How to Use Disposable Email Addresses
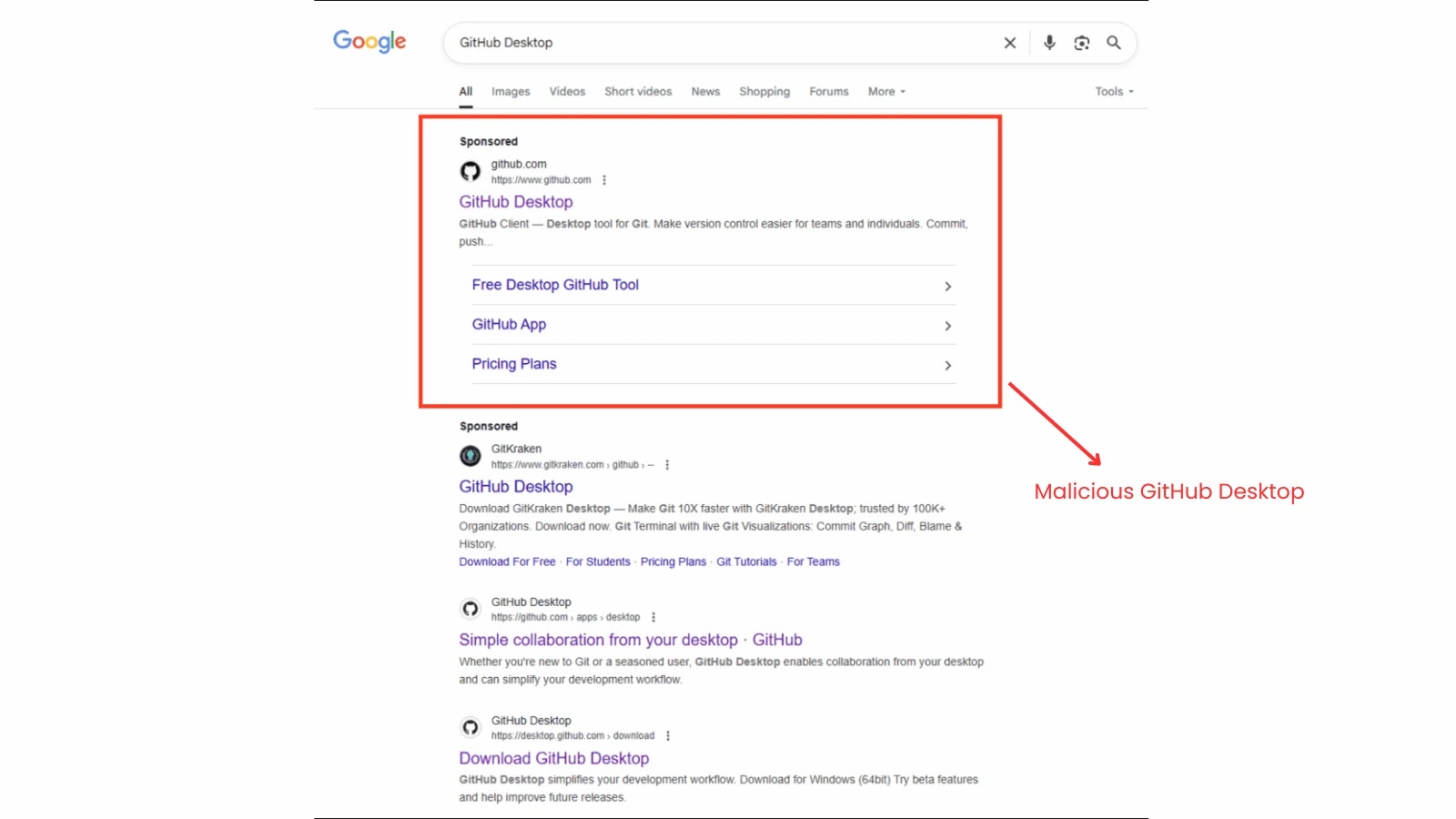
In today’s digital world, privacy is more important than ever. Have you ever signed up for a service only to be bombarded with spam? That’s where disposable email addresses come into play. They act like a shield, protecting your personal email from unwanted attention. Think of them as a temporary phone number. You can give…