A development team in Mexico is grappling with a financial crisis after a stolen Google Cloud API key resulted in unauthorized charges totaling $82,314.44 in just 48 hours. This incident highlights the critical importance of securing cloud credentials.
Incident Overview
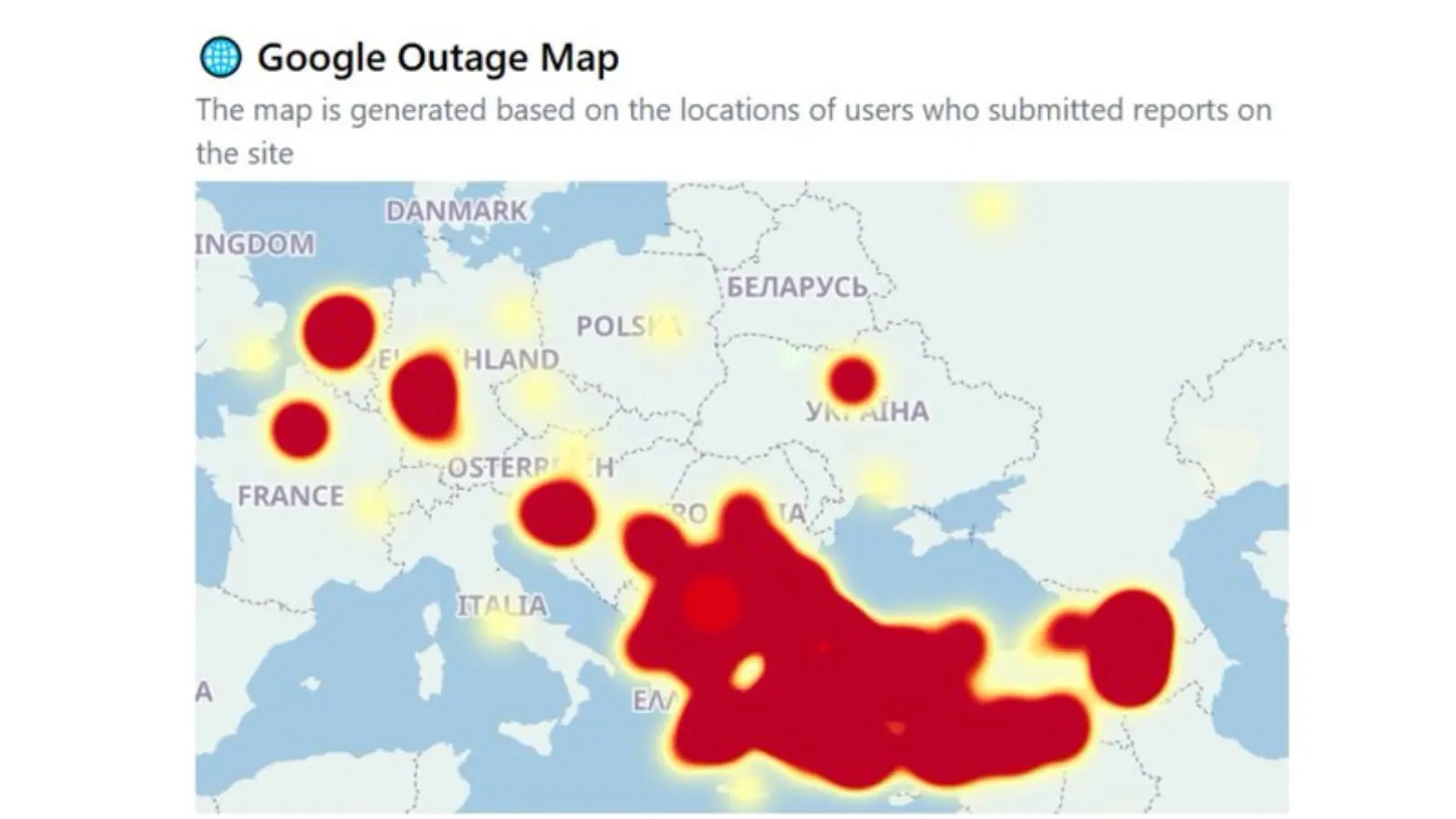
Between February 11 and 12, malicious actors exploited the team’s credentials to excessively access the ‘Gemini 3 Pro Image’ and ‘Gemini 3 Pro Text’ endpoints. This led to an unprecedented 455-fold increase over their typical $180 monthly bill. The developers suspect this breach is part of a larger pattern of international actors targeting U.S. AI models for data extraction.
Security Measures and Challenges
Despite quickly revoking the compromised key, updating their credentials, and tightening Identity and Access Management (IAM) settings, the team encountered significant hurdles when seeking assistance from customer support. Google Cloud representatives emphasized the ‘Shared Responsibility Model,’ indicating that the developers were responsible for securing their credentials, a common issue exacerbated by insecure default settings.
A recent report by Truffle Security noted the exposure of nearly 3,000 legacy Google API keys on public websites. These keys, often used for basic services like Google Maps, can become powerful AI credentials if not properly restricted.
Preventative Measures and Solutions
The incident underscores the necessity for developers to implement robust security measures. Google Cloud’s default settings do not automatically enforce billing limits, leaving accounts vulnerable to exploitation. Users must manually set spending caps and API restrictions to safeguard against unauthorized access and excessive charges.
In previous instances, Google has reversed substantial API charges when users provided comprehensive evidence of unauthorized access, including usage logs and police reports. Nonetheless, proactive configuration checks remain essential for avoiding devastating financial impacts.
Google has taken steps to improve security by automatically disabling exposed service account keys found on public platforms like GitHub. However, this does not address keys stolen directly from developer environments, necessitating vigilant security practices.
Stay informed on the latest cybersecurity developments by following us on Google News, LinkedIn, and X. Contact us to share your stories and insights.