Sep 18, 2025Ravie LakshmananVulnerability / Browser Safety
Google on Wednesday launched safety updates for the Chrome net browser to deal with 4 vulnerabilities, together with one which it stated has been exploited within the wild.
The zero-day vulnerability in query is CVE-2025-10585, which has been described as a kind confusion subject within the V8 JavaScript and WebAssembly engine.
Kind confusion vulnerabilities can have extreme penalties as they are often weaponized by dangerous actors to set off surprising software program conduct, ensuing within the execution of arbitrary code and program crashes.
Google’s Menace Evaluation Group (TAG) has been credited with discovering and reporting the flaw on September 16, 2025.
As is often the case, the corporate didn’t share any further specifics about how the vulnerability is being abused in real-world assaults, by whom, or the dimensions of such efforts. That is accomplished to forestall different risk actors from exploiting the problem earlier than customers can apply a repair.
“Google is conscious that an exploit for CVE-2025-10585 exists within the wild,” it acknowledged in a terse advisory.
CVE-2025-10585 is the sixth zero-day vulnerability in Chrome that has been both actively exploited or demonstrated as a proof-of-concept (PoC) because the begin of the 12 months. This consists of: CVE-2025-2783, CVE-2025-4664, CVE-2025-5419, CVE-2025-6554, and CVE-2025-6558.
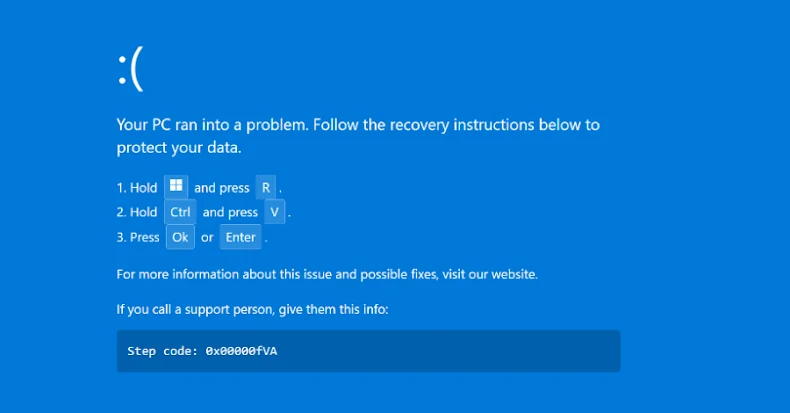
To safeguard in opposition to potential threats, it is suggested to replace their Chrome browser to variations 140.0.7339.185/.186 for Home windows and Apple macOS, and 140.0.7339.185 for Linux. To ensure the newest updates are put in, customers can navigate to Extra > Assist > About Google Chrome and choose Relaunch.
Customers of different Chromium-based browsers, reminiscent of Microsoft Edge, Courageous, Opera, and Vivaldi, are additionally suggested to use the fixes as and after they turn into out there.