A significant security flaw has been identified in Docker Engine, which potentially allows unauthorized access to the host system by bypassing authorization mechanisms. This high-severity vulnerability, known as CVE-2026-34040, has been assigned a CVSS score of 8.8. It emerges from an insufficient fix for a previous critical vulnerability, CVE-2024-41110, discovered in July 2024.
Technical Details of CVE-2026-34040
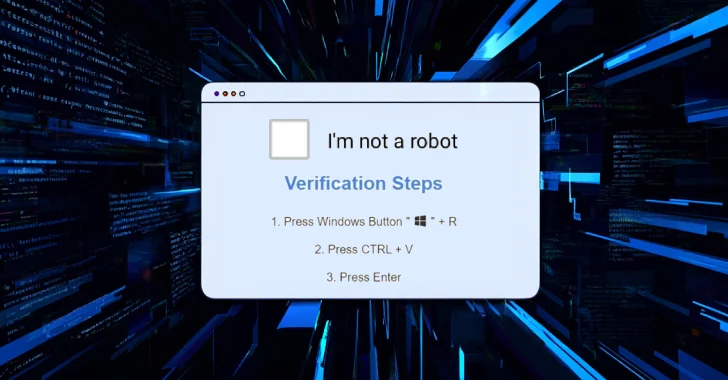
The vulnerability arises when a specially crafted API request is used. This request can cause the Docker daemon to send the request to an authorization plugin without including the request body, which could lead to unauthorized access. If the authorization plugin relies on the request body to make access control decisions, it might inadvertently allow a request it would typically block.
Security researchers Asim Viladi Oglu Manizada, Cody, Oleh Konko, and Vladimir Tokarev are credited for uncovering and reporting this vulnerability. Docker Engine version 29.3.1 includes patches to address this issue.
Potential Exploitation Scenarios
According to Vladimir Tokarev of Cyera Research Labs, the vulnerability is associated with how the previous fix handled oversized HTTP request bodies. An attacker could exploit this by crafting a request that exceeds 1MB, causing it to bypass the authorization plugin and enable the creation of a privileged container with access to the host file system.
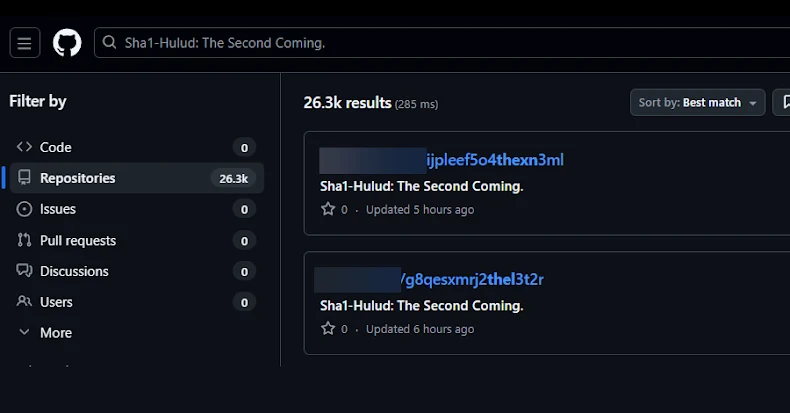
This scenario could grant attackers access to sensitive data like AWS credentials, SSH keys, and Kubernetes configurations. Additionally, AI coding agents could be manipulated to execute harmful code through a prompt injection hidden in a GitHub repository, exploiting the vulnerability to create a privileged container and mount the host file system.
Mitigation Strategies and Recommendations
With potential access to sensitive cloud services and production servers, the vulnerability poses a serious threat. Cyera recommends avoiding reliance on AuthZ plugins that depend on request body inspection, restricting Docker API access to trusted users, and implementing the least privilege principle. Running Docker in rootless mode is advised as it reduces the impact of a compromise.
In environments where rootless mode is not feasible, using –userns-remap can achieve similar UID mapping, limiting the scope of any unauthorized access to unprivileged user levels, thereby reducing the overall risk.
Organizations are urged to update to the latest Docker Engine version to protect against this vulnerability and to review their current security practices to ensure robust defenses against such attacks.