An alarming phishing operation is currently targeting French-speaking businesses by utilizing counterfeit resumes to introduce cryptocurrency miners and information-stealing malware into systems. This campaign, revealed by Securonix researchers Shikha Sangwan, Akshay Gaikwad, and Aaron Beardslee, employs heavily obfuscated VBScript files that masquerade as resume documents sent via phishing emails.
Phishing Tactics and Attack Methodology
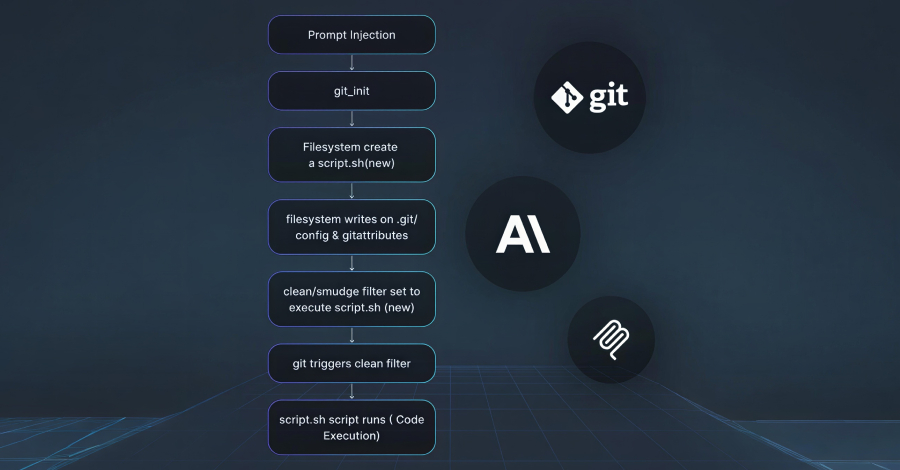
The attack, codenamed FAUX#ELEVATE, is notable for exploiting legitimate services and infrastructures for malicious purposes. The attackers use Dropbox to stage payloads, Moroccan WordPress sites for hosting command-and-control configurations, and mail[.]ru SMTP servers to extract stolen credentials and files. This strategy exemplifies a ‘living-off-the-land’ approach, allowing attackers to bypass defenses and infiltrate targets discreetly.
Once executed, the script performs various checks to avoid sandbox detection and initiates a persistent User Account Control loop, urging users to execute it with elevated privileges. Despite its large size of 9.7MB, the script contains only a small fraction of executable code, with the remainder being filled with irrelevant comments to obfuscate its intent.
Advanced Techniques for Credential Theft
After gaining administrative access, the malware swiftly disables security features and conceals its presence by altering Microsoft Defender settings and disabling User Account Control through registry tweaks. It retrieves two password-protected 7-Zip archives from Dropbox: one containing executables for data theft and cryptocurrency mining, and the other equipped with tools for maintaining persistence and cleanup.
The attackers employ components like the ChromElevator project to bypass encryption protections and extract data from browsers. Additional tools include a VBScript for stealing Mozilla Firefox credentials and another for exfiltrating desktop files. An XMRig cryptocurrency miner, activated by a configuration from a compromised site, and a Windows kernel driver to enhance CPU mining capabilities are also used in the attack.
Implications and Future Outlook
The exfiltration of browser data is executed via two mail[.]ru accounts with identical passwords, targeting another email managed by the threat actors. Following the completion of credential theft and data exfiltration, the operation initiates a thorough cleanup to minimize its forensic footprint, leaving only the miner and Trojan components behind.
Securonix highlights the FAUX#ELEVATE campaign as a sophisticated, multi-stage operation that seamlessly combines several advanced techniques. The rapid execution, completing the infection chain in about 25 seconds, and the selective targeting of enterprise machines, make this campaign particularly perilous for corporate security teams. As businesses grapple with such threats, enhancing vigilance and implementing robust security protocols remain crucial to safeguard critical data and resources.