Microsoft has raised an alert regarding a sophisticated phishing scheme that capitalizes on OAuth URL redirection to evade typical email and browser defenses. This warning, issued on Monday, highlights a targeted attack on governmental and public-sector entities designed to reroute victims to attacker-operated sites without compromising their authentication tokens. The core of this threat lies in exploiting OAuth’s native features, not software weaknesses or credential theft.
Exploiting OAuth Redirection
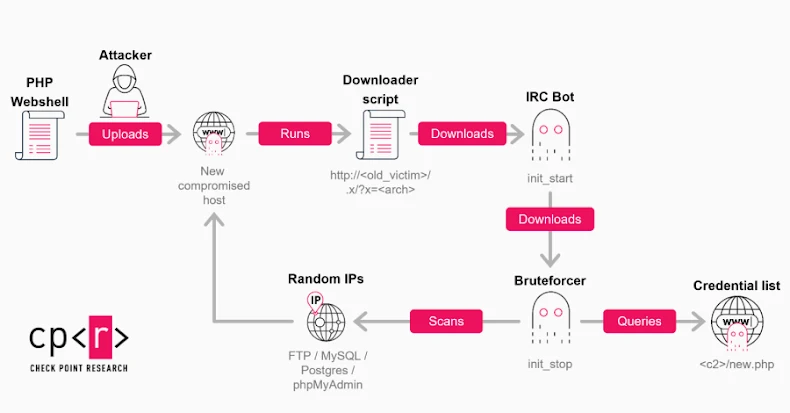
The phishing strategy manipulates OAuth’s legitimate redirection capabilities to deceive users. Attackers craft URLs associated with well-known identity providers such as Entra ID or Google Workspace. These URLs, though appearing harmless, ultimately guide users to malicious pages under the attackers’ control. This method involves creating a deceptive application within a compromised tenant, with the redirect URL leading to a malware-hosting rogue domain.
Once the phishing link is distributed, recipients are tricked into authenticating with the malicious app via an invalid scope. This results in their devices unknowingly downloading malware, often packaged in ZIP files. When unpacked, these files initiate PowerShell commands, DLL sideloading, and potentially pre-ransomware activities.
Technical Breakdown of the Attack
The ZIP archive includes a Windows shortcut (LNK) file that triggers a PowerShell command upon opening. The command conducts host reconnaissance, while the LNK file extracts an MSI installer, which deploys a decoy document and sideloads a harmful DLL, specifically ‘crashhandler.dll,’ using the legitimate ‘steam_monitor.exe’ binary. This DLL then decrypts and executes ‘crashlog.dat,’ establishing a connection to an external command-and-control server.
Phishing emails are crafted with themes like e-signature requests, Teams recordings, and financial or political issues to lure users. These emails, disseminated via mass-emailing tools or custom Python and Node.js solutions, embed links either in the email itself or within attached PDFs. To enhance credibility, attackers encode the target’s email address within the state parameter, populating it automatically on the phishing site.
Preventive Measures and Mitigation
Microsoft’s investigation has led to the removal of several malicious OAuth applications. To mitigate such risks, organizations are urged to restrict user consents, regularly audit application permissions, and eliminate unnecessary or excessively privileged apps. While some attacks deliver malware, others redirect users to phishing frameworks like EvilProxy, which intercept credentials and session cookies through adversary-in-the-middle tactics.
The ongoing challenge of protecting against such sophisticated phishing attacks underscores the importance of robust cybersecurity measures, particularly in sectors handling sensitive information. As threat actors continue to evolve their techniques, constant vigilance and proactive defense strategies are crucial for safeguarding organizational assets.