This week has highlighted a series of cybersecurity challenges that underscore the evolving threat landscape. Key areas of concern include network systems, cloud infrastructure, and AI models, all facing new forms of exploitation. The convergence of these threats points to a broader trend of vulnerabilities being leveraged across various sectors.
SD-WAN Zero-Day Exploitation
Cisco has reported a severe security vulnerability in its Catalyst SD-WAN Controller and Manager, known as CVE-2026-20127. This flaw, which has a CVSS score of 10.0, allows remote attackers to bypass authentication and gain administrative privileges. The issue, actively exploited since 2023, was first identified by the Australian Signals Directorate’s Cyber Security Centre. Cisco continues to monitor this sophisticated threat actor under the label UAT-8616.
AI Model Distillation Attacks
In recent developments, Anthropic has accused several Chinese AI companies of conducting large-scale distillation attacks to extract information from its models. This follows similar accusations by OpenAI, pointing to a growing trend where proprietary models are being targeted for unauthorized training data extraction. The controversy around these practices is further fueled by claims that Anthropic has itself engaged in large-scale data acquisition without proper consent, as highlighted by xAI CEO Elon Musk.
Cloud Security Breaches
Google has been working with industry partners to disrupt activities of the cyber espionage group UNC2814. This group has breached numerous organizations globally, utilizing a unique backdoor called GRIDTIDE that exploits Google Sheets API for covert data transmission. The telecommunications sector remains a primary target due to its access to sensitive information. Additionally, a new issue has been identified with Google Cloud API keys, which when improperly configured, can lead to unauthorized access to Gemini endpoints.
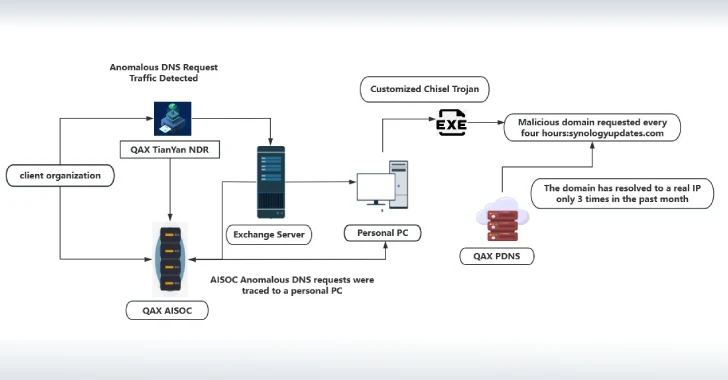
Furthermore, a newly identified threat cluster, UAT-10027, has been targeting U.S. educational and healthcare sectors. The campaign involves a novel backdoor named Dohdoor, using DNS-over-HTTPS for command-and-control operations. Although no data exfiltration has been confirmed, the attacks are believed to be financially motivated, as inferred from the targeted sectors.
Emerging Cyber Threats
Numerous vulnerabilities continue to surface, requiring immediate attention to prevent exploitation. This week’s critical CVEs include issues affecting Cisco Catalyst SD-WAN, Google Chrome, and HPE Telco Service Activator. Organizations are urged to review and address these vulnerabilities promptly to maintain system resilience against potential attacks.
The collective incidents observed this week illustrate the interconnected nature of modern cybersecurity threats. As adversaries enhance their methods, leveraging existing systems and processes, it becomes imperative for organizations to stay informed and proactive in their defense strategies.