The art of deception is not new, but its tactics have evolved, finding relevance in both art forgery and cybersecurity. In the 1960s, Elmyr de Hory became infamous for his skillful forgeries of master artists like Picasso and Matisse, duping collectors and museums alike. His methods, which deceived experts for decades, offer crucial insights into today’s cybersecurity challenges, where attackers similarly blend into legitimate environments.
The Rise of Cyber Mimicry
In a digital era characterized by imitation, cyberattackers employ sophisticated techniques to infiltrate systems. Just as de Hory used materials that mimicked authentic artworks, attackers today leverage trusted tools and credentials. According to CrowdStrike’s 2026 Global Threat Report, 81% of cyber incidents are now malware-free, which highlights the reliance on legitimate software to execute attacks. The ability to detect these camouflaged threats swiftly is essential to prevent significant damage.
Agentic AI and Network Fakery
Agentic AI represents a new frontier in cyber deception, creating fake identities and behaviors at scale. Much like de Hory’s network of art dealers, AI agents facilitate large-scale cyberattacks by generating exploit codes and scripts. These agents adapt to network behaviors, fine-tuning their activities to evade detection. They manipulate network traffic to blend in with legitimate spikes, making it challenging to identify their malicious intent.
Moreover, attackers exploit supply chains and cloud services by masquerading as trusted components. Malicious AI inserts harmful code into software updates, complicating the identification of exploit origins. This tactic was evident in the Shai Hulud v2 worm incident, where attackers modified software packages to gather sensitive credentials, exploiting trusted network pathways to propagate unnoticed.
Innovative Cloaking Techniques
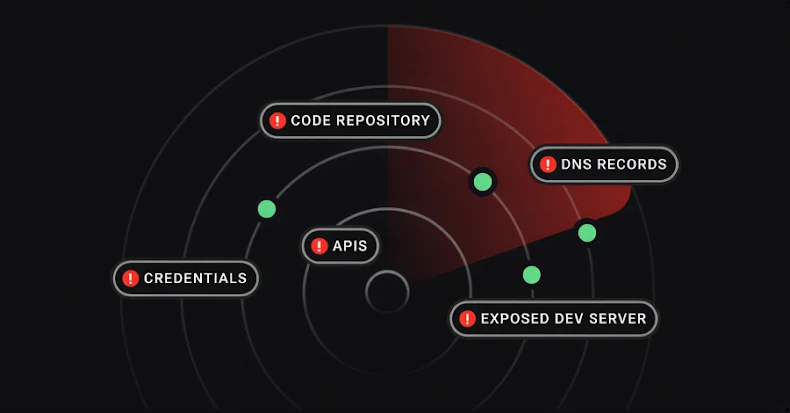
Modern attackers employ cloaking mechanisms, similar to de Hory’s strategic use of galleries to disguise his forgeries. By embedding malicious activities within legitimate protocol traffic, attackers mask their presence. Techniques include mismatching requests and replies to evade detection, allowing attackers to remain dormant within networks for extended periods.
Rogue infrastructures further complicate detection efforts. Attackers establish servers and domains that mimic legitimate entities, luring users into divulging credentials on fake platforms. Recent incidents involved phishing tactics that utilized fake email domains to redirect users to credential-harvesting sites, showcasing the parallels with de Hory’s meticulous forgery techniques.
Leveraging Network Detection and Response (NDR)
The parallels between art forgery and cyber deception underscore the importance of advanced detection technologies. Network Detection and Response (NDR) systems play a crucial role in identifying anomalies and behavioral patterns indicative of cyber threats. By analyzing network baselines and identifying deviations, NDR can expose impostors before they cause harm.
NDR’s ability to spot protocol inconsistencies and provide contextual metadata enhances threat detection capabilities. As attackers refine their methods, employing AI to scale their deceptions, security teams equipped with NDR and complementary tools can bolster their defenses and mitigate risks. Corelight’s Open NDR Platform exemplifies this approach, offering multi-layered detections to counter emerging threats effectively.
The evolving landscape of cyber deception demands vigilance and innovation. By learning from historical art forgeries, cybersecurity experts can better anticipate and counteract the sophisticated tactics employed by modern attackers.