In a recent large-scale cyberattack, over 700 web servers running Next.js have been compromised. This surge in attacks has been linked to a hacker group known as UAT-10608, according to cybersecurity experts at Cisco Talos. The attackers have been exploiting a significant security vulnerability called React2Shell, targeting web applications worldwide.
Exploiting React2Shell for Remote Code Execution
The React2Shell vulnerability, identified as CVE-2025-55182, is a critical remote code execution flaw in React Server Components. Attackers leverage this flaw to send crafted web requests to vulnerable servers, leading to unauthorized execution of hidden commands due to inadequate data validation by the server. Worryingly, this attack does not require passwords or user interaction, making it particularly dangerous.
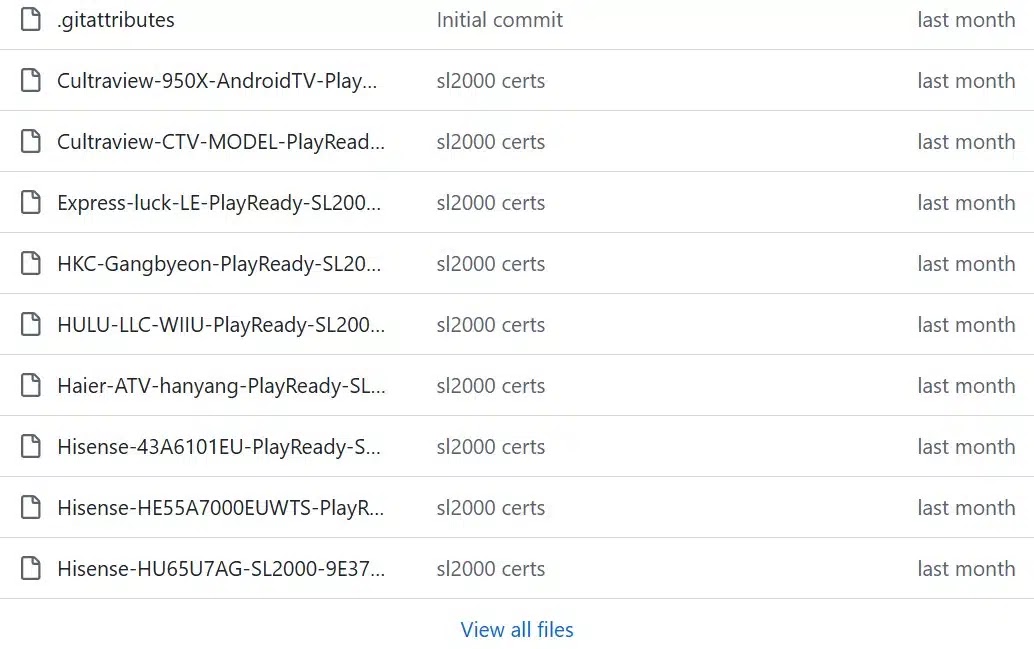
The hacker group employs automated tools to identify and exploit susceptible Next.js servers. Upon finding a target, they deploy the React2Shell exploit to gain unauthorized access, followed by the installation of a malicious script.
Mass Credential Theft and NEXUS Listener
This malicious script operates silently, scanning server files, cloud configurations, and system memory to extract sensitive credentials. These include cloud tokens, database passwords, and more, which are then transmitted to the attackers’ command-and-control server.
To manage the extensive volume of stolen data, the hackers utilize a specialized web dashboard named ‘NEXUS Listener’. Cisco Talos researchers discovered that this tool documented 766 compromised hosts within just a day. The data revealed that over 90% of these hosts had their database credentials pilfered, and nearly 80% lost crucial SSH keys.
Implications and Urgent Response
The ramifications of these breaches are severe. With stolen credentials, attackers can access private user data, financial records, and even take control of entire cloud environments. The compromised SSH keys enable lateral movement across different servers, while stolen GitHub tokens pose a risk of malicious code insertion into software updates.
Organizations using Next.js must act swiftly to mitigate these risks. Immediate patching of the React2Shell vulnerability is crucial. Additionally, companies should change all passwords, API keys, and security tokens if they suspect being targeted. Restricting access to cloud metadata services and monitoring for unusual server activities are also recommended actions.
Stay informed on the latest cybersecurity developments by following us on Google News, LinkedIn, and X. Contact us to share your cybersecurity stories.