The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has recently highlighted two significant security vulnerabilities impacting ConnectWise ScreenConnect and Microsoft Windows by adding them to its Known Exploited Vulnerabilities (KEV) catalog. This decision comes in response to confirmed instances of active exploitation.
Details of the Vulnerabilities
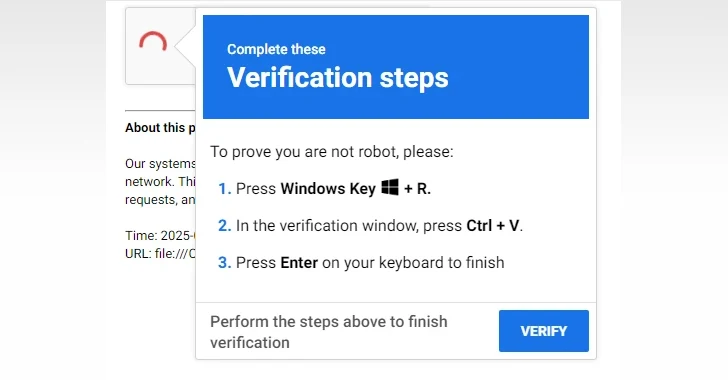
The first vulnerability, identified as CVE-2024-1708, has a CVSS score of 8.4 and involves a path traversal issue in ConnectWise ScreenConnect. This flaw could potentially allow malicious actors to execute remote code or access sensitive data and critical systems. It was rectified in February 2024. The second vulnerability, CVE-2026-32202, which affects the Microsoft Windows Shell, has a CVSS score of 4.3. This security gap could enable unauthorized individuals to carry out network-based spoofing attacks and was patched as of April 2026.
Exploitation and Impact
Microsoft’s update of its advisory on CVE-2026-32202 acknowledged the flaw’s active exploitation shortly before its inclusion in the KEV catalog. Although specific attack methodologies remain undisclosed, Akamai reported that the vulnerability resulted from an incomplete patch for CVE-2026-21510, previously exploited alongside CVE-2026-21513 by the Russian hacking group APT28. This group has targeted Ukraine and European Union nations since late 2025.
In contrast, CVE-2024-1708 has been exploited in conjunction with CVE-2024-1709, a critical authentication bypass flaw rated with a CVSS score of 10.0. Microsoft has identified a China-based threat actor, known as Storm-1175, as being responsible for leveraging these vulnerabilities to deploy the Medusa ransomware.
Response and Mitigation
CVE-2024-1709 was previously added to the KEV catalog by CISA on February 22, 2024. In response, the Federal Civilian Executive Branch (FCEB) agencies are mandated to implement necessary security updates by May 12, 2026, to fortify their network defenses against potential threats.
These developments underscore the critical need for organizations to maintain up-to-date security measures and swiftly apply patches to protect their systems from exploitation. Staying informed about emerging vulnerabilities and taking proactive steps to mitigate risks are essential components of effective cybersecurity strategies.
Looking ahead, the focus remains on enhancing collaborative efforts between agencies and the private sector to prevent and respond to cybersecurity threats effectively, ensuring the protection of sensitive information and infrastructure.