Microsoft has introduced a revolutionary artificial intelligence (AI) system named MDASH, designed to streamline the identification and resolution of software vulnerabilities. This advanced system is part of a limited private preview, with select customers engaging in its trial phase.
MDASH: A New Approach to Vulnerability Discovery
The MDASH system, which stands for multi-model agentic scanning harness, employs a unique model-agnostic framework. It utilizes a multitude of specialized AI agents to autonomously detect and validate vulnerabilities in complex systems like Windows. According to Taesoo Kim, Microsoft’s vice president of agentic security, this system orchestrates over 100 AI agents that collaborate to identify and confirm exploitable defects in software.
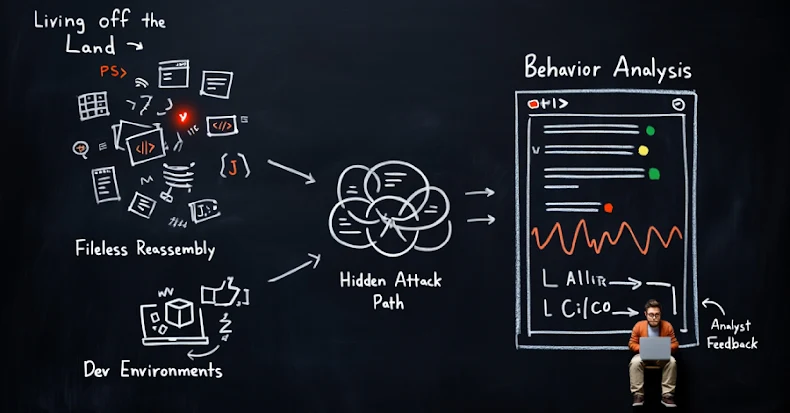
Unlike traditional single-model methods, MDASH integrates various AI models, creating a comprehensive approach to vulnerability discovery. These agents work through a structured process that begins with source code analysis, focusing on threat modeling and attack surface identification.
How MDASH Operates
MDASH functions through a series of methodical stages. Initially, the system analyzes the source code to develop a threat model and identify potential attack vectors. It then employs specialized “auditor” agents to scan code paths for vulnerabilities, followed by “debater” agents that verify these findings, and finally, it validates the vulnerabilities through a proving stage.
The system utilizes a range of state-of-the-art (SOTA) and distilled models for reasoning and validation purposes. Microsoft emphasizes that the interaction between differing models enhances the credibility of findings, as discrepancies can indicate higher confidence in identified vulnerabilities. The architecture of MDASH also allows for adaptability across different model generations, increasing its effectiveness and longevity.
Impact of MDASH on Windows Security
MDASH has already demonstrated its efficacy by detecting 16 vulnerabilities addressed in Microsoft’s latest Patch Tuesday update. These vulnerabilities affect the Windows networking and authentication infrastructure, including critical flaws like CVE-2026-33824 and CVE-2026-33827, which could potentially enable remote code execution.
CVE-2026-33824 involves a double-free vulnerability in “ikeext.dll,” posing a significant risk of attack via specially crafted packets. Meanwhile, CVE-2026-33827 is a race condition flaw in Windows TCP/IP that can be exploited using crafted IPv6 packets.
The introduction of MDASH coincides with other AI-driven cybersecurity initiatives such as Anthropic’s Project Glasswing and OpenAI Daybreak. These developments signify a shift towards AI-powered solutions for proactive vulnerability management, emphasizing the strategic importance of comprehensive agentic systems over isolated models.
In conclusion, Microsoft’s MDASH represents a significant advancement in software security, highlighting the growing role of AI in safeguarding digital infrastructure. As AI continues to evolve, its application in cybersecurity is set to become a cornerstone of enterprise-level defense strategies.