A newly identified vulnerability in the Linux kernel, named Fragnesia, allows local users without privileges to gain root access, posing a significant threat to system security. This flaw is notable for not requiring a race condition, enhancing its reliability compared to similar exploits.
Discovery and Nature of Fragnesia
Fragnesia was discovered by William Bowling of the V12 security team. It is part of a growing category of serious kernel vulnerabilities that challenge existing Linux security protocols. This particular bug is part of the Dirty Frag class, related to the well-known Dirty Pipe and Copy Fail bugs, but it targets a different logic flaw in the Linux XFRM ESP-in-TCP subsystem.
The vulnerability exploits a kernel error where it fails to recognize shared fragments during the coalescing of socket buffers, inadvertently corrupting memory it should not access.
Mechanism of the Exploit
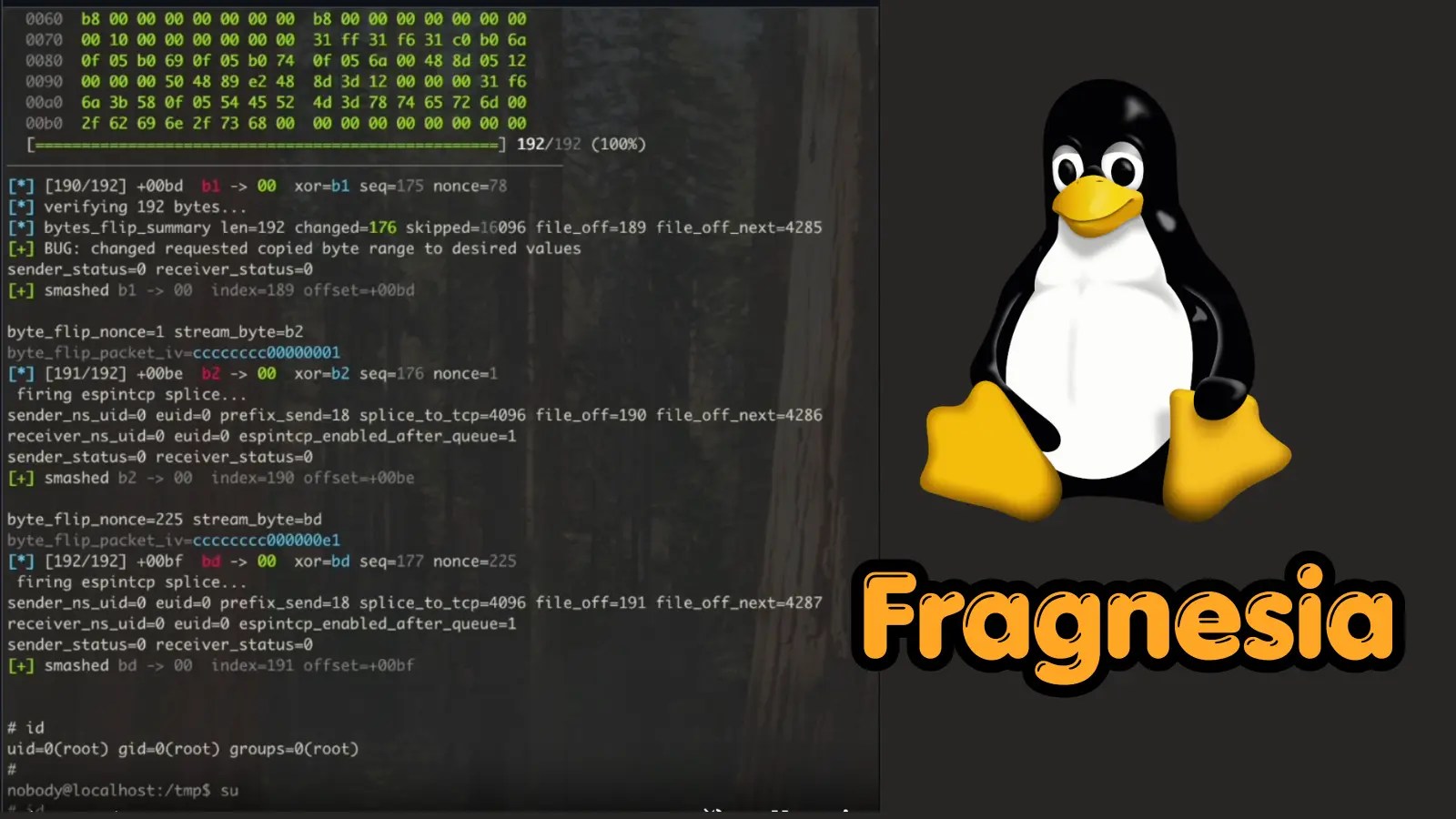
Fragnesia leverages a logic flaw in the handling of ESP-in-TCP ULP mode by the kernel. When a TCP socket shifts to espintcp ULP after data is already queued, the kernel erroneously processes the pages as ESP ciphertext. This results in an AES-GCM keystream byte being XORed into a read-only file’s kernel page cache without needing a race condition.
The exploit is executed by constructing a 256-entry lookup table of possible keystream bytes, allowing an attacker to alter any byte in a cached file by selecting the right nonce. This method enables the overwriting of the first 192 bytes of /usr/bin/su with a malicious ELF stub that elevates privileges and opens a root shell.
Impact and Mitigation Strategies
All Linux kernels affected by Dirtyfrag are susceptible, specifically those before May 13, 2026. While a patch has been submitted, systems remain at risk until it is applied. Administrators should immediately remove the vulnerable ESP modules using:
- rmmod esp4 esp6 rxrpc
- printf ‘install esp4 /bin/falseninstall esp6 /bin/falseninstall rxrpc /bin/false’ > /etc/modprobe.d/dirtyfrag.conf
It’s crucial to flush the page cache to prevent persistence of the exploit, using echo 1 | tee /proc/sys/vm/drop_caches or rebooting the system. A proof-of-concept is publicly available on GitHub, emphasizing the urgency for immediate action by organizations to patch affected systems.
Stay updated on this and other security issues by following us on platforms like Google News, LinkedIn, and X.