The Cybersecurity and Infrastructure Security Agency (CISA) has issued a critical alert concerning a security vulnerability in Ivanti Endpoint Manager Mobile (EPMM). This flaw, identified as CVE-2026-1340, has been added to the agency’s Known Exploited Vulnerabilities (KEV) catalog due to its active exploitation in cyberattacks.
Details of the Security Flaw
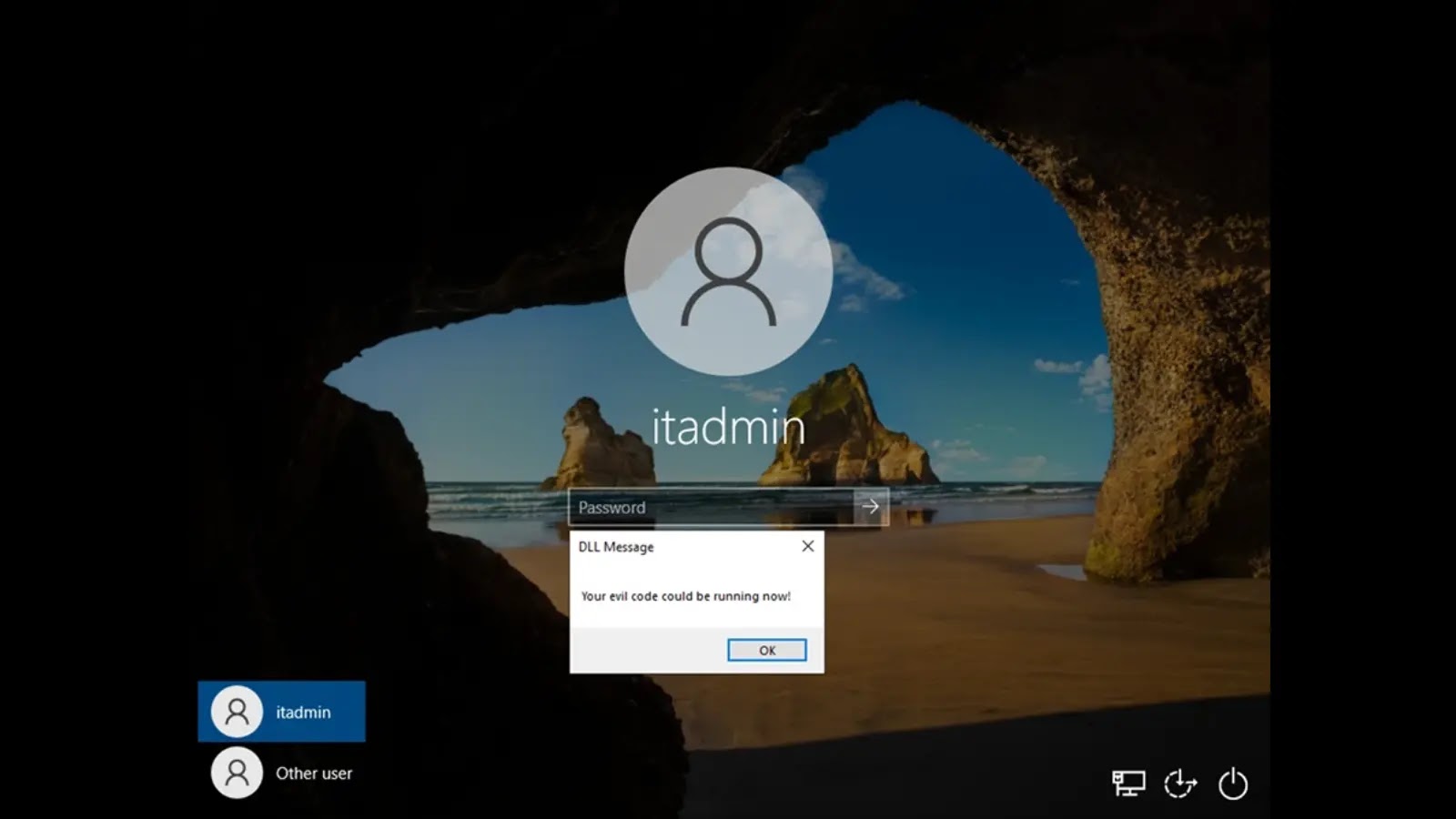
CISA’s recent advisory highlights a significant issue within Ivanti EPMM, where the software fails to adequately restrict or sanitize processed code. This vulnerability is particularly dangerous as it permits unauthenticated remote code execution (RCE) by remote attackers. The absence of the need for a valid username or password makes this flaw a prime target for cybercriminals.
Attackers can exploit this issue by sending carefully crafted requests to vulnerable Ivanti EPMM servers, leading to unauthorized command execution. This vulnerability grants adversaries high-level control over affected systems, enabling theft of sensitive information, malware deployment, and lateral movement within corporate networks.
Implications for Mobile Device Management
Ivanti EPMM, as a mobile device management solution, is an attractive target due to its elevated privileges on corporate devices. Compromised systems could allow attackers to modify security policies or deploy malicious configurations across numerous employee devices. Despite confirmation of the flaw’s exploitation, detailed information on the victims or perpetrators remains limited.
While it is unclear if this vulnerability is part of ongoing ransomware operations, its potential for full system access makes it appealing to advanced persistent threat (APT) groups and financial cybercriminals.
Mandatory Security Measures and Recommendations
CISA added CVE-2026-1340 to the KEV list on April 8, 2026, prompting immediate action. Federal Civilian Executive Branch (FCEB) agencies have been given a deadline of April 11, 2026, to secure their infrastructures under Binding Operational Directive (BOD) 22-01. CISA strongly recommends private-sector organizations adhere to this expedited timeline as well.
Administrators should implement all available patches and mitigations following Ivanti’s guidelines. For those using cloud-based systems, compliance with BOD 22-01 directives for cloud services is essential. If immediate mitigation is not possible, organizations are advised to disconnect and cease using Ivanti EPMM until a resolution is in place.
Stay updated on cybersecurity developments by following us on Google News, LinkedIn, and X. Reach out to feature your stories.