A newly discovered zero-click vulnerability in Android has been revealed in Google’s May 2026 Security Bulletin, posing a significant threat to mobile security. The flaw, identified as CVE-2026-0073, enables attackers to gain full shell access remotely without requiring any interaction from the user.
Details of the Android Zero-Click Vulnerability
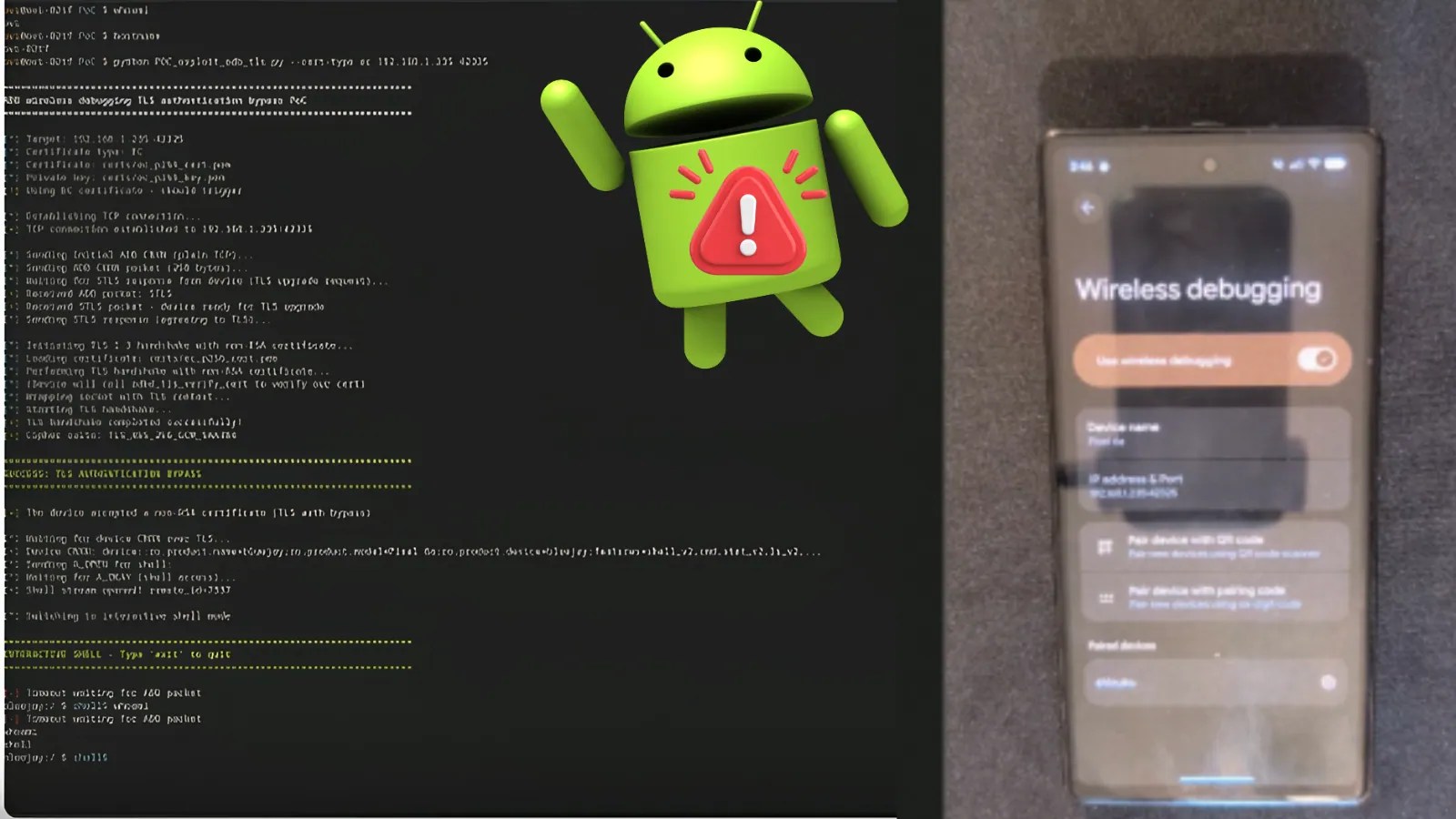
Security experts from BARGHEST have brought to light this critical flaw within Android’s adbd daemon. The vulnerability arises from a cryptographic error in the adbd_tls_verify_cert function found in the auth.cpp file. This error compromises the trust model used during debugging, turning a beneficial developer tool into a potential backdoor for cyber threats.
Technical Breakdown of the Vulnerability
The vulnerability hinges on a logic error during the TLS authentication process. During a wireless ADB connection, the system uses the EVP_PKEY_cmp API to validate a client’s certificate against authorized RSA keys. However, if an attacker uses a non-RSA certificate, the comparison returns -1, which is mistakenly interpreted as a successful match due to a C++ implementation flaw.
To exploit this, an attacker must establish a TCP connection, perform a successful STLS protocol upgrade, and present a malicious certificate. Once bypassed, the attacker gains shell user access, allowing them to extract data, install applications silently, and alter system settings, exposing the device to further risk.
Impacted Devices and Mitigation Strategies
The flaw primarily affects devices running Android versions 14 to 16, especially when certain conditions are met. These include enabled developer options, active wireless debugging, a trust store with a paired RSA host key, and network accessibility to ADB TCP port 5555.
To mitigate this risk, users and administrators are urged to apply the May 2026 security patch immediately. Additionally, disabling wireless debugging on untrusted networks and revoking permissions for unfamiliar debugging hosts can help minimize exposure. Turning off developer options when not needed is also highly recommended to prevent potential network attacks.
Stay informed by following us on Google News, LinkedIn, and X for more updates on cybersecurity threats and protective measures.