Shortly after AI search engine firm Perplexity launched its Comet AI browser, risk actors tried to capitalize on it by luring customers to fraudulent domains and pretend purposes, risk intelligence agency BforeAI reviews.
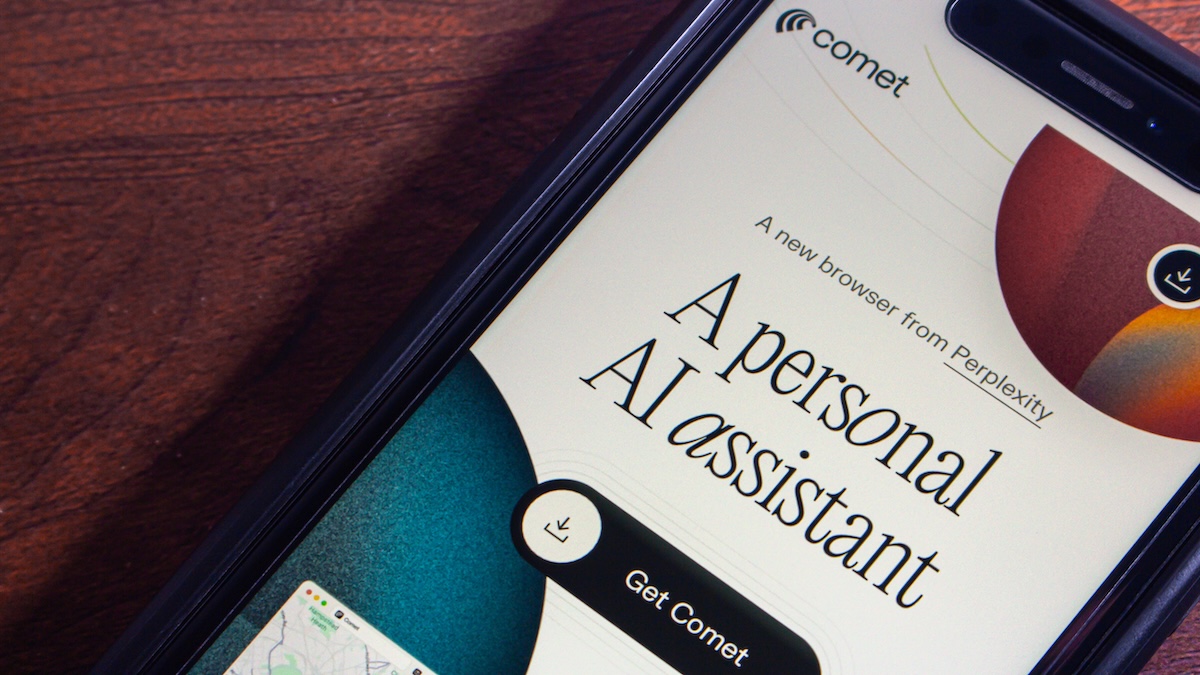
Launched in July, Comet is a Chromium-based browser that integrates Perplexity’s AI assistant, providing assist for automating duties, organizing emails, and researching the online.
Starting August, BforeAI noticed a rise in fraudulent domains selling an executable model of the browser out there for obtain by way of third-party web sites.
Evaluation of over 40 suspicious domains confirmed the usage of typo-squatting, model impersonation, and misleading ads to lure customers to the fraudulent web sites.
The risk actors behind this coordinated marketing campaign used a number of key phrase variations containing ‘comet’, ‘AI’, ‘browser’, ‘perplexity’, and ‘obtain’.
Eight of the domains had been registered after Comet was launched, together with cometai.website, cometaibrowser.com, perplexitycomet-ai.com, cometbrowser.web, and aicometbrowser.com, that are thought-about critical- and high-level threats.
The cometai.web area, the risk intelligence agency notes, has been parked for $9,999 on GoDaddy.
Moreover, BforeAI recognized two critical-level cell software threats within the Google Play Retailer, equivalent to Comet AI Atlas App Information, which immediately impersonates the browser.Commercial. Scroll to proceed studying.
A fraudulent iOS software was additionally recognized, and Perplexity CEO Aravind Srinivas warned of its existence earlier this month.
“The Comet app presently on iOS App Retailer is faux and spam and never from Perplexity,” his public warning reads.
The risk intelligence agency additionally found Google adverts selling fraudulent Comet downloads and social media adverts that directed to faux websites, and linked them to the identical marketing campaign.
“The timing of area registrations carefully follows Comet’s launch timeline, indicating opportunistic cybercriminals monitoring for rising know-how tendencies. Using worldwide registrars, privateness safety companies, and parking pages suggests coordination amongst risk actors,” BforeAI notes.
Associated: AI Sidebar Spoofing Places ChatGPT Atlas, Perplexity Comet and Different Browsers at Danger
Associated: Browser Extensions Pose Severe Risk to Gen-AI Instruments Dealing with Delicate Knowledge
Associated: Browser Safety Beneath Siege: The Alarming Rise of AI-Powered Phishing
Associated: The Shadow AI Surge: Research Finds 50% of Employees Use Unapproved AI Instruments