A classy cyber espionage marketing campaign concentrating on software program builders has infiltrated two of the world’s largest open supply package deal repositories, with North Korea’s infamous Lazarus Group efficiently deploying 234 malicious packages throughout npm and PyPI ecosystems.
Between January and July 2025, this state-sponsored operation uncovered over 36,000 potential victims to superior malware designed for long-term surveillance and credential theft.
The malicious packages masqueraded as reputable developer instruments, exploiting the inherent belief builders place in open supply ecosystems.
These weaponized elements functioned as espionage implants, engineered to steal delicate secrets and techniques, profile goal hosts, and set up persistent backdoors into vital infrastructure programs.
The marketing campaign represents a strategic evolution in nation-state cyber warfare, remodeling on a regular basis improvement workflows into assault vectors.
Sonatype analysts recognized the menace actor because the Lazarus Group, also called Hidden Cobra, a North Korean state-sponsored collective related to the Reconnaissance Normal Bureau.
This group’s decade-long prison portfolio consists of high-profile assaults such because the 2014 Sony Footage breach, the 2016 Bangladesh Financial institution heist, and the devastating 2017 WannaCry ransomware outbreak.
Most lately, they orchestrated the $1.5 billion ByBit cryptocurrency theft in 2025. The assault methodology leveraged a number of vital vulnerabilities inside open supply ecosystems.
Builders routinely set up packages with out complete verification or sandboxing protocols, whereas automated CI/CD programs propagate malicious dependencies all through improvement pipelines with out human oversight.
The decentralized nature of many well-liked initiatives, typically maintained by only one or two people, creates alternatives for impersonation and compromise.
Persistence and Evasion Mechanisms
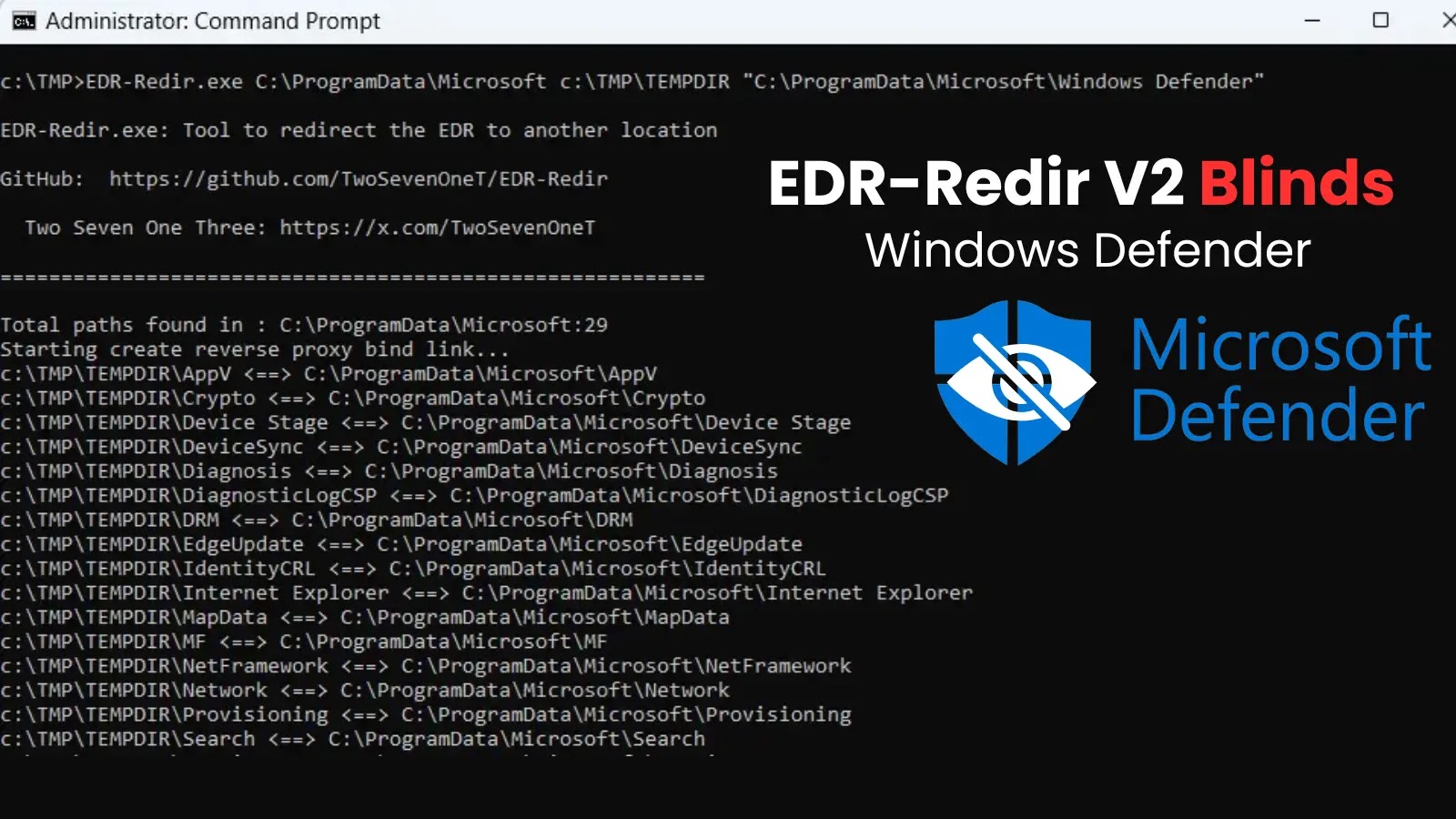
The Lazarus Group employed subtle persistence ways centered on modular payload supply and infrastructure evasion strategies.
Their malware utilized a multi-stage an infection course of, the place preliminary package deal set up triggered dormant code that might activate throughout subsequent improvement actions.
The malicious elements built-in seamlessly with reputable improvement instruments, making detection extraordinarily difficult by typical safety scanning strategies.
The persistent backdoors established by these packages created long-term entry channels that remained undetected for prolonged intervals, permitting steady information exfiltration from compromised developer environments containing delicate credentials, API tokens, and proprietary supply code.
Combine ANY.RUN TI Lookup along with your SIEM or SOAR To Analyses Superior Threats -> Attempt 50 Free Trial Searches