Dec 18, 2025Ravie LakshmananMalware / Cloud Safety
A beforehand undocumented China-aligned menace cluster dubbed LongNosedGoblin has been attributed to a collection of cyber assaults concentrating on governmental entities in Southeast Asia and Japan.
The top aim of those assaults is cyber espionage, Slovak cybersecurity firm ESET stated in a report revealed at present. The menace exercise cluster has been assessed to be energetic since not less than September 2023.
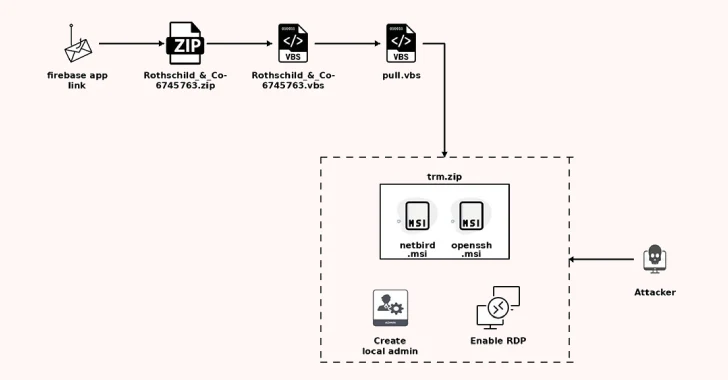
“LongNosedGoblin makes use of Group Coverage to deploy malware throughout the compromised community, and cloud companies (e.g., Microsoft OneDrive and Google Drive) as command and management (C&C) servers,” safety researchers Anton Cherepanov and Peter Strýček stated.
Group Coverage is a mechanism for managing settings and permissions on Home windows machines. In keeping with Microsoft, Group Coverage can be utilized to outline configurations for teams of customers and shopper computer systems, in addition to handle server computer systems.
The assaults are characterised by means of a diverse customized toolset that primarily consists of C#/.NET purposes –
NosyHistorian, to gather browser historical past from Google Chrome, Microsoft Edge, and Mozilla Firefox
NosyDoor, a backdoor that makes use of Microsoft OneDrive as C&C and executes instructions that enable it to exfiltrate information, delete information, and execute shell instructions
NosyStealer, to exfiltrate browser information from Google Chrome and Microsoft Edge to Google Drive within the type of an encrypted TAR archive
NosyDownloader, to obtain and run a payload in reminiscence, reminiscent of NosyLogger
NosyLogger, a modified model of DuckSharp that is used to log keystrokes
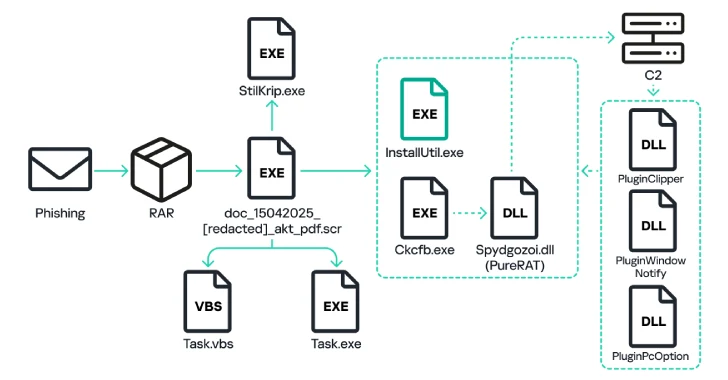
NosyDoor execution chain
ESET stated it first detected exercise related to the hacking group in February 2024 on a system of a governmental entity in Southeast Asia, ultimately discovering that Group Coverage was used to ship the malware to a number of methods from the identical group. The precise preliminary entry strategies used within the assaults are presently unknown.
Additional evaluation has decided that whereas many victims have been affected by NosyHistorian between January and March 2024, solely a subset of those victims have been contaminated with NosyDoor, indicating a extra focused method. In some circumstances, the dropper used to deploy the backdoor utilizing AppDomainManager injection has been discovered to comprise “execution guardrails” which might be designed to restrict operation to particular victims’ machines.
Additionally employed by LongNosedGoblin are different instruments like a reverse SOCKS5 proxy, a utility that is used to run a video recorder to seize audio and video, and a Cobalt Strike loader.
The cybersecurity firm famous that the menace actor’s tradecraft shares tenuous overlaps with clusters tracked as ToddyCat and Erudite Mogwai, however emphasised the dearth of definitive proof linking them collectively. That stated, the similarities between NosyDoor and LuckyStrike Agent and the presence of the phrase “Paid Model” within the PDB path of LuckyStrike Agent have raised the likelihood that the malware could also be bought or licensed to different menace actors.
“We later recognized one other occasion of a NosyDoor variant concentrating on a company in an E.U nation, as soon as once more using totally different TTPs, and utilizing the Yandex Disk cloud service as a C&C server,” the researchers famous. “Using this NosyDoor variant means that the malware could also be shared amongst a number of China-aligned menace teams.”