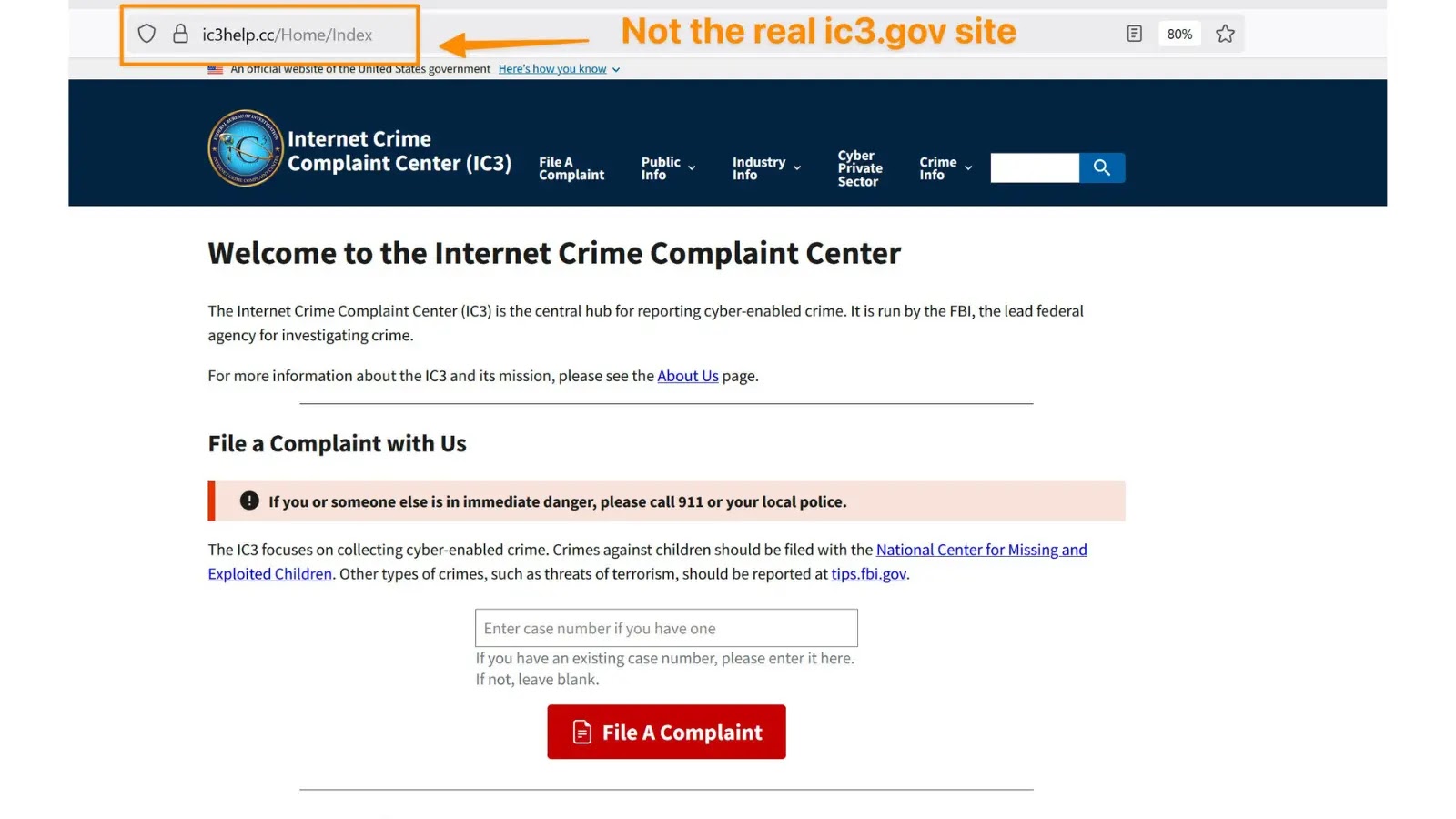
The Federal Bureau of Investigation (FBI) has issued pressing warnings about cybercriminals spoofing the official Web Crime Grievance Middle (IC3) web site to conduct phishing assaults and steal delicate private info.
These faux websites mimic the reputable www.ic3.gov portal with near-perfect replicas, borrowing content material, layouts, and visuals to deceive customers into submitting names, addresses, cellphone numbers, emails, and banking particulars.
Latest screenshots reveal impostor domains like “ichelpindex.com,” flagged as non-official, showing in safety scans comparable to VirusTotal searches for “ic3.”
Risk actors exploit victims’ belief within the IC3, the FBI’s major hub for reporting cybercrimes like fraud and scams. Customers typically land on these fakes by way of engines like google, sponsored hyperlinks, or manipulated on-line boards the place scammers pose as fellow victims, directing site visitors to phony IC3 restoration providers.
In a single variant, fraudsters impersonate IC3 employees by way of Telegram, promising fund restoration however extracting extra information for account takeovers. The FBI famous over 100 such impersonation experiences between late 2023 and early 2025, with spoofed websites surging in 2025, prompting PSAs in April and September.
Recognizing Faux IC3 Websites
Silent Push noticed these phishing pages replicate the actual web site’s welcome message and criticism kind however use altered domains with misspellings or non-.gov top-level domains.
Safety instruments spotlight discrepancies, comparable to suspicious search rankings excluding the official ic3.gov. Victims, believing they’ve filed reputable experiences, unwittingly support additional crimes like monetary theft or id fraud.
IndicatorReal IC3 (www.ic3.gov)Faux Websites DomainEnds in .govAlternate spellings or TLDs like .comAccess MethodType immediately in browserSearch engines, sponsored adsRequestsNo funds for recoveryDemands private/monetary infoSocial MediaNoneFake profiles directing to sitesGraphicsProfessional U.S. gov styleMay have low-quality artifacts
The FBI urges typing www.ic3.gov immediately into browsers, avoiding sponsored search outcomes, and verifying .gov endings. By no means share delicate information on unverified websites, and report suspicions solely by way of the official portal.
malicious web sites
IC3 maintains no social media and by no means requests funds for fund restoration. Latest FBI social posts on November 25 strengthened these alerts amid rising complaints.
Public vigilance stays essential as scammers evolve ways, focusing on prior rip-off victims in search of recourse. By sticking to direct navigation and skepticism, customers can thwart these subtle phishing operations.
Observe us on Google Information, LinkedIn, and X for every day cybersecurity updates. Contact us to characteristic your tales.