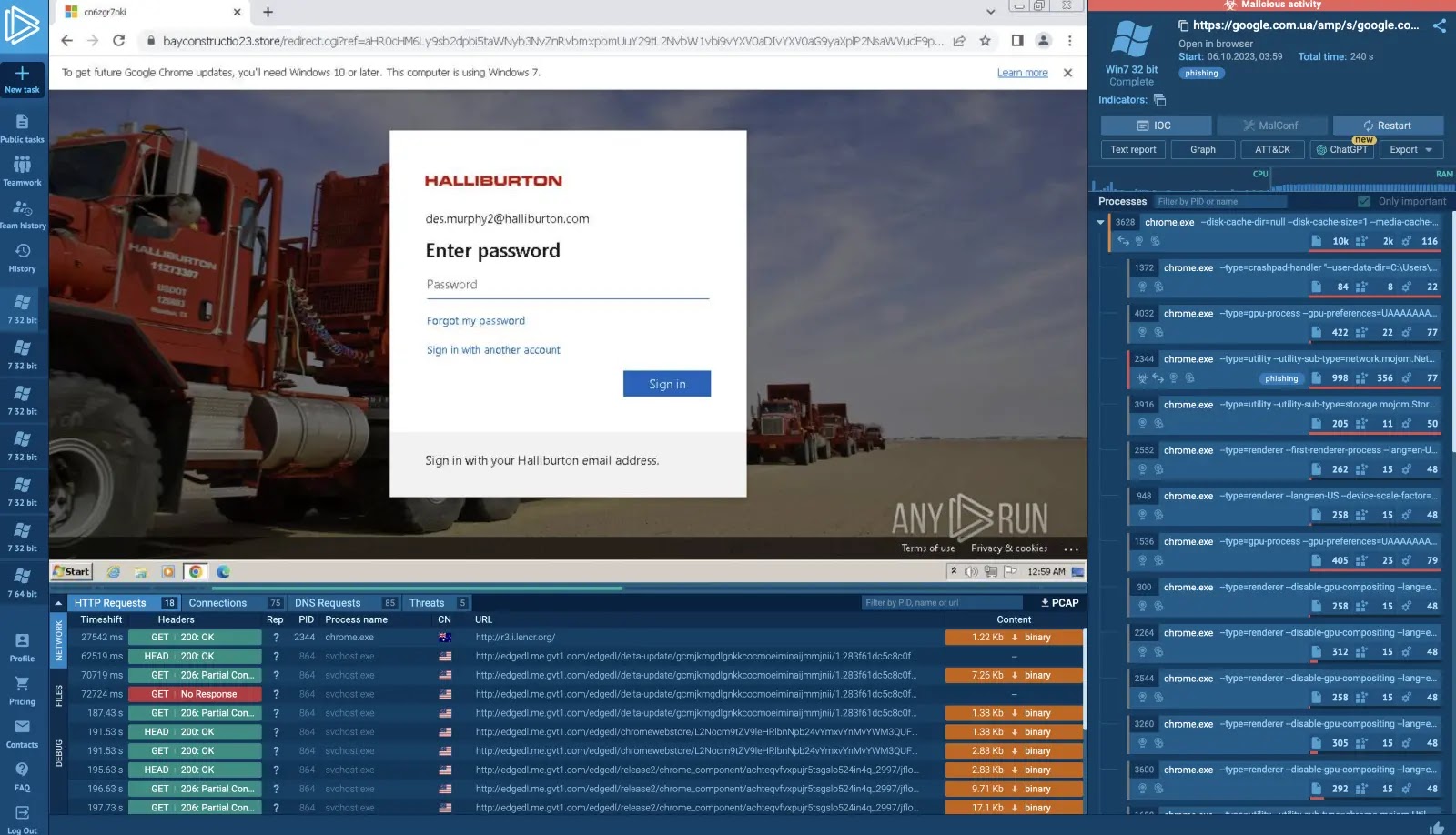
A vital distant code execution vulnerability has been found in LangGraph’s checkpoint serialization system.
The flaw CVE-2025-64439 impacts variations of langgraph-checkpoint earlier than 3.0. It permits attackers to execute arbitrary Python code when untrusted information is deserialized.
The vulnerability resides in LangGraph’s JsonPlusSerializer, the default serialization protocol used for checkpoint persistence.
When the serializer encounters unlawful Unicode surrogate values throughout msgpack serialization, it routinely falls again to JSON mode.
LangGraph Vulnerability
On this fallback state, the deserializer helps a constructor-style format that reconstructs customized objects throughout loading.
The flaw carries a CVSS rating of 8.5, categorised as “Excessive” severity. It falls beneath CWE-502, which covers deserialization of untrusted information vulnerabilities.
An attacker can exploit this mechanism to inject malicious payloads that execute arbitrary features when deserialized.
AttributeDetailsCVE IDCVE-2025-64439Vulnerability TypeRemote Code Execution (RCE)ComponentLangGraph JsonPlusSerializerAffected Versionslanggraph-checkpoint Patched Versionslanggraph-checkpoint >= 3.0SeverityHigh (7.5 CVSS v4)Assault VectorNetwork
The vulnerability primarily impacts functions that meet two circumstances: They permit untrusted or user-supplied information to be endured into checkpoints, they usually use the default JsonPlusSerializer (or explicitly instantiate it).
Purposes processing solely trusted information face considerably decrease sensible threat. LangGraph-API deployments working model 0.5 or later are unaffected.
Attackers can weaponize this vulnerability by way of a rigorously crafted proof-of-concept. That injects a malicious payload structured with particular JSON components: an “lc” worth of two, a “sort” set to “constructor,” and an “id” area pointing to harmful system features like “os.system.”
When the compromised checkpoint is loaded, the deserialization course of routinely executes the embedded command.
LangChain has launched langgraph-checkpoint model 3.0 to deal with this concern.
The repair implements an allow-list for constructor deserialization, limiting permissible paths to explicitly accredited module and sophistication mixtures.
Moreover, saving payloads in JSON format has been deprecated to eradicate this unsafe fallback mechanism. Customers ought to improve instantly to model 3.0 or later.
The replace maintains full compatibility with langgraph 0.3. It requires no code modifications or import adjustments, making the patching course of easy and low-risk for many deployments.
Comply with us on Google Information, LinkedIn, and X for day by day cybersecurity updates. Contact us to characteristic your tales.