the guise of discounts, further expanding the campaign’s reach.
Security teams are urged to prioritize monitoring WebSocket connections from checkout pages, enforce strict Content Security Policies, and conduct regular audits of third-party scripts. Financial institutions should focus on threat intelligence sharing and bolstering fraud detection for card-not-present transactions to counteract these persistent threats.
Engage in free malware research with ANY.RUN to safeguard your business today.

.webp?ssl=1)

.webp?ssl=1)