Cybersecurity researchers have identified a concerning operation named GemStuffer, which exploits the RubyGems repository to exfiltrate data rather than distribute malware. Over 150 gems have been used in this campaign, where the repository serves as a channel for transmitting scraped data from U.K. council portals.
Uncovering GemStuffer’s Tactics
According to Socket, the suspicious packages are not intended to compromise developers on a large scale. They have minimal download activity, and their payloads are noisy and self-contained. The scripts involved extract data from U.K. local government portals, bundle the gathered responses into .gem archives, and upload them back to RubyGems using preset API keys.
This campaign surfaced alongside RubyGems’ temporary suspension of new account registrations due to a significant malicious attack. Although it is not confirmed whether these incidents are connected, Socket noted that GemStuffer exhibits a similar abuse pattern by using new packages with random names to store scraped data.
Mechanisms of Data Exfiltration
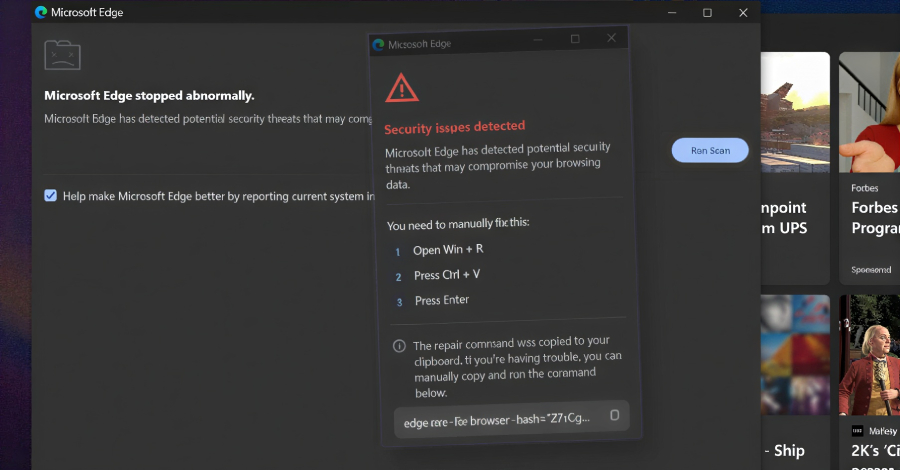
The campaign manipulates RubyGems to stage council data by fetching specific U.K. council portal URLs, packaging HTTP responses into .gem files, and publishing them with embedded credentials. Some payloads create temporary RubyGems credential environments and push gems through the command-line interface, bypassing existing credentials.
Other variants skip the CLI, opting instead to upload archives directly to RubyGems via HTTP POST requests. Once uploaded, attackers can retrieve the data using the ‘gem fetch’ command with the appropriate gem name and version.
Potential Motives and Impact
GemStuffer targets ModernGov portals in Lambeth, Wandsworth, and Southwark, collecting meeting schedules, agenda items, linked PDFs, officer contacts, and RSS feeds. Despite the public availability of this data, the systematic collection suggests a potential aim to demonstrate capabilities against government systems.
Socket speculates that the operation may be a form of registry spam, a proof-of-concept worm, or an attempt to misuse RubyGems as a storage platform. The intentional mechanics involve repeated gem creation, version updates, hardcoded credentials, and direct registry submissions.
The implications of GemStuffer are significant for software supply chains, highlighting the need for heightened vigilance and improved security practices to prevent such exploitation in the future.