Greater than 20,000 malicious IP addresses and domains linked to info stealers have been taken down in an INTERPOL-coordinated operation towards cybercriminal infrastructure.
The four-month worldwide crackdown, dubbed Operation Safe, represents one of the vital coordinated efforts to disrupt infostealer malware networks throughout the Asia-Pacific area.
Throughout Operation Safe, which ran from January to April 2025, regulation enforcement businesses from 26 nations labored systematically to find servers, map bodily networks, and execute focused takedowns.
The operation was organized below the Asia and South Pacific Joint Operations Towards Cybercrime (ASPJOC) Venture, demonstrating the rising worldwide cooperation in combating cyber threats.
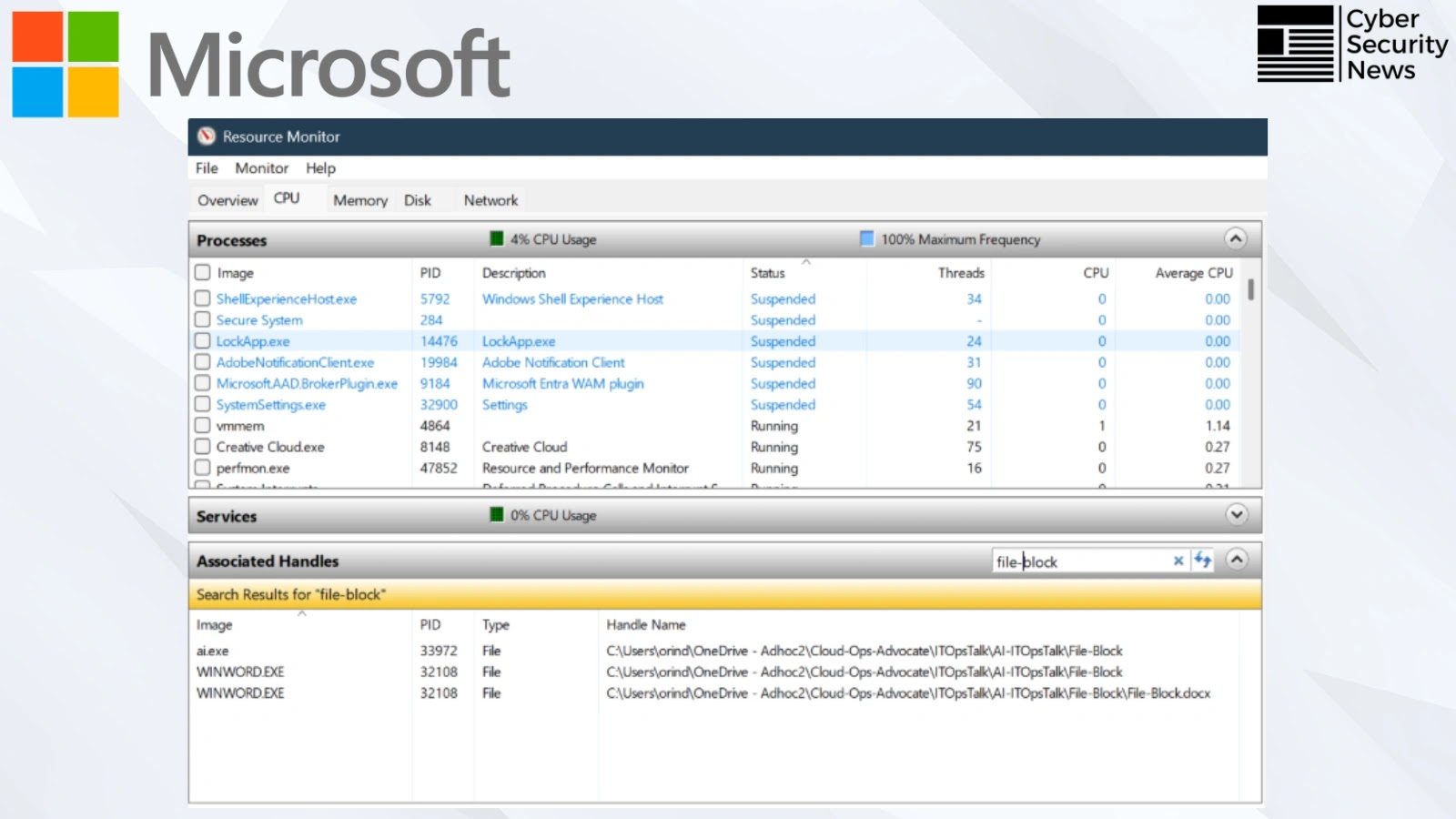
Forward of the operation, INTERPOL cooperated with private-sector companions Group-IB, Kaspersky, and Development Micro to provide complete Cyber Exercise Reviews, sharing vital intelligence with cyber groups throughout Asia. These coordinated efforts resulted in a formidable takedown fee of 79% of recognized suspicious IP addresses.
