Microsoft has issued a warning about phishing campaigns that exploit the U.S. tax season to steal credentials and spread malware. These cyberattacks are leveraging the urgency of tax-related communications to trick individuals and professionals into engaging with malicious emails disguised as refund notices or filing reminders.
Phishing Campaigns Targeting Tax Professionals
The latest threats are not just aimed at individuals but also target accountants and other professionals who routinely handle sensitive financial information. By posing as legitimate tax-related communications, these phishing efforts deceive recipients into interacting with harmful attachments or links.
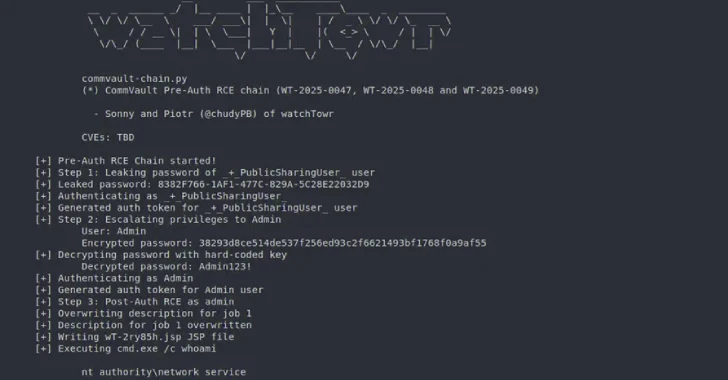
Some campaigns employ Phishing-as-a-Service (PhaaS) platforms to create fake web pages, while others install legitimate remote monitoring tools like ConnectWise ScreenConnect, enabling attackers to maintain access to compromised systems.
Details of the Cyber Threats
A variety of tactics are being used in these campaigns. For instance, CPA-themed emails are being used to lead victims to phishing sites through the Energy365 PhaaS kit. In another case, QR codes and W2 forms are employed to trick users into entering credentials on fake Microsoft 365 login pages.
Tax-themed domain names are also being utilized to lure users into downloading malware-laden files. One sophisticated scheme involves impersonating the IRS with emails that claim irregular tax returns have been filed, prompting users to download a fake ‘IRS Transcript Viewer’ to access their systems.
Impact and Protective Measures
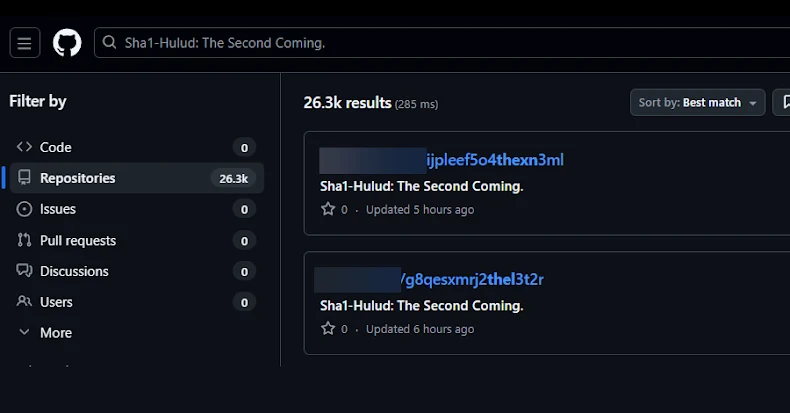
On February 10, 2026, Microsoft observed a large-scale phishing campaign affecting over 29,000 users across 10,000 organizations. The majority of these attacks were concentrated in the U.S., targeting sectors like financial services, technology, and retail.
To protect against these threats, Microsoft recommends implementing two-factor authentication, monitoring email traffic, and blocking access to malicious domains. The rise in remote monitoring tool misuse highlights the need for organizations to remain vigilant and audit for unauthorized use.
The increase in the adoption of RMM tools by cybercriminals underscores the necessity for enhanced security measures and awareness. As these tools are often used legitimately, distinguishing between authorized and malicious usage is critical.