Sep 03, 2025Ravie LakshmananData Breach / Cyber Espionage
An Iran-nexus group has been linked to a “coordinated” and “multi-wave” spear-phishing marketing campaign concentrating on the embassies and consulates in Europe and different areas internationally.
The exercise has been attributed by Israeli cybersecurity firm Dream to Iranian-aligned operators linked to broader offensive cyber exercise undertaken by a gaggle referred to as Homeland Justice.
“Emails had been despatched to a number of authorities recipients worldwide, disguising legit diplomatic communication,” the corporate mentioned. “Proof factors towards a broader regional espionage effort aimed toward diplomatic and governmental entities throughout a time of heightened geopolitical stress.”
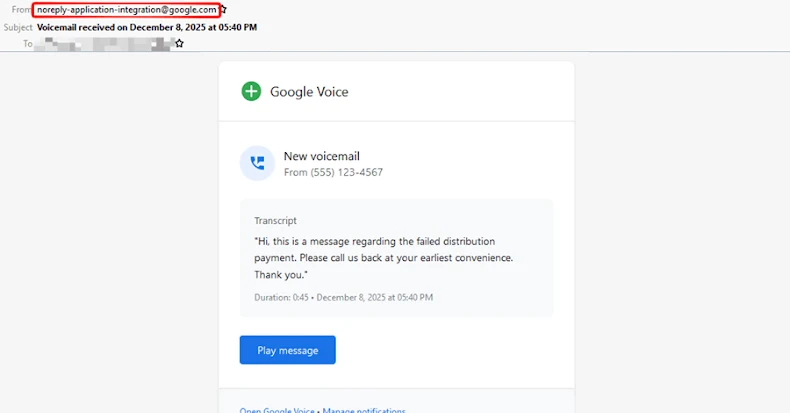
The assault chains contain the usage of spear-phishing emails with themes associated to geopolitical tensions between Iran and Israel to ship a malicious Microsoft Phrase that, when opened, urges recipients to “Allow Content material” with the intention to execute an embedded Visible Fundamental for Functions (VBA) macro, which is accountable for deploying the malware payload.
The e-mail messages, per Dream, had been despatched to embassies, consulates, and worldwide organizations throughout the Center East, Africa, Europe, Asia, and the Americas, suggesting that the exercise solid a large phishing web. European embassies and African organizations are mentioned to have been probably the most closely focused.
The digital missives had been despatched from 104 distinctive compromised addresses belonging to officers and pseudo-government entities to present them an additional layer of credibility. At the least among the emails originated from a hacked mailbox belonging to the Oman Ministry of International Affairs in Paris (*@fm.gov.om).
“The lure content material constantly referenced pressing MFA communications, conveyed authority, and exploited the widespread observe of enabling macros to entry content material, that are the hallmarks of a well-planned espionage operation that intentionally masked attribution,” Dream mentioned.
The tip objective of the assaults is to deploy utilizing the VBA macro an executable that may set up persistence, contact a command-and-control (C2) server, and harvest system info.
Cybersecurity firm ClearSky, which additionally detailed some elements of the marketing campaign late final month, mentioned the phishing emails had been despatched to a number of ministries of international affairs.
“Comparable obfuscation methods had been utilized by Iranian menace actors in 2023 after they focused Mojahedin-e-Khalq in Albania,” it mentioned in a submit on X. “We assess with reasonable confidence that this exercise is linked to the identical Iranian menace actors.”