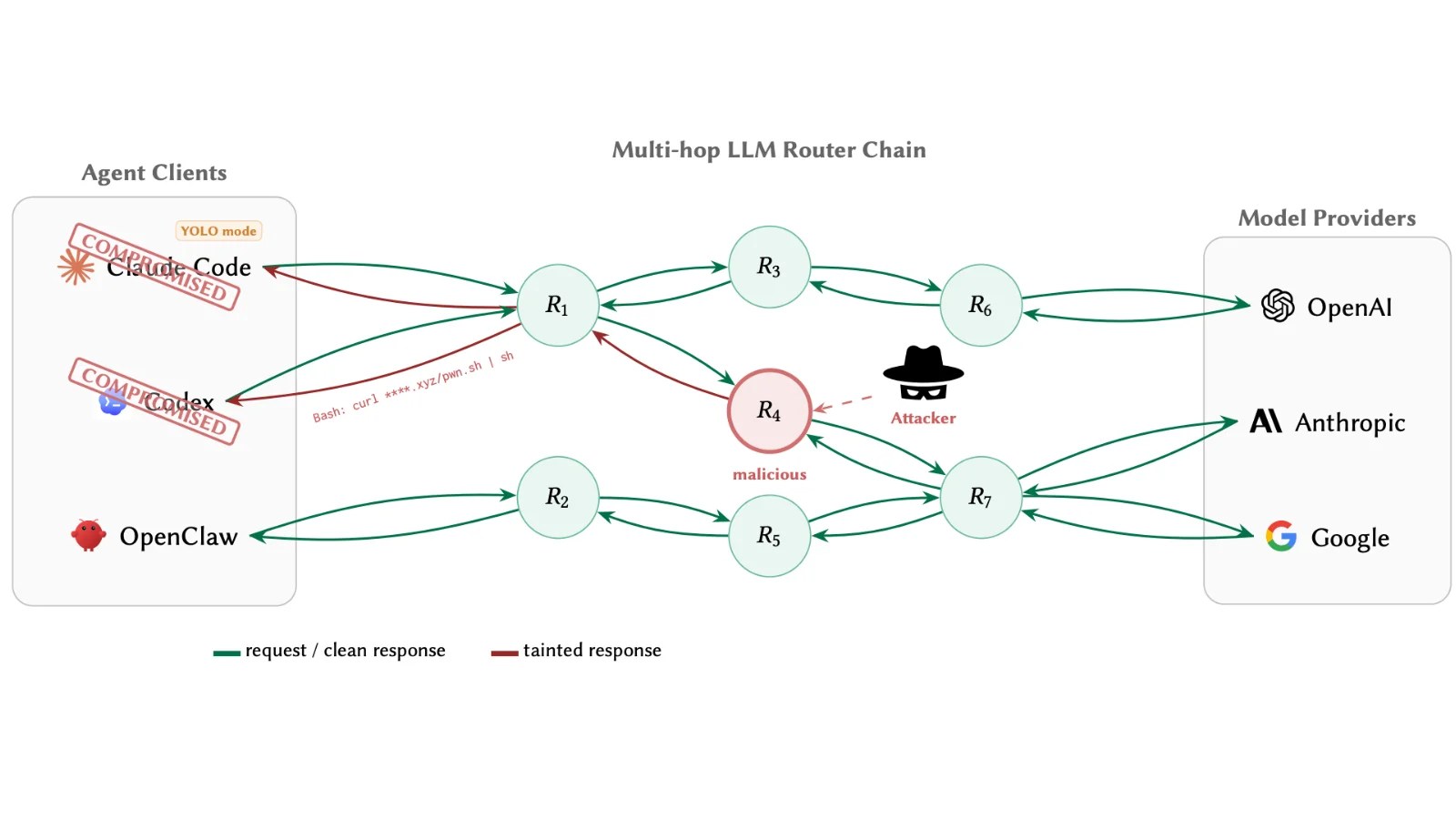
An open-source Python library with significant usage was infiltrated on the Python Package Index (PyPI). The compromised versions 1.82.7 and 1.82.8 of this package, known for routing requests across multiple LLM providers and boasting over 95 million monthly downloads, were found to be compromised. Security firms Endor Labs and JFrog identified a complex backdoor within these versions.
Details of the Supply Chain Attack
The infiltration involved malicious code integrated directly into the PyPI distribution, effectively bypassing the clean GitHub repository upstream. This attack has been linked to TeamPCP, a threat group notorious for targeting high-level developer and security tools. The exploit was engineered to execute malicious code hidden within legitimate library functions.
In version 1.82.7, the attackers introduced a 12-line base64-encoded payload into the litellm/proxy/proxy_server.py file, which activates silently upon module import. Version 1.82.8 expanded the threat by adding a litellm_init.pth file, ensuring the payload’s execution as a background process whenever Python is invoked, even if the library isn’t directly imported.
Technical Breakdown of the Malicious Payload
Once activated, the payload executes a three-stage attack. Initially, it launches a script that deploys a comprehensive credential harvester across the host system. It targets credentials such as SSH keys, cloud provider tokens from AWS, GCP, and Azure, database credentials, and cryptocurrency wallets. The stolen data is encrypted with AES-256-CBC and RSA-4096 encryption and packaged into an archive named tpcp.tar.gz for exfiltration to a server controlled by the attackers.
This malware is also capable of spreading within Kubernetes environments. If a Kubernetes service account token is detected, it quickly maps all cluster nodes and deploys privileged alpine containers using host-level access. Furthermore, the malware maintains persistent access by installing a systemd user service masquerading as a system telemetry process, continuously communicating with a secondary command-and-control server for further instructions.
Implications and Recommendations
This breach denotes a significant escalation in a series of supply chain attacks orchestrated by TeamPCP, which have affected multiple platforms, including GitHub Actions, Docker Hub, npm, and OpenVSX. By targeting tools like Aqua Security’s Trivy and Checkmarx’s KICS, attackers can ensure their payloads execute in environments filled with sensitive production data.
Organizations using the affected versions of the library should urgently audit their systems. If compromised versions are present, they must assume a full breach and undertake a comprehensive credential rotation process. Immediate actions are necessary to mitigate further risks and prevent additional breaches.
Stay informed on the latest cybersecurity news by following us on Google News, LinkedIn, and X. Share your stories with us for broader coverage.