The intelligence-sharing method proved extremely efficient, with collaborating nations reporting the seizure of 41 servers and over 100 GB of knowledge, in addition to the arrest of 32 suspects linked to unlawful cyber actions.
Operation Safe (Supply: Interpol)
The Infostealer Risk
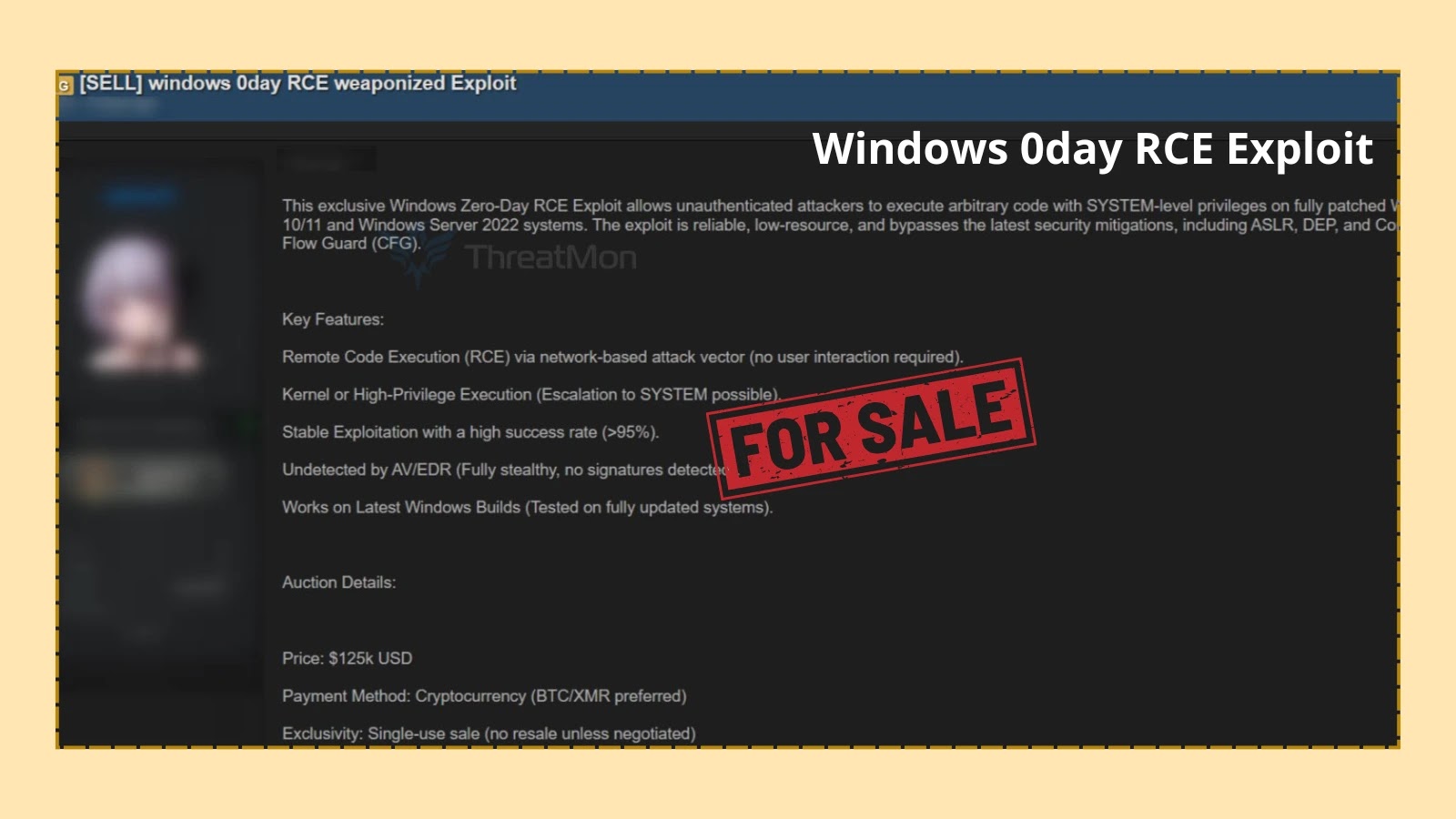
Infostealer malware represents a major software for gaining unauthorized entry to organizational networks. The sort of malicious software program extracts delicate information from contaminated units, sometimes called bots, with stolen info usually together with browser credentials, passwords, cookies, bank card particulars, and cryptocurrency pockets information.
The harvested logs from infostealers are more and more traded on the cybercriminal underground and steadily used as a gateway for additional assaults.
These logs usually allow preliminary entry for ransomware deployments, information breaches, and cyber-enabled fraud schemes similar to Enterprise E mail Compromise (BEC). Following the operation, authorities notified over 216,000 victims and potential victims so they may take instant protecting motion.
The operation achieved vital success throughout a number of nations. Vietnamese police arrested 18 suspects, seizing units from their properties and workplaces. The group’s chief was found with over VND 300 million (USD 11,500) in money, SIM playing cards, and enterprise registration paperwork, pointing to a complicated scheme to open and promote company accounts.
In Sri Lanka and Nauru, coordinated home raids led to the arrest of 14 people – 12 in Sri Lanka and two in Nauru – in addition to the identification of 40 victims.
