The cybercrime group known as ShinyHunters has allegedly claimed responsibility for multiple data breaches targeting Cisco Systems, Inc. The breaches reportedly compromised over 3 million Salesforce records, along with sensitive internal corporate data such as GitHub repositories and AWS S3 buckets.
Details of the Alleged Breach
Security researcher Dominic Alvieri has highlighted that ShinyHunters issued a ‘FINAL WARNING’ to Cisco on their data leak site, demanding contact by April 3, 2026, to avoid public data exposure. The breach listing, which was updated on March 31, 2026, points to over 3 million records being compromised through Salesforce CRM, Salesforce Aura, and AWS environments.
ShinyHunters, identified as a black-hat hacker group active since 2019, has been linked to a string of data theft and extortion activities. They operate under aliases like UNC6040 and UNC6395, often employing techniques such as vishing to manipulate employees into granting unauthorized OAuth token access to malicious applications.
Implications and Threats
According to threat intelligence from Resecurity, the data allegedly stolen from Cisco primarily originates from its Salesforce environment, including information related to Cisco’s customers and employees. The records also reportedly involve personnel from the FBI, DHS, DISA, IRS, NASA, and other international government agencies, suggesting potential risks for targeted attacks.
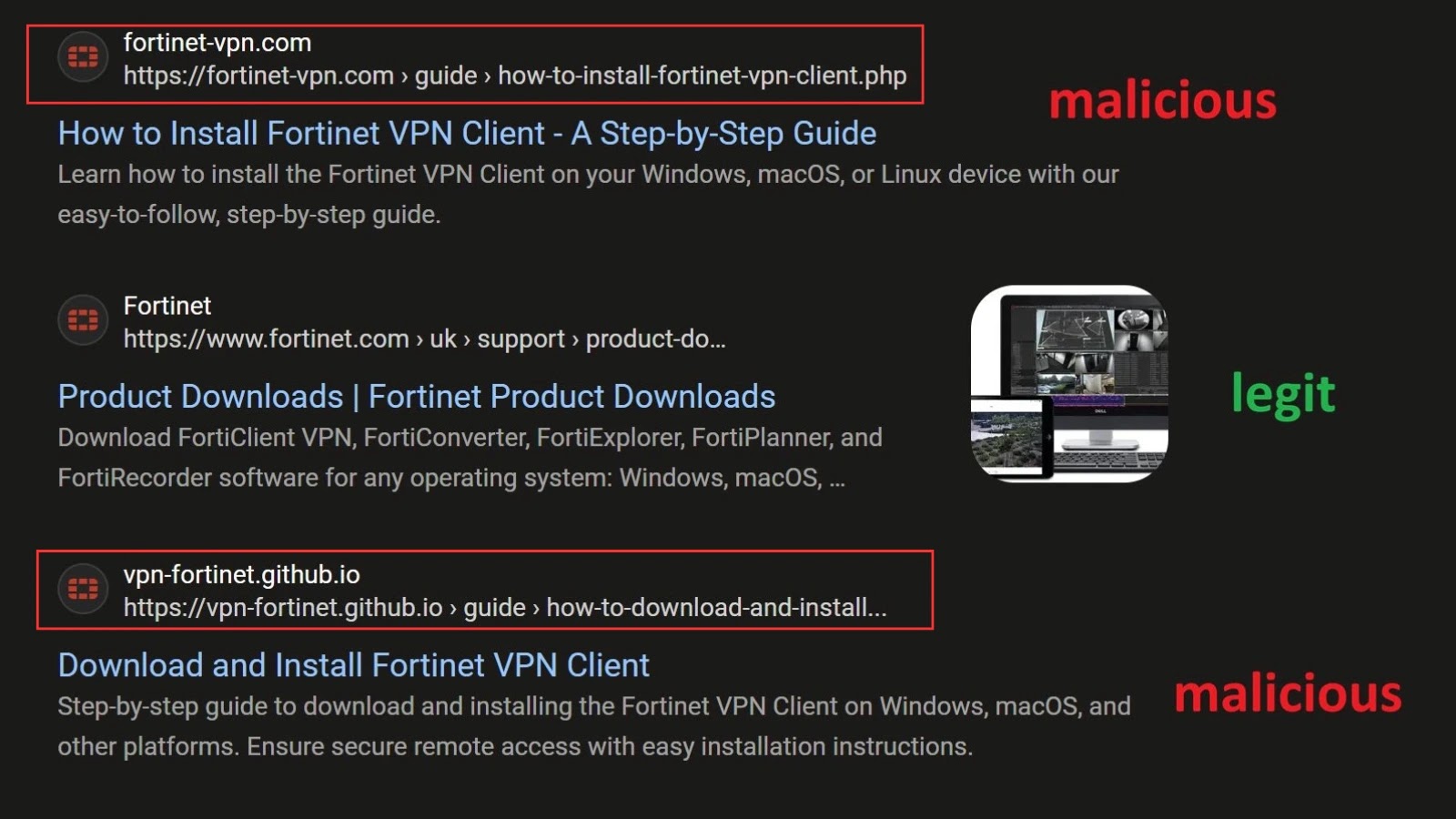
The group’s tactics involve deceiving support employees to authorize malicious Salesforce-connected apps using OAuth tokens, allowing them to bypass security measures like MFA. The subsequent misuse of these tokens enables the exfiltration of sensitive information such as AWS keys and passwords.
Recent Breach History and Recommendations
Cisco’s recent history includes an October 2024 breach where actor IntelBroker allegedly accessed 4.5 TB of data from public-facing environments. Although Cisco confirmed no core systems were breached, certain files were inadvertently exposed due to configuration errors. The company also faced a CRM data breach in August 2025 linked to ShinyHunters.
The ShinyHunters group has a history of targeting major companies, previously claiming attacks on entities like Snowflake and Google. Security experts recommend that organizations immediately review OAuth-connected apps, enforce access controls, and monitor for unauthorized activity to mitigate similar threats.
As of now, Cisco has not released an official statement regarding the latest claims made by ShinyHunters in March 2026. Follow our updates on Google News, LinkedIn, and X for the latest cybersecurity developments.