On Wednesday, Google announced a successful collaboration with industry partners to dismantle the infrastructure of a suspected China-linked cyber espionage group known as UNC2814. This entity has been implicated in breaching at least 53 organizations across 42 nations.
Background of UNC2814 Operations
The cyber group, UNC2814, has a notorious history of targeting governmental and telecommunication sectors globally, particularly across Africa, Asia, and the Americas. According to a joint report by Google’s Threat Intelligence Group and Mandiant, this group employs sophisticated methods to blend malicious traffic with legitimate communications using software-as-a-service (SaaS) applications as command-and-control (C2) infrastructure.
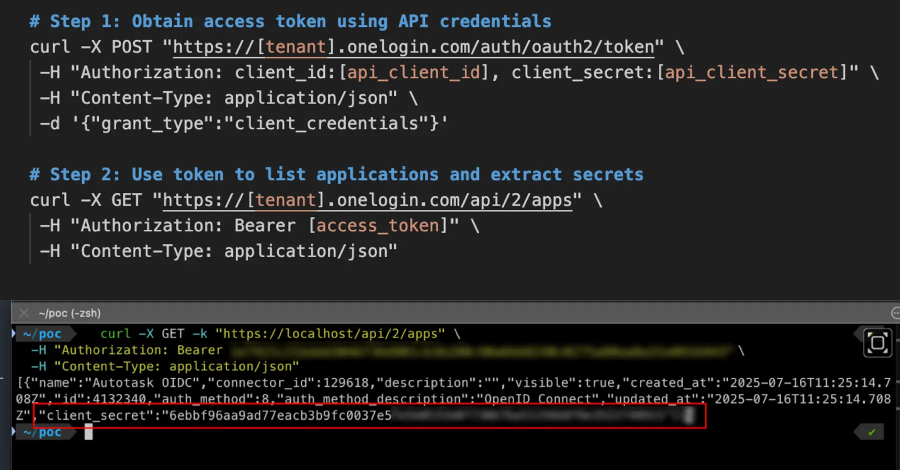
Since 2017, UNC2814 has been observed using API calls to mask their operations, a tactic that significantly complicates detection by cybersecurity defenses. The core of their operation revolves around a backdoor known as GRIDTIDE, which exploits the Google Sheets API to facilitate communication and data transfer under the guise of normal operations.
Technical Insights into GRIDTIDE
GRIDTIDE is a C-based malware designed to perform tasks such as file upload and download, as well as executing arbitrary shell commands. The initial access method of UNC2814 remains under investigation, but they are known to exploit web servers and edge systems to infiltrate networks.
Once inside a network, the group uses service accounts to move laterally, employing SSH for access and living-off-the-land binaries to maintain persistence and escalate privileges. A notable technique involves creating a service for the malware on Linux systems to ensure continuous operation.
Counteractions by Google
In response to the threat, Google terminated all Google Cloud Projects under the control of UNC2814 and disabled their infrastructure. Access to accounts and Google Sheets API calls used for C2 purposes was also cut off. Google described the campaign as one of the most significant and impactful they have encountered in recent years.
The cessation of UNC2814’s activities is a critical step in protecting the telecommunications and government sectors, which remain vulnerable to such sophisticated cyber threats. Google’s actions demonstrate the importance of rapid response and collaboration in mitigating the risks posed by state-sponsored cyber espionage.
The broader implications of this event highlight ongoing vulnerabilities at network edges, often exploited by threat actors due to insufficient malware detection capabilities and direct network access. The persistent nature of UNC2814’s efforts underscores the need for continuous vigilance and advanced security measures to protect against similar threats in the future.