Introduction
In March 2026, the Atos Threat Research Center (TRC) uncovered a sophisticated cyber campaign leveraging GitHub facades to target high-privilege enterprise accounts. This operation primarily aims at administrators, DevOps engineers, and security analysts, using advanced techniques such as SEO poisoning and decentralized command-and-control (C2) architectures. The campaign’s resilience and adaptability make it a formidable threat in the cybersecurity landscape.
Creative Distribution via GitHub Facades
The campaign employs a complex distribution strategy to avoid detection and takedowns. By using SEO poisoning, it ensures that malicious results appear prominently in search engines like Bing and Yahoo. Potential victims are directed to a primary GitHub repository that looks legitimate but contains no harmful code. Instead, it features a professional README file with a link to a secondary, hidden repository where the actual malware is hosted. This separation allows the threat actors to maintain their search engine presence while quickly rotating the malicious repositories if flagged.
Targeted Impersonation of Administrative Tools
Adversaries impersonate essential administrative tools to profile and compromise high-privilege users. These fake tools, such as PsExec and Sysmon, are used by individuals with elevated permissions. Once installed, the malware provides attackers with extensive access, potentially enabling lateral movement within the organization. This strategic impersonation capitalizes on the trust placed in familiar utilities to infiltrate enterprise environments.
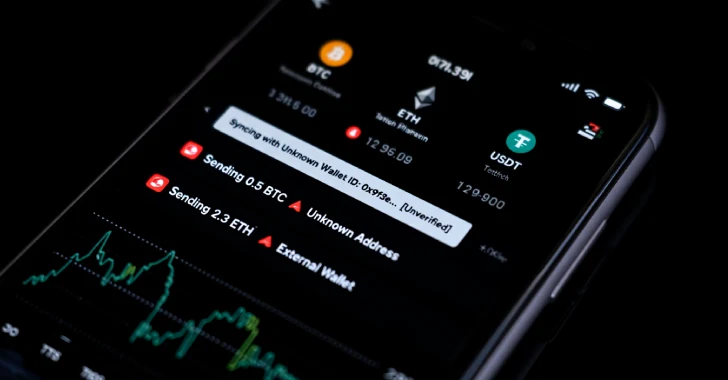
Decentralized C2 via Ethereum Blockchain
One of the most innovative aspects of this campaign is its use of Ethereum blockchain for C2 communication. Instead of relying on static IP addresses or domains, which are susceptible to blocklisting, the malware queries a smart contract on the Ethereum blockchain. This method allows the dynamic retrieval of live C2 server addresses, offering the adversaries remarkable resilience. The ability to modify server locations via blockchain transactions ensures continuous and uninterrupted control over infected systems.
Conclusion
The EtherRAT campaign represents a significant threat due to its innovative use of GitHub facades and blockchain technology. By targeting high-privilege accounts and employing decentralized C2 infrastructure, the attackers enhance their ability to remain undetected and operational. Organizations must stay vigilant and implement robust security measures to defend against such advanced threats. Continuous monitoring and education of IT personnel are essential to mitigate the risks associated with this campaign.