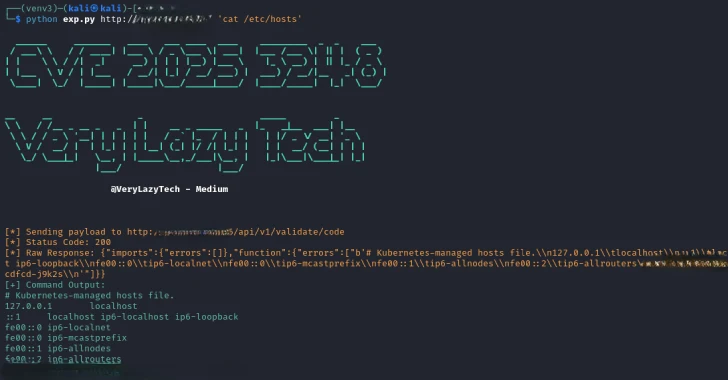
Cybersecurity researchers have recently identified and disclosed serious security vulnerabilities within the n8n workflow automation platform. These flaws, now addressed, posed significant risks, enabling arbitrary command execution. Among the critical vulnerabilities are CVE-2026-27577 and CVE-2026-27493, both of which have been assigned high CVSS scores of 9.4 and 9.5, respectively.
Details of the Critical Vulnerabilities
CVE-2026-27577 involves a sandbox escape in the expression compiler, as discovered by Eilon Cohen from Pillar Security. This flaw allowed for remote code execution due to a missing transformation in the AST rewriter, enabling authenticated expressions to bypass restrictions. Meanwhile, CVE-2026-27493, identified as a double-evaluation bug, could be exploited using n8n’s Form nodes for expression injection without requiring authentication or an n8n account.
Both vulnerabilities affected several versions of n8n, including those before 1.123.22 and specific versions in the 2.x series. Users are advised to upgrade to versions 2.10.1, 2.9.3, or 1.123.22 to ensure protection against these threats.
Mitigation Strategies and Recommendations
For CVE-2026-27577, n8n suggests restricting workflow creation and editing permissions to trusted users and deploying the platform in secure environments with limited OS permissions and network access. As a temporary measure against CVE-2026-27493, manually reviewing form nodes and disabling specific nodes through environment variables are recommended actions.
These vulnerabilities could potentially allow attackers to access the N8N_ENCRYPTION_KEY, leading to the decryption of sensitive stored credentials, such as AWS keys and database passwords. To mitigate these risks, n8n urges users to apply the recommended patches promptly.
Additional Security Concerns
Furthermore, n8n has patched two additional vulnerabilities—CVE-2026-27495 and CVE-2026-27497. Both involve code execution risks, with the former affecting the JavaScript Task Runner sandbox and the latter involving SQL queries within the Merge node. Suggested workarounds include using the external runner mode and disabling the Merge node through environment variables.
While there is no evidence of these vulnerabilities being exploited in the wild, maintaining updated installations is crucial for users to safeguard their systems from potential breaches.
In conclusion, addressing these security flaws promptly is essential to protecting sensitive data and ensuring the secure operation of the n8n platform. Users should follow the outlined mitigation strategies and keep their systems updated to mitigate potential risks effectively.