The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has recently included a significant Linux security vulnerability in its Known Exploited Vulnerabilities (KEV) list. This move follows confirmation of its active exploitation across various systems.
Understanding the Linux Kernel Flaw
Identified as CVE-2026-31431, this vulnerability carries a CVSS score of 7.8, signaling its criticality. The flaw enables local users without privileged access to escalate their rights to root level. Originating from a logic error in the Linux kernel’s authentication cryptographic template, it is exploited via a 732-byte Python-based script. This issue, known as ‘Copy Fail,’ emerged from three separate kernel changes made in 2011, 2015, and 2017.
Linux distributions released since 2017 are vulnerable, allowing unauthorized users to alter the in-memory page cache of executable files, leading to potential code execution with elevated privileges. Google-owned Wiz highlighted the risk, emphasizing how modifications to this cache can inject malicious code into privileged executables.
Impact on Cloud and Container Environments
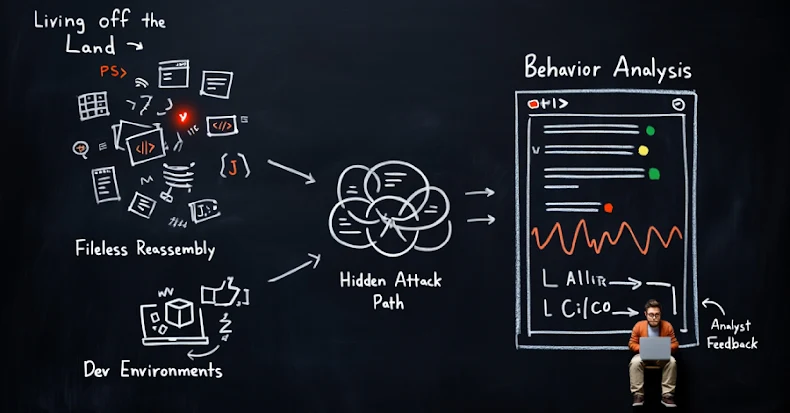
The widespread use of Linux in cloud infrastructures amplifies the implications of this vulnerability. Security firm Kaspersky has pointed out its severe threat to containerized environments like Docker and Kubernetes, which can unwittingly permit access to the AF_ALG subsystem, worsening the risk.
According to Kaspersky, the exploit’s simplicity, requiring no advanced techniques such as race conditions, makes it accessible to less sophisticated attackers. Detection is challenging since the exploit leverages legitimate system calls, mimicking normal application operations.
Security Recommendations and Future Risks
CISA has not disclosed specifics on how the vulnerability is being exploited but warns of possible increased malicious activity. Microsoft Defender’s Security Team has noted preliminary testing that could lead to broader exploitation. Exploiting this flaw involves gaining initial access through means such as SSH or compromised containers before executing the exploit.
Federal Civilian Executive Branch (FCEB) agencies are urged to implement patches by mid-May 2026. Organizations unable to patch immediately should consider disabling vulnerable features, enforcing network segmentation, and tightening access controls to mitigate risks.
With fully functional exploit proofs available in open-source repositories, the urgency for addressing this vulnerability is paramount. Proactive security measures and timely updates are crucial to safeguarding systems against potential breaches.