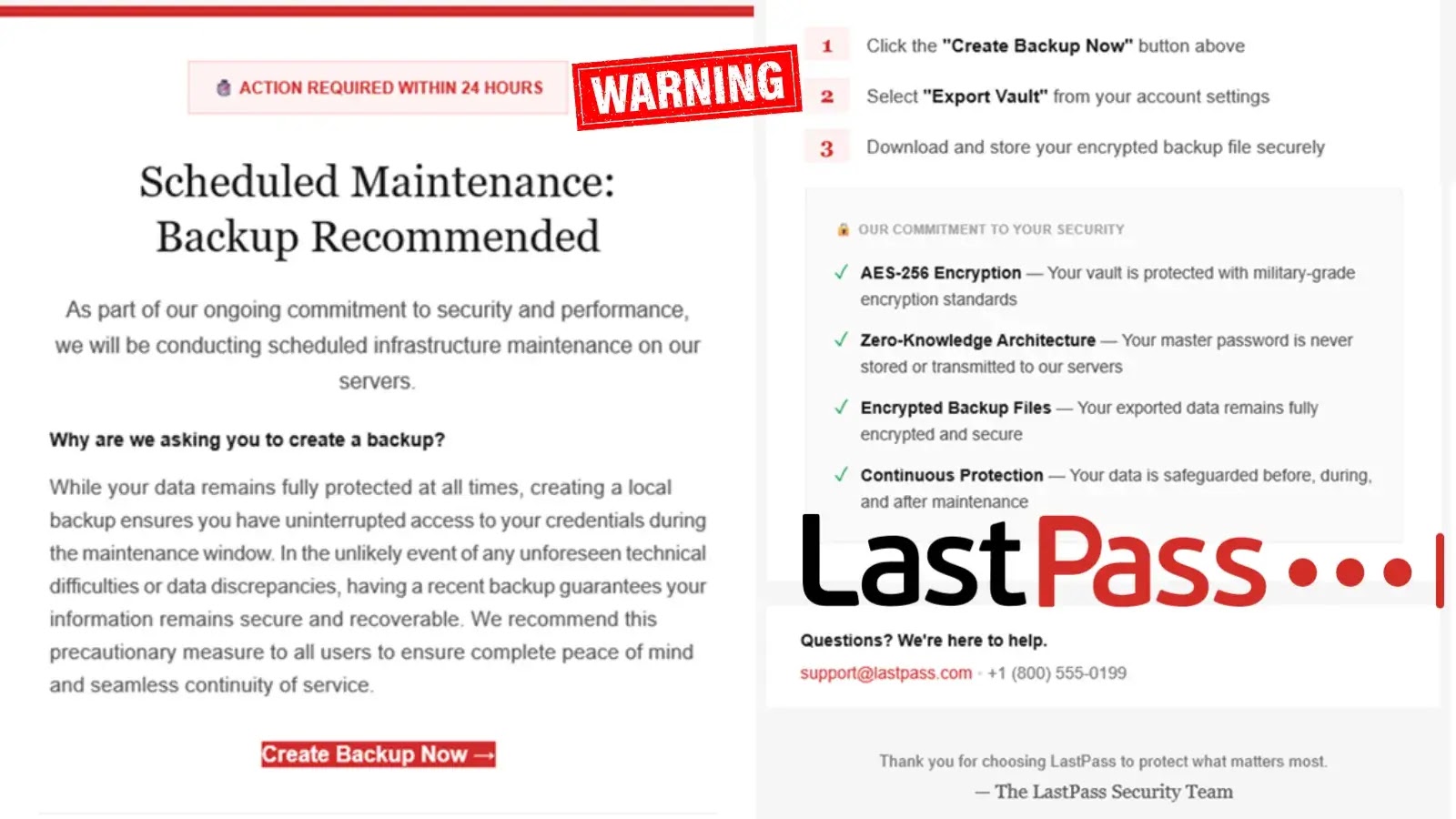
A classy malware marketing campaign has emerged concentrating on unsuspecting customers via weaponized variations of well-liked on-line instruments, significantly Google Translate interfaces.
The Silver Fox risk actors have developed an intricate assault chain that leverages social engineering techniques to ship the infamous Winos Trojan, representing a major evolution in malware distribution strategies that exploit customers’ belief in reliable net providers.
Assault chain (Supply – Medium)
The assault methodology facilities round creating convincing replicas of widely-used purposes and web sites, with attackers establishing faux Google Translate portals, foreign money converters, and software program obtain pages for well-liked purposes like WPS Workplace.
Faux WPS official obtain web site (Supply – Medium)
When customers work together with these malicious websites, they encounter misleading Flash replace prompts that redirect them to attacker-controlled obtain servers internet hosting malicious set up packages.
Knownsec 404 crew researchers recognized this marketing campaign as a part of a broader Silver Fox operation that has been energetic since 2024, with the risk actors demonstrating outstanding adaptability of their social engineering approaches.
The researchers famous that this explicit variant represents a major departure from conventional malware distribution strategies, because it particularly targets customers looking for translation providers and productiveness instruments.
Faux Simple Translation set up package deal (Supply – Medium)
The an infection mechanism reveals subtle technical implementation, with attackers embedding rigorously crafted JavaScript code throughout the phishing web sites.
The malicious script creates hidden enter components and makes an attempt to fetch configuration information from distant JSON recordsdata earlier than displaying faux Flash replace notifications.
The embedded redirect script demonstrates the attackers’ technical proficiency:-
fetch(‘url.json’)
.then(response => response.json())
.then(information => {
const urlToUse = information[0];
doc.physique.addEventListener(‘click on’, perform() {
alert(“检测Flash版本过低,请安装后插件重试!”);
});
window.location.href = urlToUse;
});
Upon profitable set up, the malware deploys a number of elements together with javaw.exe, Microsoftdata.exe, and numerous supporting recordsdata that set up persistent entry to compromised techniques.
The Winos Trojan, masquerading as reliable Microsoft software program, implements complete information theft capabilities together with screenshot seize, keylogging, and clipboard monitoring functionalities.
The marketing campaign’s persistence mechanism entails registry manipulation to make sure long-term system compromise, with the malware writing itself into Home windows startup areas.
Evaluation reveals that the ultimate payload accommodates references to “RexRat4.0.3” in its program database, indicating the usage of commercially accessible distant entry instruments which have been repurposed for cybercriminal actions.
This Silver Fox marketing campaign represents a regarding pattern in malware distribution, the place risk actors more and more depend on social engineering reasonably than technical exploits to realize preliminary compromise, making person schooling and consciousness essential elements of organizational cybersecurity methods.
Combine ANY.RUN TI Lookup together with your SIEM or SOAR To Analyses Superior Threats -> Strive 50 Free Trial Searches