In the meantime, the Hong Kong Police carried out an in depth evaluation of over 1,700 items of intelligence offered by INTERPOL, figuring out 117 command-and-control servers hosted throughout 89 web service suppliers.
These servers served as central hubs for cybercriminals to launch and handle malicious campaigns, together with phishing, on-line fraud, and social media scams.
Singapore authorities contributed considerably to the operation, with over 1,000 malicious IP addresses primarily based within the nation efficiently taken down by means of joint efforts between the Cybercrime Command and the Cyber Safety Company of Singapore.
Neal Jetton, INTERPOL’s Director of Cybercrime, emphasised the operation’s significance, stating that “INTERPOL continues to assist sensible, collaborative motion towards international cyber threats.
Operation Safe has as soon as once more proven the ability of intelligence sharing in disrupting malicious infrastructure and stopping large-scale hurt to each people and companies”.
The success of Operation Safe builds upon earlier worldwide efforts, together with Operation Synergia II, which dismantled over 22,000 malicious servers globally in 2024.
The operation concerned regulation enforcement businesses from Brunei, Cambodia, Fiji, Hong Kong, India, Indonesia, Japan, Kazakhstan, Kiribati, Korea, Laos, Macau, Malaysia, Maldives, Nauru, Nepal, Papua New Guinea, Philippines, Samoa, Singapore, Solomon Islands, Sri Lanka, Thailand, Timor-Leste, Tonga, Vanuatu, and Vietnam.
Automate menace response with ANY.RUN’s TI Feeds—Enrich alerts and block malicious IPs throughout all endpoints -> Request full entry