A complicated risk actor referred to as NoisyBear has emerged as a major concern for Kazakhstan’s vitality sector, using superior ways to infiltrate important infrastructure by weaponized ZIP recordsdata and PowerShell-based assault chains.
This newly recognized group has been orchestrating focused campaigns in opposition to KazMunaiGas (KMG), the nation’s nationwide oil and gasoline firm, utilizing extremely crafted phishing emails that mimic authentic inside communications about wage schedules and coverage updates.
The assault methodology demonstrates outstanding precision in social engineering, with risk actors compromising authentic enterprise electronic mail accounts inside KazMunaiGas to lend authenticity to their malicious communications.
These emails comprise ZIP attachments disguised as pressing HR-related paperwork, making a false sense of legitimacy that encourages worker interplay.
The marketing campaign’s sophistication extends past easy phishing, incorporating multi-stage payload supply methods that leverage trusted system binaries and PowerShell execution environments to keep up stealth all through the an infection course of.
Seqrite researchers recognized this risk group’s actions starting in April 2025, with energetic campaigns intensifying all through Might 2025.
The researchers famous that NoisyBear’s operational patterns counsel Russian origins, evidenced by Russian language feedback inside malicious code, utilization of sanctioned internet hosting providers, and concentrating on patterns per geopolitical pursuits in Central Asian vitality sources.
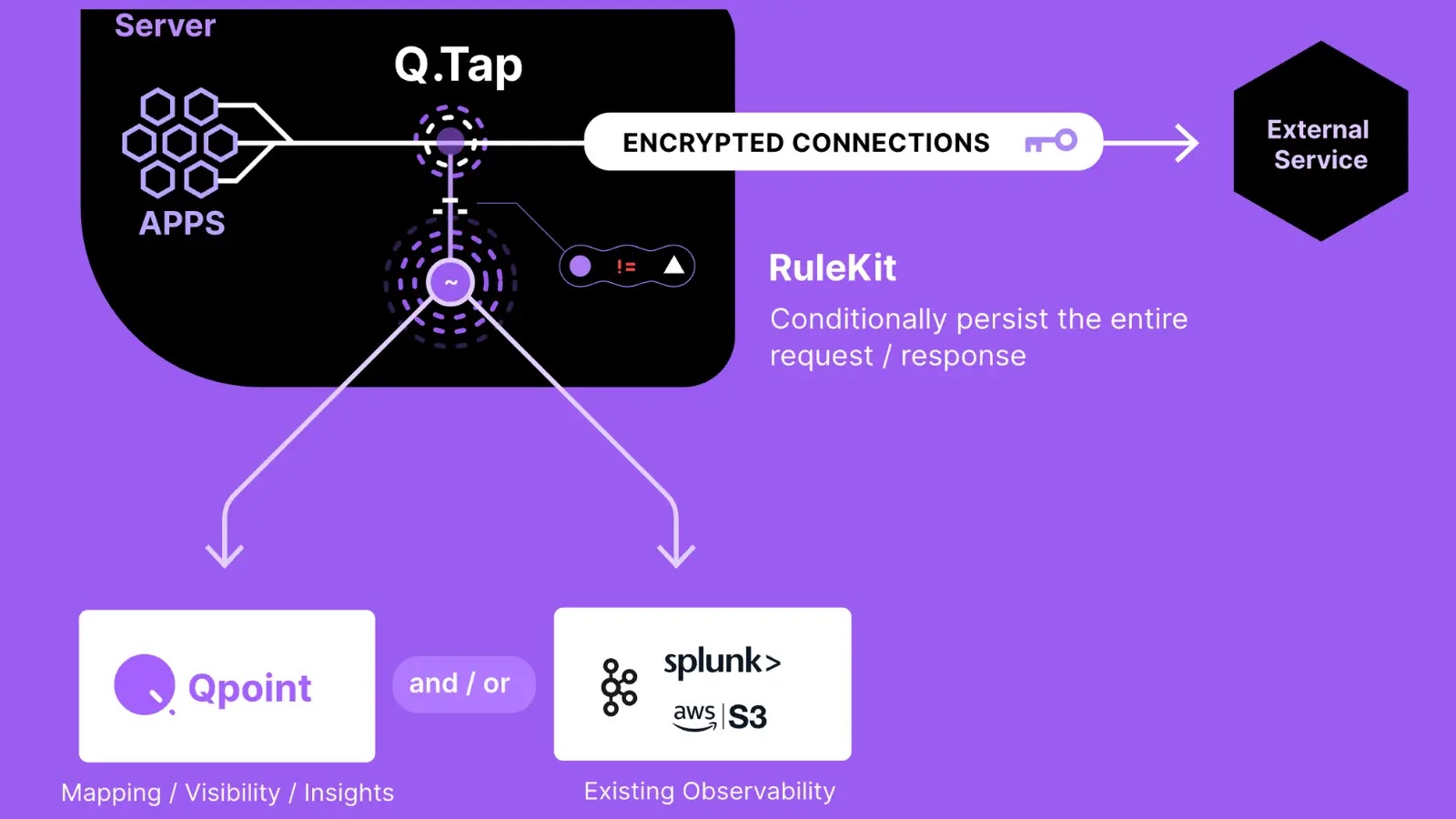
An infection Chain (Supply – Seqrite)
The group’s infrastructure evaluation reveals connections to Aeza Group LLC, a sanctioned internet hosting supplier, indicating deliberate makes an attempt to function inside jurisdictions that complicate attribution and takedown efforts.
The malware’s affect extends past easy information theft, incorporating superior persistence mechanisms and protection evasion strategies that permit extended community entry.
Victims face potential publicity of delicate company communications, strategic planning paperwork, and operational information important to Kazakhstan’s vitality infrastructure.
The marketing campaign’s concentrate on vitality sector entities raises considerations about potential disruption to important nationwide infrastructure and financial stability.
An infection Mechanism and Technical Evaluation
The NoisyBear an infection chain begins with malicious ZIP recordsdata containing three important elements: a decoy doc bearing the official KazMunaiGas emblem, a README.txt file offering execution directions, and a weaponized LNK file named “График зарплат.lnk” (Wage Schedule.lnk).
The malicious shortcut file employs PowerShell as a Residing Off The Land Binary (LOLBIN) to execute refined obtain operations.
Upon execution, the LNK file initiates a PowerShell command that retrieves a malicious batch script named “123.bat” from the distant server “77.239.125.41:8443”.
The downloaded script is strategically positioned within the C:UsersPublic listing, a location chosen for its accessibility and lowered safety scrutiny.
The batch script serves as a secondary loader, downloading PowerShell scripts dubbed “DOWNSHELL” by researchers.
These loaders show superior Anti-Malware Scan Interface (AMSI) bypass strategies, utilizing reflection to govern the System.Administration.Automation.AmsiUtils class.
The malware units the “amsiInitiFailed” flag to persuade PowerShell that AMSI initialization has failed, successfully disabling real-time scanning capabilities for subsequent malicious operations.
The ultimate payload includes course of injection strategies concentrating on explorer.exe, using traditional CreateRemoteThread injection strategies.
The malware employs OpenProcess, VirtualAllocEx, WriteProcessMemory, and CreateRemoteThread API calls to inject Meterpreter reverse shell capabilities, establishing persistent backdoor entry for information exfiltration and distant command execution.
Increase your SOC and assist your staff shield your small business with free top-notch risk intelligence: Request TI Lookup Premium Trial.